Exam Details
Exam Code
:HPE6-A68Exam Name
:Aruba Certified ClearPass Professional (ACCP) v6.7Certification
:HP CertificationsVendor
:HPTotal Questions
:116 Q&AsLast Updated
:Mar 28, 2025
HP HP Certifications HPE6-A68 Questions & Answers
-
Question 81:
Refer to the exhibit.
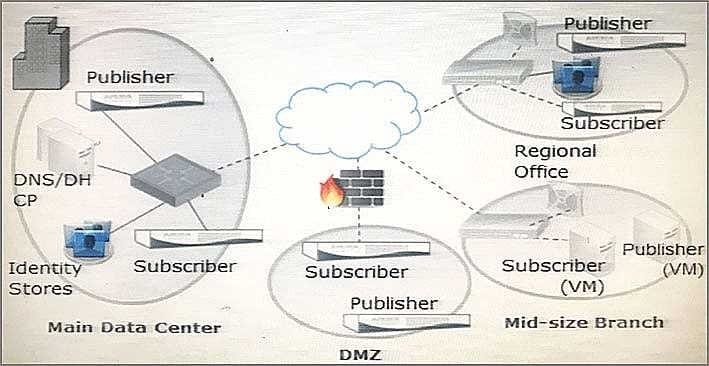
Based on the network topology diagram shown, how many clusters are needed for this deployment?
A. 1
B. 2
C. 3
D. 4
E. 8
-
Question 82:
When a third party Mobile Device Management server is integrated with ClearPass, where is the endpoint information from the MDM server stored in ClearPass?
A. Endpoints repository
B. Onboard Device repository
C. MDM repository
D. Guest User repository
E. Local User repository
-
Question 83:
Which database in the Policy Manager contains the device attributes derived by profiling?
A. Endpoints Repository
B. Client Repository
C. Local Users Repository
D. Onboard Devices Repository
E. Guest User Repository
-
Question 84:
An SNMP probe is sent from ClearPass to a network access device, but ClearPass is unable to obtain profiling information. What are likely causes? (Select three.)
A. Only SNMP read has been configured but SNMP write is needed for profiling information.
B. An external firewall is blocking SNMP traffic.
C. SNMP is not enabled on the NAD.
D. SNMP community string in the ClearPass and NAD configuration is mismatched.
E. SNMP probing is not supported between ClearPass and NADs.
-
Question 85:
Refer to the exhibit.
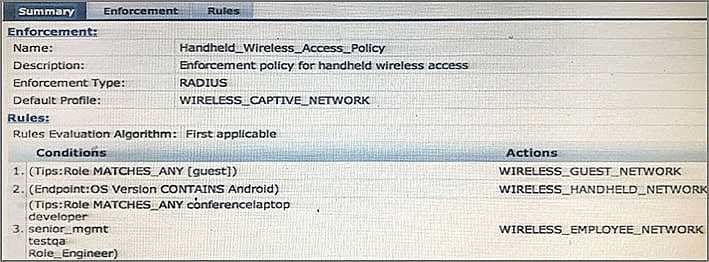
A user who is tagged with the ClearPass roles of Role_Engineer and developer, but not testqa, connects to the network with a corporate Windows laptop. Which Enforcement Profile is applied?
A. WIRELESS_GUEST_NETWORK
B. WIRELESS_CAPTIVE_NETWORK
C. WIRELESS_HANDHELD_NETWORK
D. Deny Access
E. WIRELESS_EMPLOYEE_NETWORK
-
Question 86:
Refer to the exhibit.
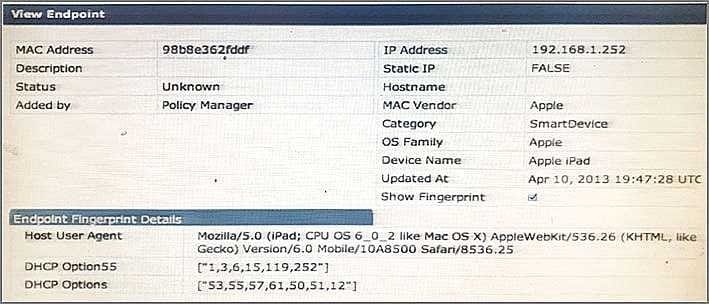
Based on the Endpoint information shown, which collectors were used to profile the device as Apple iPad? (Select two.)
