Exam Details
Exam Code
:1Z0-822Exam Name
:Oracle Solaris 11 Advanced System AdministrationCertification
:Oracle CertificationsVendor
:OracleTotal Questions
:140 Q&AsLast Updated
:Mar 24, 2025
Oracle Oracle Certifications 1Z0-822 Questions & Answers
-
Question 91:
Laura is a user and netadm is a role on a Solaris 11 system. You want to allow Laura to generate SSH keys. Which two steps should be taken?
A. Verify that netadm includes the Network Management profile.
B. Verify that laura has permission to access the Network Management profile.
C. Verify that the Network Management profile includes the netadm role.
D. Add a line for the ssh-keygen command to the file auth_attr.d/local-entries.
E. Add a line for the ssh-keygen command to the file exec_attr.d/local-entries.
-
Question 92:
Assume you are on a system that has a valid use account johnjay Consider the following command-line invocation:
rolemod p "Network Administrator,All,Stop" johnjay What is the result?
A. The user will not acquire profiles allowed in /etc/secutity/policy.conf
B. There is no effect. The user acquires all profiles before the Stop profile is read.
C. The system will return an error.
D. The user gets Network Administrator profile and all profiles listed in the All macro.
-
Question 93:
The output of the ppriv command lists four privilege sets. Which option best describes the Inherited privilege set?
A. It is the privilege set that nonroot users may inherit.
B. It is the privilege set an effective-user process may inherit.
C. It is the privilege set only privilege-aware child processes may inherit.
D. It is the privilege set the current process inherited.
-
Question 94:
You appended a site-specific Rights Profile to the /etc/security/prof_attr file. Which file will be updated as a result of this operation?
A. /etc/security/prof_attr.d/local-entries
B. /etc/security/prof_attr.d/prof_attr
C. /etc/security/prof_attr.d/core-os
D. /etc/user_attr
-
Question 95:
You created a role. The role should be able to change the configuration of a zone. How will you assign that privilege to the role?
A. Modify the zone using the admin resource, set the user property to the role and the auths property to manage.
B. Assign to the role the zone Management Rights Profile.
C. Assign to the role the solaris.zones.* authorization.
D. Assign to the role the zone Security Rights Profile.
-
Question 96:
Yon are using the svc:/network/http:apache22 service to manage your web server. You have noticed that this service starts as the root: user and later changes to a nonprivileged user called webservd. You do not want this service to operate as the root user and any time. Which option correctly describes how you could achieve this task?
A. Modify the privileges in the service configuration.
B. Add an authorization to the webservd users' rights' profile.
C. Create a webservd role with a modified exec_attr entry.
D. Modify the PHIV_AWARE state of the service configuration.
-
Question 97:
You created a virtual network of three zones.
One network hosts a web server.
Another hosts an application server used by the web server.
The third zone host a video streaming application.
You already configured a flow to prioritize the video traffic over the web server traffic. You now need to continuously monitor the flow.
Which tool must you use to gather the flow data?
A. the system activity reporter (SAR)
B. extended accounting
C. the flowstat command
D. the kstat utility
-
Question 98:
You configured a limit of 100 LWPs project. You want to ensure that the LWP limit was not set too low, so you need to monitor the LWPs currently in use by the project. Which two options could you use to monitor the current LWP resource control and the consumption of resources for this project?
A. prtcl $$
B. configuring syslogd to log messages received from the resource manager daemon
C. ps o taskid p
D. prtcl n task.max-lwps $$
E. rctladm l task.max-lwps
F. rctladm e syslog task.max-lwps; when the threshold for the resource is exceeded, a log entry will be generated by syslogd
-
Question 99:
The following information describes the current dump configuration of your server:
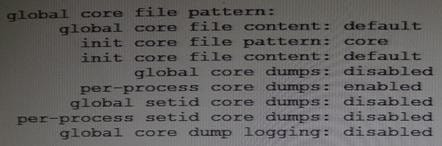
Assume that the following command lines have been run on a system:
(root) # coreadm g $HOME/var/core/%m.core.%f.%t (non-root) $ coreadm p core.%f.%p
Identify the result of a subsequent process crash.
A. A copy of a core file will appear in /var/core.
B. A copy of a core file will appear in the process' current working directory.
C. The root copy will include the taskid of the process.
D. The nonroot copy will include the day of the process crash.
E. The global format will override the per-process format.
F. The global core dump is disabled, so a core file will not be saved.
-
Question 100:
You are asked to configure your system to save crash dump information. While choosing a directory to save the dump data, you consider protecting a minimum amount of free space. What is the default minimum free space in a crash dump directory?
A. By default, the minimum free space is 10% of the size of the dump volume.
B. By default, no minimum free space is set.
C. By default, the minimum free space is 1 MB.
D. By default, the space is determined by the amount of swap space.
E. By default, the spat e is determined by the amount of memory installed in the system.
Related Exams:
1Z0-020
Oracle8i: New Features for Administrators1Z0-023
Architecture and Administration1Z0-024
Performance Tuning1Z0-025
Backup and Recovery1Z0-026
Network Administration1Z0-034
Upgrade Oracle9i/10g OCA to Oracle Database OCP1Z0-036
Managing Oracle9i on Linux1Z0-041
Oracle Database 10g: DBA Assessment1Z0-052
Oracle Database 11g: Administration Workshop I1Z0-053
Oracle Database 11g: Administration II
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Oracle exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1Z0-822 exam preparations and Oracle certification application, do not hesitate to visit our Vcedump.com to find your solutions here.