Exam Details
Exam Code
:300-720Exam Name
:Securing Email with Cisco Email Security Appliance (SESA)Certification
:CCNP SecurityVendor
:CiscoTotal Questions
:148 Q&AsLast Updated
:Mar 26, 2025
Cisco CCNP Security 300-720 Questions & Answers
-
Question 41:
An administrator manipulated the subnet mask but was still unable to access the user interface. How must the administrator access the appliance to perform the initial configuration?
A. Use the data 2 port.
B. Use the serial or console port.
C. Use the data 1 port.
D. Use the management port.
-
Question 42:
A Cisco ESA administrator is creating a Mail Flow Policy to receive outbound email from Microsoft Exchange. Which Connection Behavior must be selected to properly process the messages?
A. Delay
B. Accept
C. Relay
D. Reject
-
Question 43:
Refer to the exhibit.
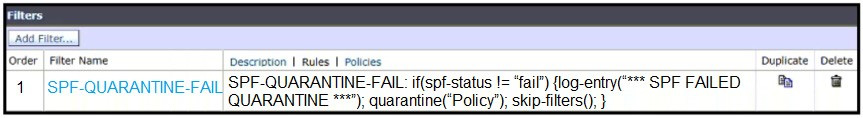
A network engineer must set up a content filter to find any messages that failed SPF and send them into quarantine. The content filter has been set up and enabled, but all messages except those that have failed SPF are being sent into quarantine. Which section of the filter must be modified to correct this behavior?
A. log-entry
B. quarantine
C. spf-status
D. skip-filters
-
Question 44:
Refer to the exhibit.
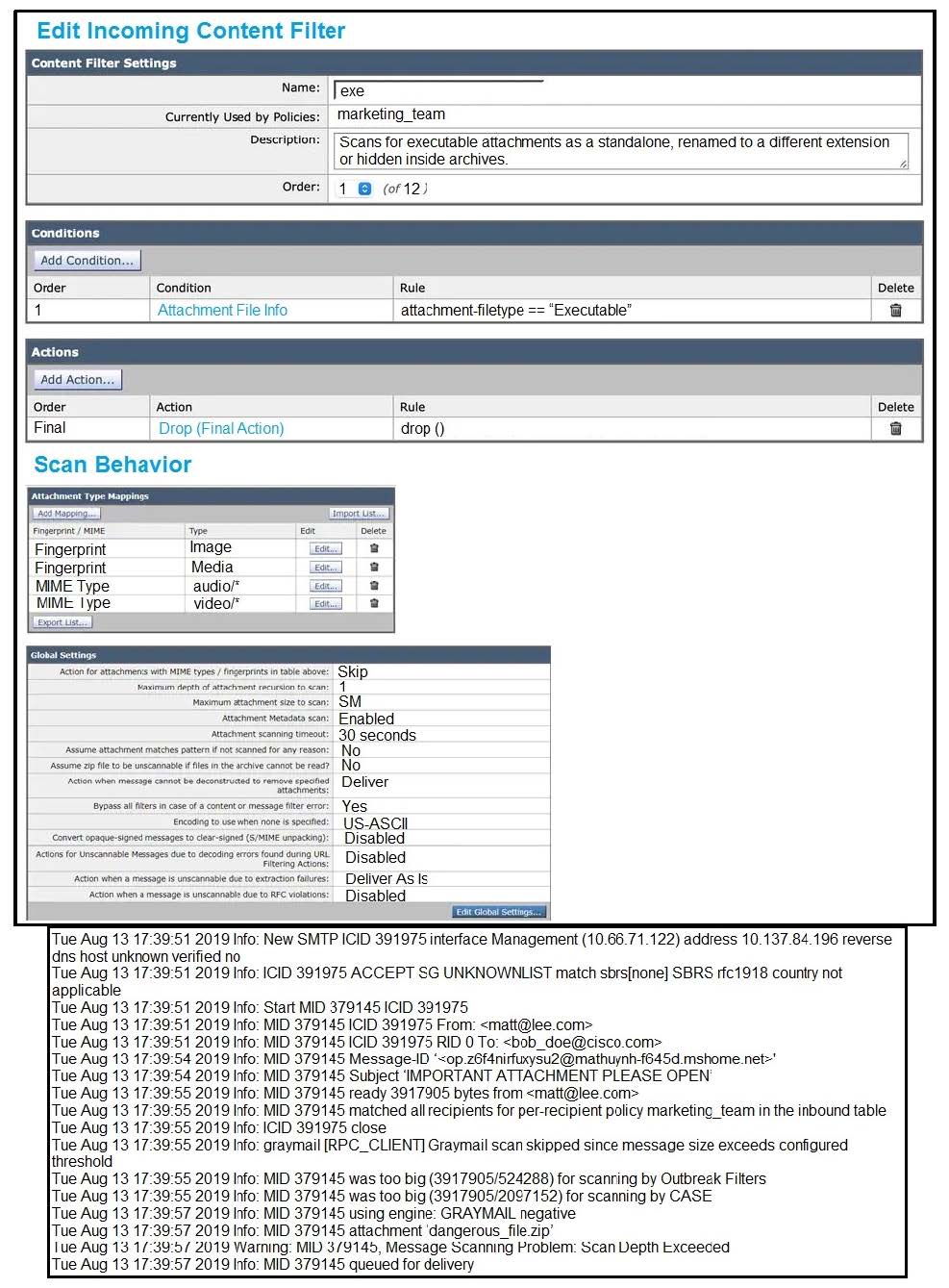
Which configuration allows the Cisco ESA to scan for executables inside the zip and apply the action as per the content filter?
A. Modify the content filter to look for .exe filename instead of executable filetype.
B. Configure the recursion depth to a higher value.
C. Configure the maximum attachment size to a higher value.
D. Modify the content filter to look for attachment filetype of compressed.
-
Question 45:
A Cisco ESA administrator has noticed that new messages being sent to the Centralized Policy Quarantine are being released after one hour. Previously, they were being held for a day before being released.
What was configured that caused this to occur?
A. The retention period was changed to one hour.
B. The threshold settings were set to override the clock settings.
C. The retention period was set to default.
D. The threshold settings were set to default.
-
Question 46:
What are organizations trying to address when implementing a SPAM quarantine?
A. true positives
B. false negatives
C. false positives
D. true negatives
-
Question 47:
Which two Cisco ESA features are used to control email delivery based on the sender? (Choose two.)
A. incoming mail policies
B. spam quarantine
C. outbreak filter
D. safelists
E. blocklists
-
Question 48:
Refer to the exhibit.

An administrator has configured File Reputation and File Analysis on the Cisco ESA; however, is does not function as expected. What must be configured on the Cisco ESA for this to function?
A. Upload the Root CA certificate for the File Reputation cloud to the Cisco ESA.
B. Open port 443 on the firewall for the Cisco ESA to connect to the File Reputation cloud.
C. Restart the File Reputation service to force the scanning engine to connect to the File Reputation cloud.
D. Configure the Cisco ESA to use SSL for the connection to the File Reputation server.
-
Question 49:
Refer to the exhibit.
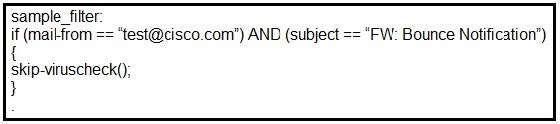
What results from this filter configuration?
A. Action is skipping all antispam checks for the mail.
B. Action is applied to all mail from [email protected].
C. Action is skipping all antivirus checks for the mail.
D. Action is applied to all mail that has the subject "FW: Bounce Notification."
-
Question 50:
An administrator needs to configure Cisco ESA to ensure that emails are sent and authorized by the owner of the domain. Which two steps must be performed to accomplish this task? (Choose two.)
A. Generate keys.
B. Create signing profile.
C. Create Mx record.
D. Enable SPF verification.
E. Create DMARC profile.
Related Exams:
300-710
Securing Networks with Cisco Firepower (SNCF)300-715
Implementing and Configuring Cisco Identity Services Engine (SISE)300-720
Securing Email with Cisco Email Security Appliance (SESA)300-725
Securing the Web with Cisco Web Security Appliance (SWSA)300-730
Implementing Secure Solutions with Virtual Private Networks (SVPN)300-735
Automating and Programming Cisco Security Solutions (SAUTO)350-701
Implementing and Operating Cisco Security Core Technologies (SCOR)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 300-720 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.