Exam Details
Exam Code
:EC0-349Exam Name
:Computer Hacking Forensic InvestigatorCertification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:304 Q&AsLast Updated
:Mar 26, 2025
EC-COUNCIL EC-COUNCIL Certifications EC0-349 Questions & Answers
-
Question 231:
Heather, a computer forensics investigator, is assisting a group of investigators working on a large computer fraud case involving over 20 people. These 20 people, working in different offices, allegedly siphoned off money from many different client accounts. Heather responsibility is to find out how the accused people communicated between each other. She has searched their email and their computers and has not found any useful evidence. Heather then finds some possibly useful evidence under the desk of one of the accused. In an envelope she finds a piece of plastic with numerous holes cut out of it. Heather then finds the same exact piece of plastic with holes at many of the other accused peoples desks. Heather believes that the 20 people involved in the case were using a cipher to send secret messages in between each other. What type of cipher was used by the accused in this case?
A. Grill cipher
B. Null cipher
C. Text semagram
D. Visual semagram
-
Question 232:
In the following directory listing,
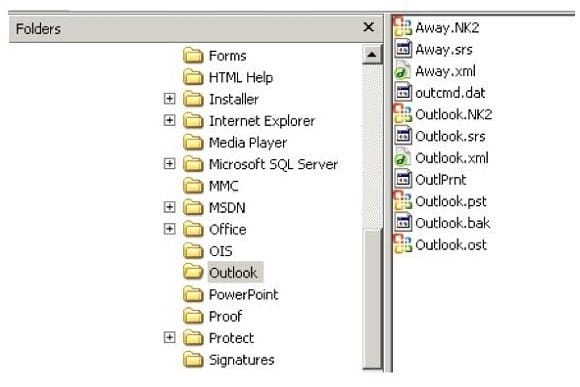
Which file should be used to restore archived email messages for someone using Microsoft Outlook?
A. Outlook bak
B. Outlook ost
C. Outlook NK2
D. Outlook pst
-
Question 233:
Daryl, a computer forensics investigator, has just arrived at the house of an alleged computer hacker. Daryl takes pictures and tags all computer and peripheral equipment found in the house. Daryl packs all the items found in his van and takes them back to his lab for further examination. At his lab, Michael his assistant helps him with the investigation. Since Michael is still in training, Daryl supervises all of his work very carefully. Michael is not quite sure about the procedures to copy all the data off the computer and peripheral devices. How many data acquisition tools should Michael use when creating copies of the evidence for the investigation?
A. Two
B. One
C. Three
D. Four
-
Question 234:
What feature of Decryption Collection allows an investigator to crack a password as quickly as possible?
A. Cracks every password in 10 minutes
B. Distribute processing over 16 or fewer computers
C. Support for Encrypted File System
D. Support for MD5 hash verification
-
Question 235:
What hashing method is used to password protect Blackberry devices?
A. AES
B. RC5
C. MD5
D. SHA-1
-
Question 236:
What layer of the OSI model do TCP and UDP utilize?
A. Data Link
B. Network
C. Transport
D. Session
-
Question 237:
When making the preliminary investigations in a sexual harassment case, how many investigators are you recommended having?
A. One
B. Two
C. Three
D. Four
-
Question 238:
What type of equipment would a forensics investigator store in a StrongHold bag?
A. PDAPDA?
B. Backup tapes
C. Hard drives
D. Wireless cards
-
Question 239:
If you are concerned about a high level of compression but not concerned about any possible data loss, what type of compression would you use?
A. Lossful compression
B. Lossy compression
C. Lossless compression
D. Time-loss compression
-
Question 240:
When marking evidence that has been collected with the aa/ddmmyy/nnnn/zz format, what does the nnn denote?
A. The year the evidence was taken
B. The sequence number for the parts of the same exhibit
C. The initials of the forensics analyst
D. The sequential number of the exhibits seized
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your EC0-349 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.