Exam Details
Exam Code
:CV0-004Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:285 Q&AsLast Updated
:Apr 01, 2025
CompTIA CompTIA Certifications CV0-004 Questions & Answers
-
Question 191:
A customer relationship management application, which is hosted in a public cloud laaS network, is vulnerable to a remote command execution vulnerability.
Which of the following is the best solution for the security engineer to implement to prevent the application from being exploited by basic attacks?
A. IPS
B. ACL
C. DLP
D. WAF
-
Question 192:
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce costs.
Which of the following are the most important requisite steps to create the report? (Select two).
A. Set the desired retention of resource logs.
B. Configure application tracing.
C. Integrate email alerts with ticketing software.
D. Enable resource tagging.
E. Configure the collection of performance/utilization logs.
F. Configure metric threshold alerts.
-
Question 193:
An engineer wants to scale several cloud workloads on demand. Which of the following approaches is the most suitable?
A. Load
B. Scheduled
C. Manual
D. Trending
-
Question 194:
A company operates a website that allows customers to upload, share, and retain full ownership of their photographs. Which of the following could affect image ownership as the website's usage expands globally?
A. Sovereignty
B. Data classification
C. Litigation holds
D. Retention
-
Question 195:
A cloud engineer is exploring options to reduce the management overhead of the servers and network. Which of the following cloud service models should the engineer implement?
A. SaaS
B. XaaS
C. PaaS
D. laaS
-
Question 196:
A security engineer recently discovered a vulnerability in the operating system of the company VMs. The operations team reviews the issue and decides all VMs need to be updated from version 3.4.0 to 3.4.1. Which of the following best describes the type of update that will be applied?
A. Consistent
B. Major
C. Minor
D. Ephemeral
-
Question 197:
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
A. Resource tagging
B. Discretionary access control
C. Multifactor authentication
D. Role-based access control
E. Token-based authentication
F. Bastion host
-
Question 198:
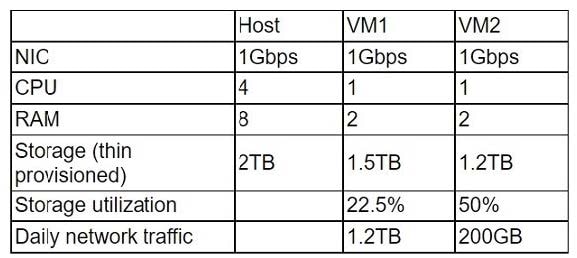
A cloud administrator wants to provision a host with two VMs. The VMs require the following: After configuring the servers, the administrator notices that during certain hours of the day, the performance heavily degrades. Which of the following is the best explanation?
A. The host requires additional physical CPUs.
B. A higher number of processes occur at those times.
C. The RAM on each VM is insufficient.
D. The storage is overutilized.
-
Question 199:
A company has one cloud-based web server that is prone to downtime during maintenance. Which of the following should the cloud engineer add to ensure high availability?
A. A redundant web server behind a load balancer
B. A backup cloud web server
C. A secondary network link to the web server
D. An autoscaling feature on the web server
-
Question 200:
A cloud engineer is extending on-premises services to a public cloud. The following design requirements must be considered in the overall solution:
1.
The ability to remotely connect systems from both environments
2.
No IP address conflicts or overlap
3.
Cost-effectiveness
Which of the following cloud network concepts best meets these requirements?
A. Dedicated connection
B. VPN
C. VLAN
D. ACL
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-004 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.