Exam Details
Exam Code
:1Z0-574Exam Name
:Oracle IT Architecture Release 3 EssentialsCertification
:Oracle CertificationsVendor
:OracleTotal Questions
:176 Q&AsLast Updated
:Mar 26, 2025
Oracle Oracle Certifications 1Z0-574 Questions & Answers
-
Question 151:
Which of the following interactions does not occur as part of a web-based single sign-on scenario?
A. A gateway, deployed In the Web Server, intercepts requests destined for protected resource
B. The user is prompted for login credentials when a protected resource is accessed and the user has not (recently) logged In.
C. Credentials are passed to the application for validation.
D. Authorization checks are optionally performed before the user is permitted access to the application.
E. A cookie is returned, which is used to permit access to other protected resources in that domain
-
Question 152:
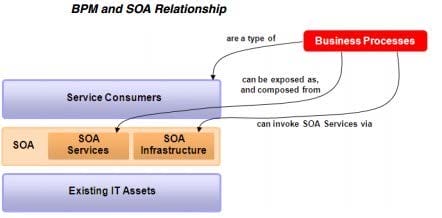
BPM and SOA are frequently combined to provide greater business value than either technology provides independently. Which statements are true with regard to combining the BPM Technology Perspective and SOA Technology Perspective?
A. A Business Process may invoke a SOA Services to perform specific tasks within the process flow.
B. A Business Process may be exposed as a SOA Service.
C. When combining SOA and BPM, all the tasks within a Business Process are accomplished via Services.
D. A Business Process may invoke an SOA Service, but an SOA Service cannot invoke a Business Process.
E. Every business Process is exposed as a SOA Service.
-
Question 153:
Which one of the following types of access control should be used when access to a resource is dependent upon specific qualities of the user, for example, membership status, frequency of purchases, or level of certification?
A. role-based access control
B. rule-based access control
C. discretionary access control
D. content-dependent access control
E. attribute-based access control
-
Question 154:
The Mediation Layer in the Logical View of the Service-Oriented Integration architecture provides several capabilities. Which of the following are capabilities provided by the Mediation Layer?
A. enrichment - adding data elements to a data entity to give the entity increased Information
B. routing - sending the client request to the appropriate provider (s) based on some criteria
C. message transformation - converting the request message format to a different message form, appropriate for the provider
D. choreography - defining the messages that flow back and forth between systems that are participating in a business process
E. protocol mediation - converting a client request from one protocol to a different protocol used by provider
-
Question 155:
IT Strategies from Oracle (ITSO) Includes multiple Enterprise Technology Strategies. Why are there multiple Enterprise Technology Strategies within ITSO?
A. Each enterprise Technology Strategy documents the architecture for a particular Oracle product.
B. Each Enterprise Technology Strategy provides Oracle product details that are important to the technology strategy.
C. An Enterprise Technology Strategy provides detailed guidance on deploying the oracle products that are important to the technology strategy.
D. Each Enterprise technology Strategy provides a reference architecture and practical guidance to achieve success with specific new technology.
E. Each Enterprise Technology Strategy provides industry-vertical reference architecture and practical guidance.
-
Question 156:
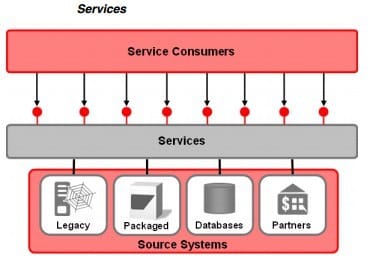
Service Oriented Integration (SOI) exposes capabilities from existing source systems. Which statement best describes the Impact SOI has on existing source systems?
A. Because SOI exposes only existing capabilities, any new required functionality will be implemented by modifying the existing source systems.
B. No modifications to existing source systems are allowed because SOA Services expose all the necessary capabilities from the source systems.
C. Modifications to existing source systems should be avoided, but may be necessary to support SOA Service creation.
D. To support SOA Service connectivity, modifications will be required for the existing source systems incorporated into the SOI architecture.
-
Question 157:
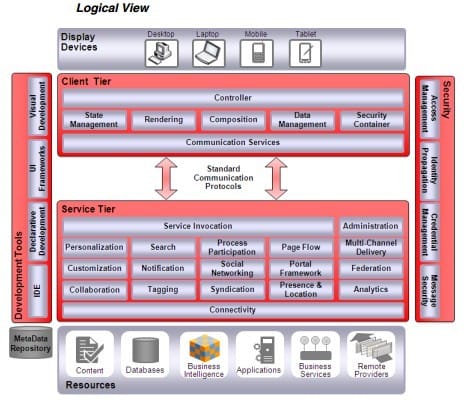
Where are the components of the client tier of the ORA UI logical architecture hosted?
A. on the transcoding engine
B. on the web server
C. on the display device
D. some components on the web server and some on the display device
-
Question 158:
Identify the true statements in the following list.
A. The core components of the ORA UI Logical view are grouped into the client tier and the server tier.
B. The components of the ORA UI Logical view are model, view, and controller.
C. The core components of the ORA UI Logical view are grouped into thedisplaytier and theresourcestier.
D. In addition to the core components, the Logical view also includes security, communication protocols, and development tools.
-
Question 159:
Interface elements are an important part of modular programming for UI. Which of the following statements is true with regard to Interface elements?
A. Interface elements are always provided as proprietary packages of widgets from device vendors and third parties.
B. There is a wide variety of interface elements that can be developed once and used repeatedly in various user-interface designs.
C. Interface elements are highly standardized and, once developed for one device, they are sufficiently portable to be reused on other devices without modification.
D. Interface elements implement application-specific functionality and are therefore rarely reusable across multiple applications.
-
Question 160:
Which statement best describes the relationship between Oracle Reference Architecture (ORA) and the Oracle products?
A. ORA describes the architecture built in to the Oracle products.
B. ORA describes the architecture underlying the Oracle Fusion Applications.
C. ORA describes a product-agnostic architecture and then maps the Oracle products onto the architecture.
D. ORA describes an architecture thatis exclusively based on Oracle products.
Related Exams:
1Z0-020
Oracle8i: New Features for Administrators1Z0-023
Architecture and Administration1Z0-024
Performance Tuning1Z0-025
Backup and Recovery1Z0-026
Network Administration1Z0-034
Upgrade Oracle9i/10g OCA to Oracle Database OCP1Z0-036
Managing Oracle9i on Linux1Z0-041
Oracle Database 10g: DBA Assessment1Z0-052
Oracle Database 11g: Administration Workshop I1Z0-053
Oracle Database 11g: Administration II
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Oracle exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1Z0-574 exam preparations and Oracle certification application, do not hesitate to visit our Vcedump.com to find your solutions here.