Exam Details
Exam Code
:312-50V8Exam Name
:Certified Ethical Hacker v8Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:1008 Q&AsLast Updated
:Apr 15, 2025
EC-COUNCIL EC-COUNCIL Certifications 312-50V8 Questions & Answers
-
Question 271:
TCP packets transmitted in either direction after the initial three-way handshake will have which of the following bit set?
A. SYN flag
B. ACK flag
C. FIN flag
D. XMAS flag
-
Question 272:
Which of the following is NOT part of CEH Scanning Methodology?
A. Check for Live systems
B. Check for Open Ports
C. Banner Grabbing
D. Prepare Proxies
E. Social Engineering attacks
F. Scan for Vulnerabilities
G. Draw Network Diagrams
-
Question 273:
Lee is using Wireshark to log traffic on his network. He notices a number of packets being directed to an internal IP from an outside IP where the packets are ICMP and their size is around 65, 536 bytes.
What is Lee seeing here?
A. Lee is seeing activity indicative of a Smurf attack.
B. Most likely,the ICMP packets are being sent in this manner to attempt IP spoofing.
C. Lee is seeing a Ping of death attack.
D. This is not unusual traffic,ICMP packets can be of any size.
-
Question 274:
This method is used to determine the Operating system and version running on a remote target system. What is it called?
A. Service Degradation
B. OS Fingerprinting
C. Manual Target System
D. Identification Scanning
-
Question 275:
William has received a Chess game from someone in his computer programming class through email. William does not really know the person who sent the game very well, but decides to install the game anyway because he really likes Chess.

After William installs the game, he plays it for a couple of hours. The next day, William plays the Chess game again and notices that his machine has begun to slow down. He brings up his Task Manager and
sees the following programs running:
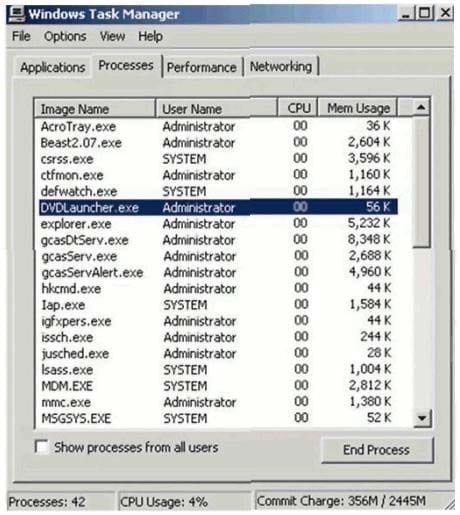
What has William just installed?
A. Zombie Zapper (ZoZ)
B. Remote Access Trojan (RAT)
C. Bot IRC Tunnel (BIT)
D. Root Digger (RD)
-
Question 276:
John the hacker is sniffing the network to inject ARP packets. He injects broadcast frames onto the wire to conduct MiTM attack.
What is the destination MAC address of a broadcast frame?
A. 0xFFFFFFFFFFFF
B. 0xDDDDDDDDDDDD
C. 0xAAAAAAAAAAAA
D. 0xBBBBBBBBBBBB
-
Question 277:
You are gathering competitive intelligence on an organization. You notice that they have jobs listed on a few Internet job-hunting sites. There are two jobs for network and system administrators. How can this help you in foot printing the organization?
A. To learn about the IP range used by the target network
B. To identify the number of employees working for the company
C. To test the limits of the corporate security policy enforced in the company
D. To learn about the operating systems,services and applications used on the network
-
Question 278:
A Trojan horse is a destructive program that masquerades as a benign application. The software initially appears to perform a desirable function for the user prior to installation and/or execution, but in addition to the expected function steals information or harms the system.
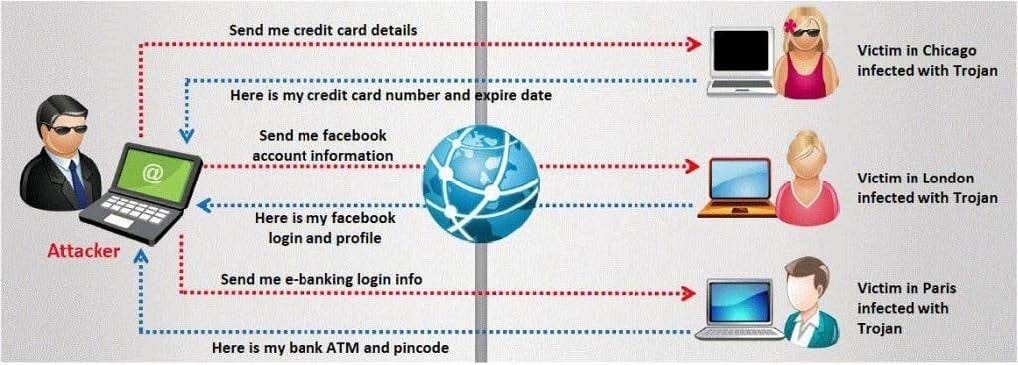
The challenge for an attacker is to send a convincing file attachment to the victim, which gets easily executed on the victim machine without raising any suspicion. Today's end users are quite knowledgeable about malwares and viruses. Instead of sending games and fun executables, Hackers today are quite successful in spreading the Trojans using Rogue security software.
What is Rogue security software?
A. A flash file extension to Firefox that gets automatically installed when a victim visits rogue software disabling websites
B. A Fake AV program that claims to rid a computer of malware,but instead installs spyware or other malware onto the computer. This kind of software is known as rogue security software.
C. Rogue security software is based on social engineering technique in which the attackers lures victim to visit spear phishing websites
D. This software disables firewalls and establishes reverse connecting tunnel between the victim's machine and that of the attacker
-
Question 279:
You are the CIO for Avantes Finance International, a global finance company based in Geneva. You are responsible for network functions and logical security throughout the entire corporation. Your company has over 250 servers running Windows Server, 5000 workstations running Windows Vista, and 200 mobile users working from laptops on Windows 7.
Last week, 10 of your company's laptops were stolen from salesmen while at a conference in Amsterdam. These laptops contained proprietary company information. While doing damage assessment on the possible public relations nightmare this may become, a news story leaks about the stolen laptops and also that sensitive information from those computers was posted to a blog online.
What built-in Windows feature could you have implemented to protect the sensitive information on these laptops?
A. You should have used 3DES which is built into Windows
B. If you would have implemented Pretty Good Privacy (PGP) which is built into Windows,the sensitive information on the laptops would not have leaked out
C. You should have utilized the built-in feature of Distributed File System (DFS) to protect the sensitive information on the laptops
D. You could have implemented Encrypted File System (EFS) to encrypt the sensitive files on the laptops
-
Question 280:
Steve scans the network for SNMP enabled devices.
Which port number Steve should scan?
A. 150
B. 161
C. 169
D. 69
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V8 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.