Exam Details
Exam Code
:1Z0-052Exam Name
:Oracle Database 11g: Administration Workshop ICertification
:Oracle CertificationsVendor
:OracleTotal Questions
:285 Q&AsLast Updated
:Mar 25, 2025
Oracle Oracle Certifications 1Z0-052 Questions & Answers
-
Question 121:
The instance abnormally terminates because of a power outage. Which statement is true about redo log files during instance recovery?
A. Inactive and current redo log files are required to accomplish recovery
B. Online and archived redo files are required to accomplish instance recovery
C. All redo log entries after the last checkpoint are applied from redo log files to data files
D. All redo log entries recorded in the current log file until the checkpoint position are applied to data files
-
Question 122:
View the Exhibit to examine the output for the CROSSCHECK BACKUP command.
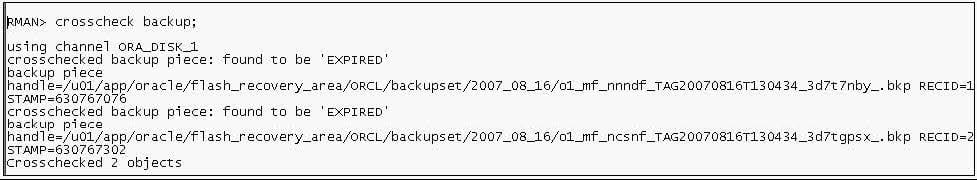
Which statement is true about the output of the command?
A. The backup piece is expired as the new backup is available
B. The backup piece is expired because the operating-system file was not found
C. The backup piece is expired because the retention period for the backup has expired
D. The backup piece is expired because the backup set to which it belongs is not complete
-
Question 123:
Examine the values for the following initialization parameters:
FAST_START_MTTR_TARGET=0
LOG_CHECKPOINT_INTERVAL=0
Which two will be the implications of these values in your database? (Choose two.)
A. The SGA advisor will be disabled
B. The MTTR advisor will be disabled
C. Automatic checkpoint tuning will be disabled
D. Checkpoint information will not be written to the alert log file
-
Question 124:
Automatic Shared Memory Management (ASMM) has been enabled for your database instance. The initialization parameters for the components that are managed by ASMM are not set. After observing the effects of ASMM, you executed the following command:
SQL> ALTER SYSTEM SET DB_CACHE_SIZE = 100M;
Which statement is true in this scenario?
A. The minimum memory size for the database buffer cache is set to 100 MB.
B. The maximum memory size that can be obtained by the database buffer cache during ASMM is set to 100 MB.
C. The minimum memory size allocated for a server process in the database buffer cache in dedicated mode is set to 100 MB.
D. The maximum memory size from the database buffer cache that can be released for dynamic distribution during ASMM is set to 100 MB.
-
Question 125:
You used the IMMEDIATE option to shutdown your database instance. Consider the steps that will be performed later when you open the database:
1.
SGA is allocated.
2.
Control file is read.
3.
Redo log files are read.
4.
Instance recovery is started.
5.
Background processes are started.
6.
Data files are checked for consistency.
7.
Server parameter file or the initialization parameter file is read. Which option has the correct order in which these steps occur?
A. 7, 1, 5, 2, 3, 6, 4
B. 1, 5, 7, 2, 3, 6; step 4 is not required
C. 7, 1, 5, 2, 3, 6 step 4 is not required
D. 1, 2, 3, 5, 6, 4; step 7 is not required
-
Question 126:
Your database is configured in shared server mode. However, your senior DBA asks you to modify the
value of the PRIVATE_SGA limit in the profile of the users.
What could be the reason for this?
A. To limit the User Global Area (UGA) memory allocated to a session from the SGA
B. To limit the amount of memory to be used for the dispatcher queue of a session in SGA
C. To limit the amount of memory to be used for the request pool in System Global Area (SGA)
D. To control the amount of memory allocated in SGA for the local variables for each shared server process
-
Question 127:
See the Exhibit:
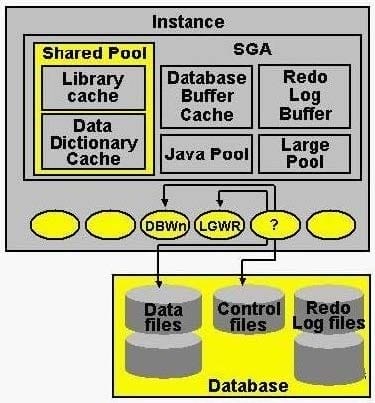
Identify the component marked with a question mark:
A. Checkpoint (CKPT) B. Process Monitor (PMON)
C. Archiver Processes (ARcn)
D. Recoverer Process (RECO)
E. Memory Manager Process (MMAN)
-
Question 128:
Note the following points describing various utilities in Oracle Database 11g: Which point describes the Oracle Data Pump utility?
1.
It enables the transfer of data from one database to another
2.
It provides a complete solution for the backup, restoration and recovery needs of the entire database
3.
It enables the loading of data from an external file into tables of an Oracle Database
4.
It provides a tape backup management for the Oracle ecosystem
A. 1
B. 2
C. 3
D. 4
E. 1 and 3
F. 1, 2, 3 and 4
-
Question 129:
You want to create a role to meet these requirements:
1.
The role is to be protected from unauthorized usage.
2.
The password of the role is not to be embedded in the application source code or stored in a table. Which method would you use to restrict enabling of such roles?
A. Create the role with external authentication.
B. Create the role as a secure application role.
C. Create the role as a password-protected role.
D. Create a role and use Fine-Grained Access Control (FGAC) to secure the role.
-
Question 130:
Which two statements are true about setting the FAST_START_MTTR_TARGET initialization parameter to a nonzero value? (Choose two.)
A. The MTTR advisor will be disabled
B. Automatic checkpoint tuning will be enabled
C. The value for the LOG_CHECKPOINT_INTERVAL initialization parameter will be override the value for FAST_START_MTTR_TARGET
D. The time taken to recover the instance after the crash is always exactly the same as the value given for the FAST_START_MTTR_TARGET initialization parameter
Related Exams:
1Z0-020
Oracle8i: New Features for Administrators1Z0-023
Architecture and Administration1Z0-024
Performance Tuning1Z0-025
Backup and Recovery1Z0-026
Network Administration1Z0-034
Upgrade Oracle9i/10g OCA to Oracle Database OCP1Z0-036
Managing Oracle9i on Linux1Z0-041
Oracle Database 10g: DBA Assessment1Z0-052
Oracle Database 11g: Administration Workshop I1Z0-053
Oracle Database 11g: Administration II
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Oracle exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1Z0-052 exam preparations and Oracle certification application, do not hesitate to visit our Vcedump.com to find your solutions here.