Exam Details
Exam Code
:220-1002Exam Name
:CompTIA A+ Certification: Core 2Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:898 Q&AsLast Updated
:Mar 31, 2025
CompTIA CompTIA Certifications 220-1002 Questions & Answers
-
Question 101:
A change advisory board authorized a setting change so a technician is permitted to implement the change. The technician successfully implemented the change.
Which of the following should be done NEXT?
A. Document the date and time of change.
B. Document the purpose of the change.
C. Document the risk level.
D. Document findings of the sandbox test.
-
Question 102:
The Chief Executive Officer at a bank recently saw a news report about a high-profile cybercrime where a remote access tool that the bank uses for support was also used in this crime. The report stated that attackers were able to brute force passwords to access systems.
Which of the following would BEST limit the bank's risk? (Choose two.)
A. Enable multifactor authentication for each support account.
B. Limit remote access to destinations inside the corporate network.
C. Block all support accounts from logging in from foreign countries.
D. Configure a replacement remote-access tool for support cases.
E. Purchase a password manager for remote tool users.
F. Enforce account lockouts after five bad password attempts.
-
Question 103:
Joe, a user, is getting out-of-office replies from people he did not email. A technician inspects Joe's inbox and sees a sent email that appears to have come from Joe. The email contains a link to a well-known company's website, which is spelled incorrectly. Joe's sent items folder shows dozens of emails that were sent to everyone on his contact list.
Which of the following is the MOST likely cause of this issue?
A. Joe was the victim of a man-in-the-middle attack
B. Joe inadvertently triggered a mail merge
C. Joe's email address was spoofed
D. Joe's email password was compromised
-
Question 104:
Which of the following must a systems administrator employ to protect the contents of all corporate machines?
A. Regulatory policy
B. Password policy
C. Acceptable use policy
D. Compliance policy
-
Question 105:
An office computer has been infected with malware.
Which of the following steps should be taken FIRST?
A. Back up the hard drive
B. Educate the user
C. Quarantine the infected computer
D. Run antivirus software
-
Question 106:
An Android smartphone user constantly receives notices that the device is low on storage. The user has uninstalled unneeded applications and does not want to remove any others.
Which of the following troubleshooting steps should the user take FIRST to identify the issue?
A. Upgrade the device to a newer version with more storage.
B. Restore installed applications to their original device versions by uninstalling updates.
C. Check the storage type and size of the data and cache on each installed application.
D. Add more storage using a memory card.
-
Question 107:
A user's workstation is running extremely slow. A technician sees a pop-up on the workstation offering what appears to be fake technical support, so the technician begins the malware removal procedure. After disabling System Restore, the technician runs a malware scan, but the scan does not find any malware on the machine.
Which of the following is the MOST likely reason the technician cannot find any malware?
A. The technician should not have disabled System Restore
B. The technician never quarantined the workstation
C. The technician did not update the anti-malware software
D. There is no malware on the workstation
-
Question 108:
A technician is troubleshooting a customer's PC and receives a phone call. The technician does not take the call and sets the phone to silent.
Which of the following BEST describes the technician's actions?
A. Avoid distractions
B. Deal appropriately with customer's confidential material
C. Adhere to user privacy policy
D. Set and meet timelines
-
Question 109:
A technician sees the following in a .ps1 file:
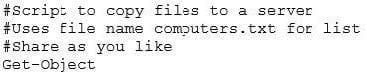
Which of the following BEST describes the lines that start with the # symbol?
A. Basic loops
B. Comments
C. Integers
D. Environment variables
-
Question 110:
A technician has created a new fileshare for an organization. To maintain data security, all users should have read-only rights to the fileshare. Additionally, supervisors need to be able to write and delete files. After the technician has configured the fileshare, users can read documents, but supervisors cannot modify documents.
Which of the following utilities should the technician use to troubleshoot the issue?
A. Microsoft Management Console
B. User Account Control
C. Local Security Policy
D. Map Network Drive
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 220-1002 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.