Exam Details
Exam Code
:C1000-018Exam Name
:IBM QRadar SIEM V7.3.2 Fundamental AnalysisCertification
:IBM CertificationsVendor
:IBMTotal Questions
:60 Q&AsLast Updated
:Mar 26, 2025
IBM IBM Certifications C1000-018 Questions & Answers
-
Question 31:
Which consideration should be given to the position of rule tests that evaluate regular expressions (Regex tests)?
A. They can only be used in Building Blocks to ensure they are evaluated as infrequently as possible.
B. They are usually the most specific. As such, they should appear first in the order.
C. They are usually the most expensive. As such, they should appear last in the order.
D. They are stateful tests. As such QRadar automatically evaluates them last.
-
Question 32:
An analyst needs to perform Offense management.
In QRadar SIEM, what is the significance of “Protecting” an offense?
A. Escalate the Offense to the QRadar administrator for investigation.
B. Hide the Offense in the Offense tab to prevent other analysts to see it.
C. Prevent the Offense from being automatically removed from QRadar.
D. Create an Action Incident response plan for a specific type of cyber attack.
-
Question 33:
What could be a possible reason that events are routed directly to storage by the custom rule engine (CRE)?
A. System is under high load
B. A rule is processing 20,000 EPS
C. Event normalization issue
D. Event Parsing issue
-
Question 34:
What is the purpose of Anomaly detection rules?
A. They inspect other QRadar rules.
B. They detect if QRadar is operating at peak performance and error free.
C. They detect unusual traffic patterns in the network from the results of saved flow and events.
D. They run past events and flows through the Custom Rules Engine (CRE) to identify threats or security incidents that already occurred.
-
Question 35:
What is the intent of the magnitude of an offense?
A. It measures the age of the event attached to the offense.
B. It measures the age of the offense.
C. It measures the importance of the offense.
D. It measures the importance of the event attached to the offense.
-
Question 36:
How many normalized timestamp field(s) does an event contain?
A. 2
B. 3
C. 4
D. 1
-
Question 37:
While creating a new custom property, which is a valid property type selection?
A. Flow Based
B. Event Based
C. AQL Based
D. Regular Expressions Based
-
Question 38:
The graph below shows a time series of a value. A rule has been created which will trigger at the indicated point.
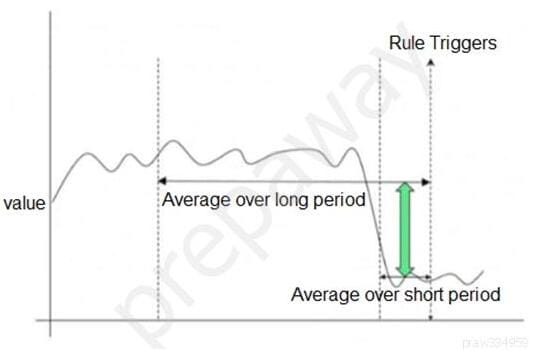
Which type of QRadar rule has been used?
A. Common Rule
B. Threshold Rule
C. Behavioral Rule
D. Anomaly Rule
-
Question 39:
When an Offense is triggered, it only shows the events that triggered the Offense. The analyst wants to investigate further to see more events around the incident, not only those that triggered the Offense. The analyst clicks on the event count and sees the events belonging to the Offense.
How can the analyst proceed to see a more detailed picture of what occurred?
A. Right-click on the source IP, and choose More Options, then Information, and then Search Events.
B. Right-click on the destination IP, and choose More Options, then Raw Events.
C. Right-click on the source IP, and choose View in DSM Editor.
D. Right-click and filter on the Destination IP.
-
Question 40:
Which filter would an analyst apply in the Log Activity tab to get a list of log sources not reporting to QRadar?
A. Log source status does not equal active
B. Custom rule equals device stopped sending events
C. Log source type does not equal active
D. Log source status does not equal error
Related Exams:
C1000-002
IBM MQ V9.0 System AdministrationC1000-003
IBM Mobile Foundation v8.0 Application DevelopmentC1000-004
IBM Curam SPM V7.X Application DeveloperC1000-007
IBM Cloud Application Development v3C1000-010
IBM Operational Decision Manager Standard V8.9.1 Application DevelopmentC1000-012
IBM Watson Application Developer V3.1C1000-015
IBM Business Process Manager V8.6 Application Development using Process DesignerC1000-018
IBM QRadar SIEM V7.3.2 Fundamental AnalysisC1000-020
IBM New Workloads Sales V2C1000-021
IBM Virtualized Storage V2
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only IBM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your C1000-018 exam preparations and IBM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.