Exam Details
Exam Code
:412-79V10Exam Name
:EC-Council Certified Security Analyst (ECSA) V10Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:201 Q&AsLast Updated
:Mar 23, 2025
EC-COUNCIL EC-COUNCIL Certifications 412-79V10 Questions & Answers
-
Question 71:
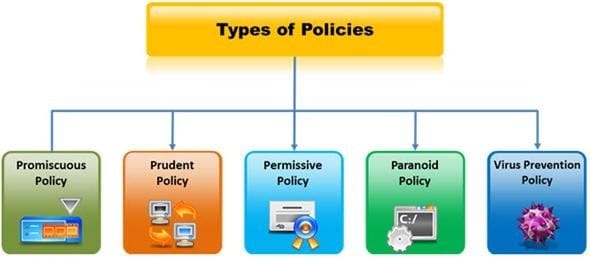
A security policy is a document or set of documents that describes, at a high level, the security controls that will be implemented by the company. Which one of the following policies forbids everything and restricts usage of company computers, whether it is system usage or network usage?
A. Paranoid Policy
B. Prudent Policy
C. Promiscuous Policy
D. Information-Protection Policy
-
Question 72:
Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
A. Unannounced Testing
B. Double Blind Testing
C. Announced Testing
D. Blind Testing
-
Question 73:
Traffic on which port is unusual for both the TCP and UDP ports?
A. Port 81
B. Port 443
C. Port 0
D. Port21
-
Question 74:
Amazon, an IT based company, conducts a survey on the usage of the Internet. They found that company employees spend most of the time at work surfing the web for their personal use and for inappropriate web site viewing. Management decide to block all such web sites using URL filtering software.

How can employees continue to see the blocked websites?
A. Using session hijacking
B. Using proxy servers
C. Using authentication
D. Using encryption
-
Question 75:
In the process of hacking a web application, attackers manipulate the HTTP requests to subvert the application authorization schemes by modifying input fields that relate to the user ID, username, access group, cost, file names, file identifiers, etc. They first access the web application using a low privileged account and then escalate privileges to access protected resources. What attack has been carried out?
A. XPath Injection Attack
B. Authorization Attack
C. Authentication Attack
D. Frame Injection Attack
-
Question 76:
Which type of security policy applies to the below configuration? i)Provides maximum security while allowing known, but necessary, dangers ii)All services are blocked; nothing is allowed iii)Safe and necessary services are enabled individually iv)Non-essential services and procedures that cannot be made safe are NOT allowed v)Everything is logged
A. Paranoid Policy
B. Prudent Policy
C. Permissive Policy
D. Promiscuous Policy
-
Question 77:
Which of the following acts related to information security in the US establish that the management of an organization is responsible for establishing and maintaining an adequate internal control structure and procedures for financial reporting?
A. USA Patriot Act 2001
B. Sarbanes-Oxley 2002
C. Gramm-Leach-Bliley Act (GLBA)
D. California SB 1386
-
Question 78:
What are the 6 core concepts in IT security?
A. Server management, website domains, firewalls, IDS, IPS, and auditing
B. Authentication, authorization, confidentiality, integrity, availability, and non-repudiation
C. Passwords, logins, access controls, restricted domains, configurations, and tunnels
D. Biometrics, cloud security, social engineering, DoS attack, viruses, and Trojans
-
Question 79:
You work as an IT security auditor hired by a law firm in Boston. You have been assigned the responsibility to audit the client for security risks. When assessing the risk to the clients network, what step should you take first?
A. Analyzing, categorizing and prioritizing resources
B. Evaluating the existing perimeter and internal security
C. Checking for a written security policy
D. Analyzing the use of existing management and control architecture
-
Question 80:
From where can clues about the underlying application environment can be collected?
A. From the extension of the file
B. From executable file
C. From file types and directories
D. From source code
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 412-79V10 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.