A. HTTP User-Agent
B. SNMP
C. DHCP fingerprinting
D. SmartDevice
E. Onguard Agent
-
Question 87:
A ClearPass administrator wants to make Enforcement decisions during 802.1x authentication based on a client's Onguard posture token. Which Enforcement profile should be used on the health check service?
A. RADIUS CoA
B. Quarantine VLAN
C. Full Access VLAN
D. RADIUS Accept
E. RADIUS Reject
-
Question 88:
Refer to the exhibit.
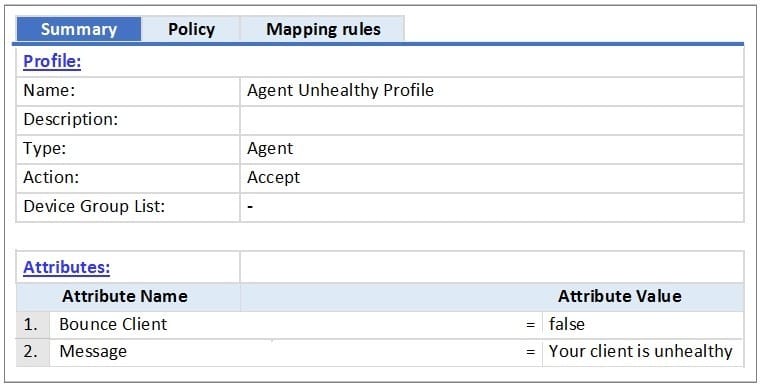
Based on the Enforcement Profile configuration shown, which statement accurately describes what is sent?
A. A limited access VLAN value is sent to the Network Access Device.
B. An unhealthy role value is sent to the Network Access Device.
C. A message is sent to the Onguard Agent on the client device.
D. A RADIUS CoA message is sent to bounce the client.
E. A RADIUS access-accept message is sent to the Controller
-
Question 89:
Why can the Onguard posture check not be performed during 802.1x authentication?
A. Health Checks cannot be used with 802.1x.
B. Onguard uses RADIUS, so an additional service must be created.
C. Onguard uses HTTPS, so an additional service must be created.
D. Onguard uses TACACS, so an additional service must be created.
E. 802.1x is already secure, so Onguard is not needed.
-
Question 90:
Refer to the exhibit.
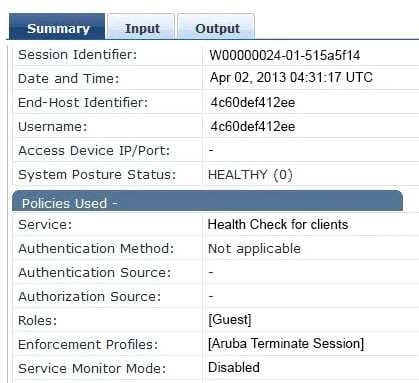
Based on the Access Tracker output for the user shown, which statement describes the status?
A. The Aruba Terminate Session enforcement profile as applied because the posture check failed.
B. A Healthy Posture Token was sent to the Policy Manager.
C. A RADIUS-Access-Accept message is sent back to the Network Access Device.
D. The authentication method used is EAP-PEAP.
E. A NAP agent was used to obtain the posture token for the user.
Related Exams:
HP0-D15
Administering HP CloudSystem Matrix SolutionsHP0-D20
Architecting the HP Matrix Operating EnvironmentHP2-E56
Selling HP SMB SolutionsHP2-H88
Selling HP Business Personal Systems Hardware 2019HP2-I14
Selling HP Supplies 2020HP2-I15
Selling HP Business Personal Systems Hardware 2020HP2-I17
Selling HP Printing Hardware 2020HP2-I44
Selling HP Workstations 2022HP2-I73
Selling HP Retail and Hospitality Solutions 2024HP2-N51
HP Application Lifecycle Management 12.x Software
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HPE6-A68 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.