Exam Details
Exam Code
:1D0-610Exam Name
:CIW Web Foundations AssociateCertification
:CIW CertificationsVendor
:CIWTotal Questions
:172 Q&AsLast Updated
:Mar 29, 2025
CIW CIW Certifications 1D0-610 Questions & Answers
-
Question 71:
Violating a copyright or trademark is an example of what type of prosecutable crime?
A. Infringement
B. Plagiarism
C. Trade secrets
D. Non-disclosure
-
Question 72:
Which code is best for embedding video into an HTML5 page?
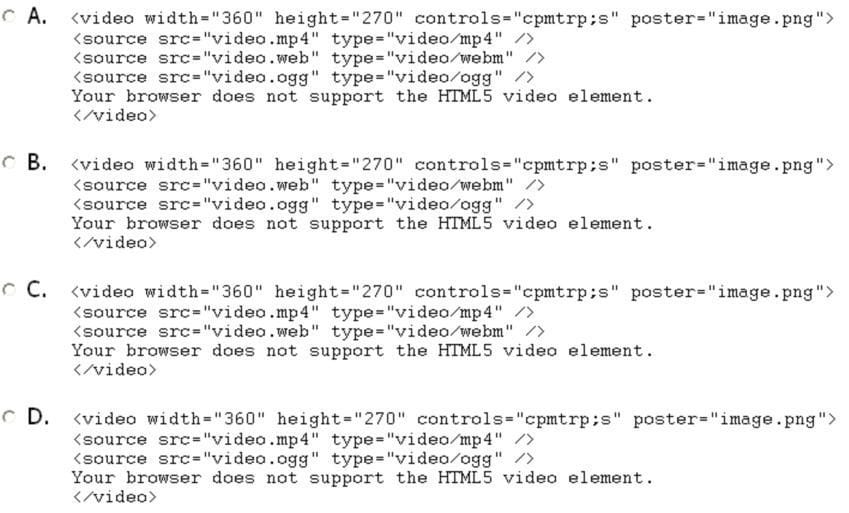
A. Option A
B. Option B
C. Option C
D. Option D
-
Question 73:
You have been asked to design and develop a Web site for a retirement community. What can you do to help make the site accessible to the elderly?
A. Comply with the latest scripting standards.
B. Comply with ICANN's accessibility standards.
C. Comply with WAI's Web Content Accessibility Guidelines.
D. Comply with IETF's Web Content Accessibility Guidelines.
-
Question 74:
To restore a backup file on a Windows-based computer, you:
A. Use the Disk Management utility in the Microsoft Management Console (MMC)
B. Use the Backup And Restore utility in the Control Panel.
C. Use Device Manager in the Control Panel.
D. Extract the backed-up file.
-
Question 75:
Security attacks can vary greatly. Which type of attack is characterized as an attempt to trick an individual into revealing confidential or private information?
A. Trojan
B. Spoofing
C. Man in the middle
D. Social engineering
-
Question 76:
Marsha has been hired by XYZ, Inc., to update the company Web site. Marsha discovers that the existing Web pages were structured using tables. Marsha needs to explain to XYZ why the Web site needs to be recoded in HTML5 with CSS controlling the structure of the document. What is the most important reason for using HTML5 and CSS?
A. The updates will increase user traffic to the site.
B. The updates will improve the overall look and feel of the Web site.
C. The Web site can be interpreted by any HTML5-compliant browser, including mobile devices.
D. The Web site will rank higher in many search engines results, as long as the search engine bot recognizes the code.
-
Question 77:
Philip creates a Web form in HTNL5, but the data will not process. He has the method attribute included in the
-
Question 78:
When comparing IPv4 to IPv6, which of the following is an advantage of the IPv6 network addressing scheme?
A. Larger address space
B. Shorter address space
C. High dependence on network routers
D. Fast and unencrypted network transmissions
-
Question 79:
You are a small-business owner and would like to encourage employees to bring their own devices (BYOD) to work. Which of the following can help reduce the security risks associated with a BYOD implementation?
A. Expense accounts
B. Acceptable use policy
C. End user license agreement
D. In-house device maintenance
-
Question 80:
Which Web-based validation tool is used to validate Cascading Style Sheets (CSS)?
A. www.cynthiasays.com
B. www.validator.w3.org
C. www.vischeck.com
D. www.jigsaw.w3.org
Related Exams:
1D0-435
CIW JavaScript Fundamentals1D0-437
CIW PERL FUNDAMENTALS1D0-510
CIW v5 Founfations1D0-520
CIW v5 Site Designer1D0-525
CIW v5 E-Commerce Designer1D0-541
CIW v5 Database Design Specialist1D0-571
CIW v5 Security Essentials1D0-610
CIW Web Foundations Associate1D0-61A
CIW Internet Business Associate1D0-61B
CIW Site Development Associate
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CIW exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1D0-610 exam preparations and CIW certification application, do not hesitate to visit our Vcedump.com to find your solutions here.