Exam Details
Exam Code
:NCS-COREExam Name
:Nutanix Certified Services Core Infrastructure ProfessionalCertification
:Nutanix CertificationsVendor
:NutanixTotal Questions
:302 Q&AsLast Updated
:Mar 24, 2025
Nutanix Nutanix Certifications NCS-CORE Questions & Answers
-
Question 51:
An administrator learns that some security settings in a cluster have been changed. The environment is out ofcompliance with required policies. Which function should be used to revert any settings that have changed from the defaults and prevent further violations?
A. Cluster Lockdown with strong password enforcement
B. Advanced Intrusion Detection Environment (AIDE)
C. Security Configuration Management Automation (SCMA)
D. Defense Information Systems Agency STIG enforcement
-
Question 52:
A consultant creates a four-node AHV cluster with two 1GbE (eth0, etc1) and two 10GbE (eth2, eth3) NICs per node. The 1GbE NICs will not be placed into service, but the customer wants the network to be preconfigured for their eventual use.
The consultant removes the 1GbE NIC from the default bond and creates a second bridge(br1), but is unable to add the 1GbE NIC using the below command: manage_ovs –bridge_name br1 –interfaces 1g –bond_name br1-up update_uplinks
Which parameter is missing from this command?
A. --bond_duplex full
B. --require_link=false
C. --interfaces eth0
D. --bridge_duplex full
-
Question 53:
Refer to the exhibit.
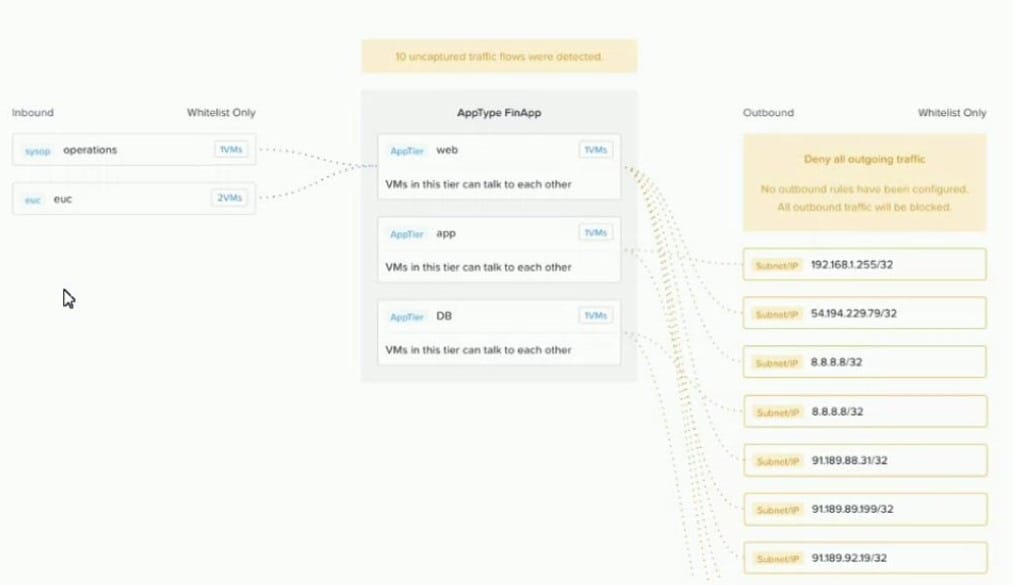
An administrator creates a security policy that isolates their financial application from accessing the Internet When viewing the policy in Prism Central, several connections from the application are outbound to the Internet. What is causing this issue with the policy?
A. The 0.0.0.0 address was not specified in the outbound rule.
B. The blockedconnections are illustrated for information only.
C. The Activate box was not checked in the rule, so it is not enforcing.
D. The policy has been left in monitor mode instead of enforcing mode.
-
Question 54:
A consultant is onsite and needs to start their Foundation Virtual Machine (FVM) to image Nutanix hardware. The FVM fails to boot. The consultant decides to use a different Foundation method. Assuming the nodes will discover, which Foundation type or configuration option should the consultant select?
A. Foundation VM
B. Use IPMI IPs
C. Use IPMI MACs
D. Foundation Applet
-
Question 55:
A customer racks all nodes in the new cluster. The customer does not allow IPv6 for node discovery. The consultant is not allowed to use the consultant's own flat switch in the customer's environment. Which step should the consultant take to resolve this issue?
A. Bare metal image all nodes with Foundation VM.
B. Image each node individually with Foundation VM.
C. Connect to the top of rack switch and discover the nodes with IPv4.
D. Open a console to all nodes and statically assign IP addresses.
-
Question 56:
Where in the Support Portal is the Best Practices guide for vSphere Networking located?
