Exam Details
Exam Code
:312-49V9Exam Name
:EC-Council Certified Computer Hacking Forensic Investigator (V9)Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:531 Q&AsLast Updated
:Apr 14, 2025
EC-COUNCIL EC-COUNCIL Certifications 312-49V9 Questions & Answers
-
Question 451:
The Electronic Serial Number (ESN) is a unique __________ recorded on a secure chip in a mobile phone by the manufacturer.
A. 16-bit identifier
B. 24-bit identifier
C. 32-bit identifier
D. 64-bit identifier
-
Question 452:
The IIS log file format is a fixed (cannot be customized) ASCII text-based format. The IIS format includes basic items, such as client IP address, user name, date and time, service and instance, server name and IP address, request type, target of operation, etc. Identify the service status code from the following IIS log.
192.168.100.150, -, 03/6/11, 8:45:30, W3SVC2, SERVER, 172.15.10.30, 4210, 125, 3524, 100, 0, GET, / dollerlogo.gif,
A. W3SVC2
B. 4210
C. 3524
D. 100
-
Question 453:
Data acquisition system is a combination of tools or processes used to gather, analyze and record Information about some phenomenon. Different data acquisition system are used depends on the location, speed, cost. etc. Serial communication data acquisition system is used when the actual location of the data is at some distance from the computer. Which of the following communication standard is used in serial communication data acquisition system?
A. RS422
B. RS423
C. RS232
D. RS231
-
Question 454:
FAT32 is a 32-bit version of FAT file system using smaller clusters and results in efficient storage capacity. What is the maximum drive size supported?
A. 1 terabytes
B. 2 terabytes
C. 3 terabytes
D. 4 terabytes
-
Question 455:
Task list command displays a list of applications and services with their Process ID (PID) for all tasks running on either a local or a remote computer.
Which of the following task list commands provides information about the listed processes, including the image name, PID, name, and number of the session for the process?
A. tasklist/s
B. tasklist/u
C. tasklist/p
D. tasklist/V
-
Question 456:
A mobile operating system manages communication between the mobile device and other compatible devices like computers, televisions, or printers.
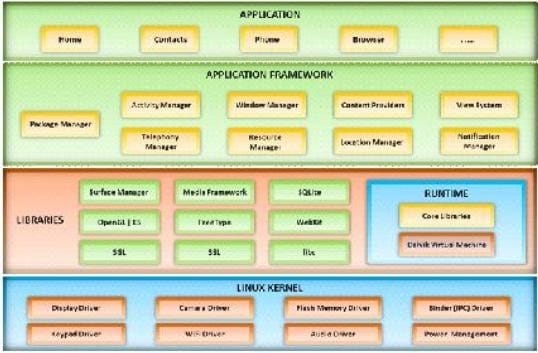
Which mobile operating system architecture is represented here?
A. webOS System Architecture
B. Symbian OS Architecture
C. Android OS Architecture
D. Windows Phone 7 Architecture
-
Question 457:
Which of the following Wi-Fi chalking methods refers to drawing symbols in public places to advertise open Wi-Fi networks?
A. WarWalking
B. WarFlying
C. WarChalking
D. WarDhving
-
Question 458:
In what circumstances would you conduct searches without a warrant?
A. When destruction of evidence is imminent, a warrantless seizure of that evidence is justified if there is probable cause to believe that the item seized constitutes evidence of criminal activity
B. Agents may search a place or object without a warrant if he suspect the crime was committed
C. A search warrant is not required if the crime involves Denial-Of-Service attack over the Internet
D. Law enforcement agencies located in California under section SB 567 are authorized to seize computers without warrant under all circumstances
-
Question 459:
MAC filtering is a security access control methodology, where a ___________ is assigned to each network card to determine access to the network
A. 16-bit address
B. 24-bit address
C. 32-bit address
D. 48-bit address
-
Question 460:
Network forensics can be defined as the sniffing, recording, acquisition and analysis of the network traffic and event logs in order to investigate a network security incident.
A. True
B. False
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-49V9 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.