Exam Details
Exam Code
:1Z0-574Exam Name
:Oracle IT Architecture Release 3 EssentialsCertification
:Oracle CertificationsVendor
:OracleTotal Questions
:176 Q&AsLast Updated
:Mar 26, 2025
Oracle Oracle Certifications 1Z0-574 Questions & Answers
-
Question 51:
What one the three primary concerns that developers following this architecture should strive to conform to?
A. Personalization
B. Modular development
C. Internationalization
D. Localization
E. The Model View-Controller (MVC) pattern
F. Federation
-
Question 52:
What does ORA Engineering refer to as Round-Trip Engineering?
A. the ability to effectively perform both forward and reverse engineering to seamlessly transform assets in either direction of the life cycle
B. the ability to derive artifacts from a previous life-cycle activity
C. the ability to generate artifacts backwardsinthe life cycle
D. a continuous improvement process in the SDLC that allows the assets to be produced at various stages of the life cycle with a feedback loop from operations to requirement analysis.
-
Question 53:
A customer has two separate lines of business and each has its own unique resources that are controlled independently. The customer wants to provide a single user interface at the enterprise level that, at least from the user's perspective, unifies the separate lines of business and presents a single consistent view. What is the most suitable architectural arrangement for such a federated deployment?
A. The enterprise implements full client stack and part of the service stack while each LoB deploys the remaining part of the service tierin order to expose uniform interface elements.
B. The client tier assimilates the data from the resource stack of each line of business.
C. The enterprise implements full client and service stacks while each LoB deploys a partial service. sufficient to expose uniform interface elements.
D. The client tier assimilates the data from the service stack of each line of business.
-
Question 54:
Which of the following statements are true about asymmetric key encryption?
A. It uses a pair of keys, one public and one private, that are unique and mathematically linked.
B. It uses one key that is shared by both parties in the data exchange.
C. It is faster than symmetric key encryption.
D. It can be used in conjunction with symmetric key encryption in order to securely share a common encryption key.
E. It can be used to produce and verify digital signatures.
-
Question 55:
Which of the following statements best describes the ideal role of an application owner with respect to defining application security?
A. The application owner must become knowledgeable about security risks, threats, classifications, and policies in order to define security requirements for his or her applications. The more on owner learns about security, the more secure his or her applications will become.
B. The application owner should hire a security expert to define security requirements for his or herapplications, based on current Industry best practices. Actively implementing the latest trends will best ensure a secure application environment.
C. The application owner should recommend adherence to common established practices for assessments, classifications, architecture, and policies that have been defined, and are actively maintained, by security experts across the organization. Deviations may be necessary, butapplication owners should strive to be consistent with best practices that have been adopted by the organization.
D. The application owner, whenever possible, should elect to deploy applications into a public cloud computing environment. Doing so effectivelydelegatesresponsibility and accountability of concerns to another company. The owner doesn't need to be concerned with security as long as the cloud provider has been certified.
-
Question 56:
Which of the following does Policy Management Compliance refer to?
A. a desired behavior, andis associated with one or more Infrastructure components
B. the demonstration and enforcement of regulatory standards,industry standards, internal best practices
C. a set of processes through which management identifies, analyzes and, where necessary, responds appropriately to risks
D. a management approach to direct and control the entire organization by using a combination of management information and hierarchical management control structures
-
Question 57:
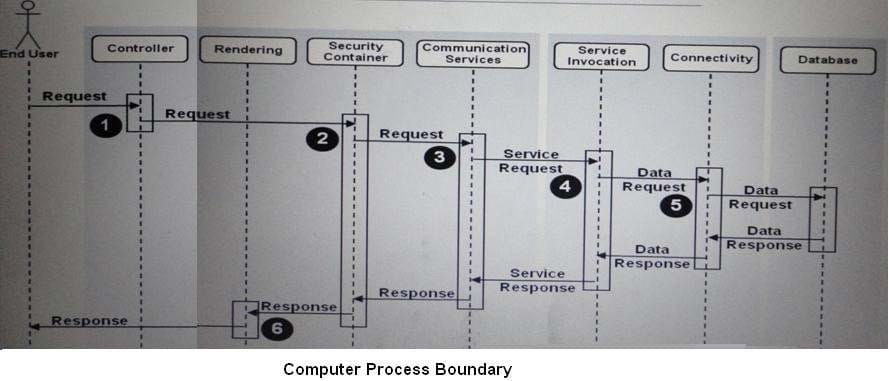
The sequence diagram (attached) maps to the Model-View Controller (MVC) development pattern. Which statement best describes how the sequence diagram maps to the MVC development pattern?
A. The three process blocks (or tiers) represented in the sequence diagram map from left to right to Controller, View, Model.
B. The three process blocks (or tiers) represented in the sequence diagram map from left to right to View, Controller, Model.
C. The Controller and View appear in the first process block (starting from the left of the diagram) while the Model spans the next two blocks (incorporating service Invocation and database).
D. The sequence diagram does not map to MVC.
-
Question 58:
Which of the following are capabilities required for the Integration subsystem of the Oracle Reference Architecture Management and Monitoring Framework?
A. Data Exchange
B. Extensibility Framework
C. Patch Monitoring
D. Alert and Notification Integration
E. Reporting
-
Question 59:
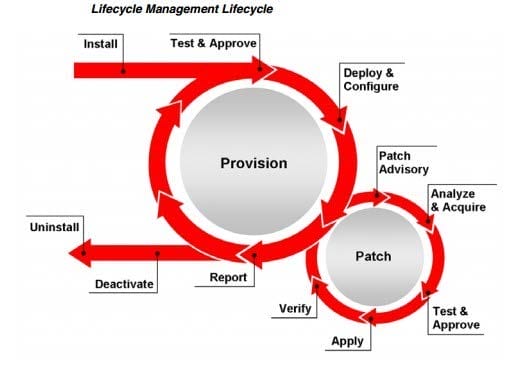
What does Lifecycle Management Provisioning refer to?
A. The process of preparing and equipping a network to allow it to provide (new) services to its users.
B. Automation of the Installation and configuration of operating systems, infrastructure software, applications, services, virtual servers, and hosts across different platforms, environments, and locations
C. Demonstration and enforcement of regulatory standards. Industry standards, and internal best practices
D. A comprehensive management and monitoring solution that helps to effectively manage services from an overview level to theindividual component
-
Question 60:
Which of the following statements are true?
A. The MVC pattern became very popular when the client-server architecture was in common use.
B. MVC was developed to map to three tiers of an n-tier architecture.
C. Federation, as applied to user interfaces, means that all security standards must only be applied at a level at which government security agencies are able to decrypt communications.
D. Federation, as applied to user interfaces, is the concept that parts of the user interface arecreatedand controlled by an organization that is separate from the organization creating the user interface.
E. When in a disconnected state, the Data Management capability in the client tier may act temporarily as the model allowing the user interface to function.
F. Federation, as applied to a user interfaces, means that data must be replicated.
Related Exams:
1Z0-020
Oracle8i: New Features for Administrators1Z0-023
Architecture and Administration1Z0-024
Performance Tuning1Z0-025
Backup and Recovery1Z0-026
Network Administration1Z0-034
Upgrade Oracle9i/10g OCA to Oracle Database OCP1Z0-036
Managing Oracle9i on Linux1Z0-041
Oracle Database 10g: DBA Assessment1Z0-052
Oracle Database 11g: Administration Workshop I1Z0-053
Oracle Database 11g: Administration II
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Oracle exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1Z0-574 exam preparations and Oracle certification application, do not hesitate to visit our Vcedump.com to find your solutions here.