A. Product Notices
B. Solutions Documentation
C. Software Documentation
D. Knowledge Base
-
Question 57:
An administrator protected a DB VM running on a Nutanix cluster with NearSync Replication, which schedules to repeat every 15 minutes to a second site. The daily change rate is low. During nightly backups, the replication window is missed due to write volume.
Which two options describe the expected behavior? (Choose two.)
A. NearSync stops working and fails over to the remote site.
B. Protection Domain transitions back to the hourly schedule.
C. The Administrator needs to re-enable it manually.
D. The system continuously tries to get to the NearSync schedule.
-
Question 58:
An administrator responsible for a VDI environment needs to investigate reports of slow logins. Theadministrator finds that increasing the number of vCPUs from 2 to 4 will reduce the login times. Production workloads are consuming 75% of the host CPU on the cluster. The administrator increases the vCPU count on all of the VDI VMs.
What are two impacts on the cluster? (Choose two.)
A. Increase CPU utilization%
B. Increase CPU ready%
C. Increase memory utilization%
D. Increasing CPU counts will decrease memory utilization
-
Question 59:
An administrator knows that the disks in a cluster are out of date and a new firmware is available. For security reasons, these clusters do not have access to theInternet.
Which two steps must be completed to update the firmware? (Choose two.)
A. Configure LCM with a URL to access the firmware bundle.
B. Download a dark site bundle and stage it on an internal webserver.
C. Download the updated firmware .tgz file from the Nutanix portal.
D. Select Upgrade Software, then select disks and upload the updated firmware.
-
Question 60:
An administrator inherits a new Nutanix environment and logs in to a CVM to check the network configuration. The configuration is as follows:
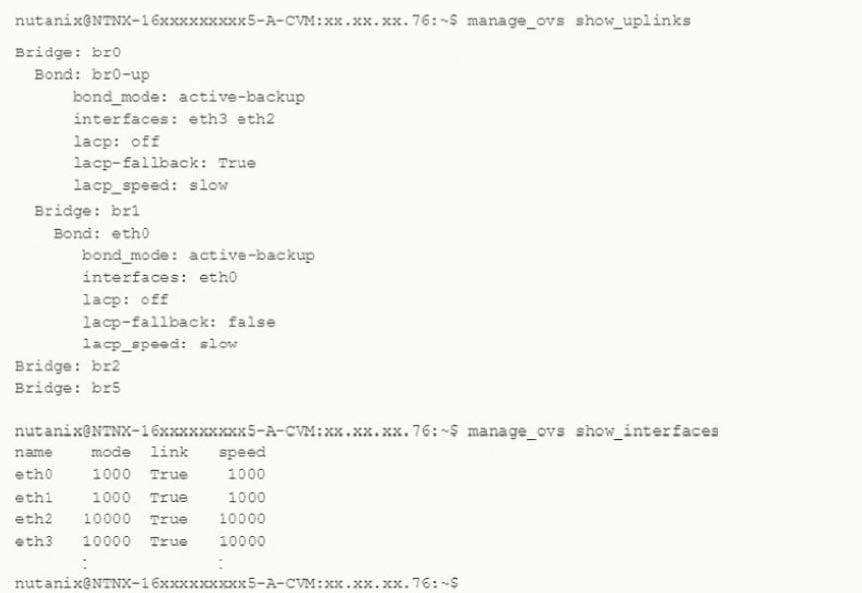
Which action should the administrator take to improve network performance?
A. Configure VLAN tagging both on br0 and br1 and their physical interfaces.
B. Add eth0 and eth1 to the br0-up bond
C. Configure balance-sib or balance-tcp mode for br0-up if switch configuration allows
D. Remove one 10 Gbs interface from br0-up to make sure all 10 Gbs can be used.
Related Exams:
NCA-5.15
Nutanix Certified Associate (NCA) v5.15NCA-5.20
Nutanix Certified Associate (NCA) v5.20NCA-6.5
Nutanix Certified Associate (NCA) v6.5NCM-5.15
Nutanix Certified Master - Multicloud Infrastructure (NCM-MCI) v5.15NCM-MCI
Nutanix Certified Master - Multicloud InfrastructureNCM-MCI-5.15
Nutanix Certified Master - Multicloud Infrastructure (NCM-MCI) v5.15NCM-MCI-5.20
Nutanix Certified Master - Multicloud Infrastructure (NCM-MCI) v5.20NCM-MCI-6.5
Nutanix Certified Master - Multicloud Infrastructure (NCM-MCI) v6.5NCP-5.10
Nutanix Certified Professional (NCP) v5.10NCP-5.15
Nutanix Certified Professional - Multi cloud Infrastructure (NCP-MCI) v5.15
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Nutanix exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your NCS-CORE exam preparations and Nutanix certification application, do not hesitate to visit our Vcedump.com to find your solutions here.