Exam Details
Exam Code
:C2090-611Exam Name
:DB2 10.1 DBA for Linux UNIX and WindowsCertification
:IBM Certified Advanced Database AdministratorVendor
:IBMTotal Questions
:118 Q&AsLast Updated
:Mar 31, 2025
IBM IBM Certified Advanced Database Administrator C2090-611 Questions & Answers
-
Question 21:
What authorization is needed to use the AUDIT statement to create an audit policy?
A. DBADM
B. SYSADM
C. SECADM
D. SYSMAINT
-
Question 22:
The following statement is run:
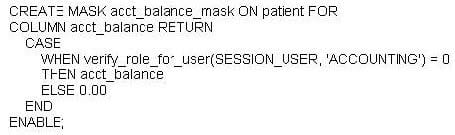
Which statement about the ACCT_BALANCE column is true?
A. Values stored in the ACCT_BALANCE column are visible to all users.
B. Values stored in the ACCT_BALANCE column are not visible to any user.
C. Values stored in the ACCT_BALANCE column are only visible to users with the ACCOUNTING role.
D. Values stored in the ACCT_BALANCE column are not visible to users with the ACCOUNTING role.
-
Question 23:
Which administrative authority is needed to grant ACCESSCTRL, DATAACCESS, or SECADM authority to other users, groups, or roles?
A. DBADM
B. SYSADM
C. SQLADM
D. SECADM
-
Question 24:
What authority is required to grant a user ACCESSCTRL authority?
A. DBADM
B. SQLADM
C. SECADM
D. DATAACCESS
-
Question 25:
Which is a valid statement about the Row and Column Access Control (RCAC) feature?
A. Users with SECADM authority are exempt from RCAC rules.
B. The RCAC feature uses a subset of Label Based Access Control (LBAC) functionality.
C. RCAC is a more powerful security mechanism than Label Based Access Control (LBAC).
D. When a result set is restricted due to the RCAC rules defined on a table, no warnings or errors are returned.
-
Question 26:
What type of Label-Based Access Control (LBAC) security label component is used to define a scale in which the first element listed represents the highest level of trust a person can have and the last element listed represents the lowest level of trust a person can have?
A. Set
B. Array
C. Tree
D. Range
-
Question 27:
A table named SALES was created as follows:
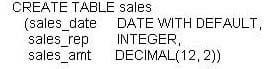
If management wants to use Label-Based Access Control (LBAC) to protect individual columns in the SALES table, and the security policy needed (SEC_POLICY) has already been created, what must be done to protect the table as desired?
A. Associate the SEC_POLICY security policy with the SALES table.
B. Add a SECURED WITH clause to every column in the SALES table.
C. Add a column with the DB2SECURITYLABEL data type to the SALES table and then associate the SEC_POLICY security policy with the table.
D. Add a SECURED WITH clause to every column in the SALES table and then associate the SEC_POLICY security policy with the SALES table.
-
Question 28:
If a single node database is actively being used by applications when a power failure occurs, what method is used to bring the database back to a consistent state once power has been restored?
A. Crash recovery
B. Version recovery
C. Disaster recovery
D. Roll-forward recovery
-
Question 29:
Which High Availability Disaster Recovery (HADR) synchronization mode provides the shortest transaction response time but has the highest probability of transaction losses if the primary system fails?
A. SYNC (synchronous)
B. ASYNC (asynchronous)
C. NEARSYNC (near synchronous)
D. SUPERASYNC (super asynchronous)
-
Question 30:
Which statement regarding SECADM authority is true?
A. The instance owner has SECADM authority by default.
B. PUBLIC cannot receive SECADM authority, either directly or indirectly.
C. Only users with SECADM authority are allowed to grant the CONNECT database authority to others.
D. The SECADM_GROUP database manager configuration parameter determines who has SECADM authority by default.
Related Exams:
A2090-541
Assessment: DB2 9.7 DBA for LUW-AssessmentA2090-544
Assessment: DB2 9.7 Advanced DBA for LUW - AssessmentA2090-610
Assessment: DB2 10.1 Fundamentals - AssessmentA2090-611
Assessment: DB2 10.1 DBA for Linux, UNIX, and Windows - AssessmentA2090-614
Assessment: DB2 10.1 Advanced DBA for LUW - AssessmentA2090-730
Assessment: DB2 9 Fundamentals-AssessmentC2090-541
DB2 9.7 DBA for Linux UNIX and WindowsC2090-610
DB2 10.1 FundamentalsC2090-611
DB2 10.1 DBA for Linux UNIX and WindowsC2090-614
DB2 10.1 Advanced DBA for Linux UNIX and Windows
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only IBM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your C2090-611 exam preparations and IBM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.