Exam Details
Exam Code
:200-901Exam Name
:Developing Applications and Automating Workflows using Cisco Platforms (DEVASC)Certification
:Cisco Certified DevNet AssociateVendor
:CiscoTotal Questions
:615 Q&AsLast Updated
:Mar 28, 2025
Cisco Cisco Certified DevNet Associate 200-901 Questions & Answers
-
Question 471:
Which protocol must be allowed on the firewall so that NTP services work properly?
A. TCP
B. ICMP
C. BGP
D. UDP
-
Question 472:
How are load balancers used in modern application deployments?
A. Turn off traffic and take down compute units, then update and bring the compute units back up.
B. Allow traffic to continue as new compute units are brought up and old compute units are taken down.
C. Allow http and https traffic to continue as old compute units are discontinued before new units are brought up.
D. Bring up new compute units, test the compute units, and switch the traffic from old units to new units.
-
Question 473:
Which advantage does the agile process offer compared to waterfall software development?
A. to add or update features with incremental delivery
B. to view the full scope of end-to-end work
C. to have each phase end before the next begins
D. to fix any issues at the end of the development cycle
-
Question 474:
What is the purpose of a MAC address on a network device?
A. unique network address that identifies the network interface of a device
B. unique network interlace address that is provided by the DHCP server
C. unique hardware address that identifies the network interface of a device
D. unique hardware interface address that is provided by the central switch
-
Question 475:
What are two benefits of model-driven programmability? (Choose two.)
A. easier to design, deploy, and manage APIs
B. single choice of transport, protocol, and encoding
C. models decoupled from transport, protocol, and encoding
D. model-based, structured, and human friendly
E. model-driven APIs for abstraction and simplification
-
Question 476:
Which API must an engineer use to change a netmask on a Cisco IOS XE device?
A. Meraki
B. SD-WAN
C. RESTCONF/YANG
D. DNAC
-
Question 477:
Refer to the exhibit.
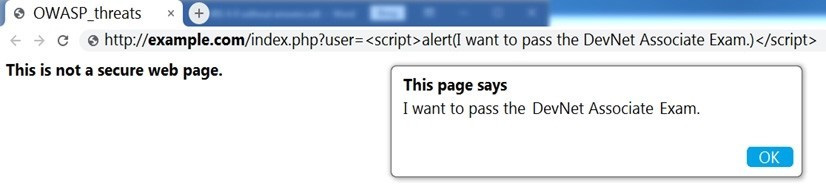
Which OWASP threat does this example demonstrate?
A. broken access control
B. cross-site scripting
C. SQL injection
D. man-in-the-middle
-
Question 478:
A company is looking for a cloud deployment which will only use the on-premise infrastructure, is user self- service, and is easy to scale. Which cloud solution should be selected for these requirements?
A. multi
B. private
C. hybrid
D. public
-
Question 479:
Refer to the exhibit.
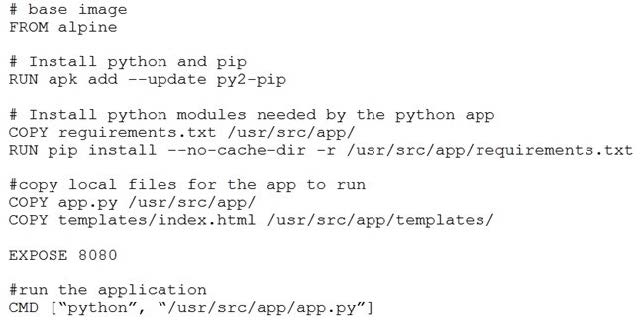
Which function does the EXPOSE line perform when building an image from this Dockerfile?
A. Local port 8080 of the container that launched with this docker image is accessible from co-hosted containers and external clients.
B. Local port 8080 is not reachable at all because no IP address is specified along with the EXPOSE command of the Dockerfile.
C. Local port 8080 is accessible from other containers running on the same docker host as the container that launched with this docker image.
D. Local port 8080 of the container that launched with this docker image is accessible to external clients.
-
Question 480:
Refer to the exhibit.
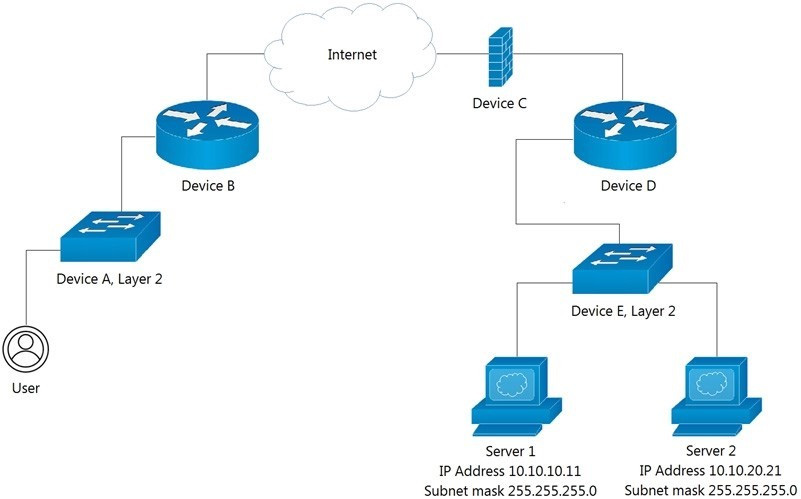
Which Device limits traffic between Server 1 and Server 2?
A. Device B
B. Device C
C. Device D
D. Device E
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-901 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.