Exam Details
Exam Code
:PT0-002Exam Name
:CompTIA PenTest+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:455 Q&AsLast Updated
:Mar 28, 2025
CompTIA CompTIA Certifications PT0-002 Questions & Answers
-
Question 121:
Given the following Nmap scan command:
[root@kali ~]# nmap 192.168.0 .* -- exclude 192.168.0.101
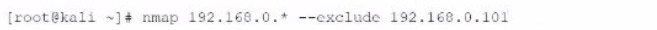
Which of the following is the total number of servers that Nmap will attempt to scan?
A. 1
B. 101
C. 255
D. 256
-
Question 122:
A penetration tester who is working remotely is conducting a penetration test using a wireless connection. Which of the following is the BEST way to provide confidentiality for the client while using this connection?
A. Configure wireless access to use a AAA server.
B. Use random MAC addresses on the penetration testing distribution.
C. Install a host-based firewall on the penetration testing distribution.
D. Connect to the penetration testing company's VPS using a VPN.
-
Question 123:
A customer adds a requirement to the scope of a penetration test that states activities can only occur during normal business hours. Which of the following BEST describes why this would be necessary?
A. To meet PCI DSS testing requirements
B. For testing of the customer's SLA with the ISP
C. Because of concerns regarding bandwidth limitations
D. To ensure someone is available if something goes wrong
-
Question 124:
A penetration tester finds a PHP script used by a web application in an unprotected internal source code repository. After reviewing the code, the tester identifies the following:
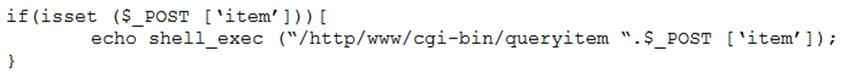
Which of the following combinations of tools would the penetration tester use to exploit this script?
A. Hydra and crunch
B. Netcat and cURL
C. Burp Suite and DIRB
D. Nmap and OWASP ZAP
-
Question 125:
A penetration tester has prepared the following phishing email for an upcoming penetration test:

Which of the following is the penetration tester using MOST to influence phishing targets to click on the link?
A. Familiarity and likeness
B. Authority and urgency
C. Scarcity and fear
D. Social proof and greed
-
Question 126:
The output from a penetration testing tool shows 100 hosts contained findings due to improper patch management. Which of the following did the penetration tester perform?
A. A vulnerability scan
B. A WHOIS lookup
C. A packet capture
D. An Nmap scan
-
Question 127:
Which of the following documents describes specific activities, deliverables, and schedules for a penetration tester?
A. NDA
B. MSA
C. SOW
D. MOU
-
Question 128:
A penetration tester runs the following command:
dig @ dns01.comptia.local axfr comptia.local
Which of the following types of information would be provided?
A. The DNSSEC certificate and CA
B. The DHCP scopes and ranges used on the network
C. The hostnames and IP addresses of internal systems
D. The OS and version of the DNS server
-
Question 129:
A penetration tester opened a shell on a laptop at a client's office but is unable to pivot because of restrictive ACLs on the wireless subnet. The tester is also aware that all laptop users have a hard-wired connection available at their desks. Which of the following is the BEST method available to pivot and gain additional access to the network?
A. Set up a captive portal with embedded malicious code.
B. Capture handshakes from wireless clients to crack.
C. Span deauthentication packets to the wireless clients.
D. Set up another access point and perform an evil twin attack.
-
Question 130:
A penetration tester is conducting an Nmap scan and wants to scan for ports without establishing a connection. The tester also wants to find version data information for services running on Projects. Which of the following Nmap commands should the tester use?
A. ..nmap -sU -sV -T4 -F target.company.com
B. ..nmap -sS -sV -F target.company.com
C. ..nmap -sT -v -T5 target.company.com
D. ..nmap -sX -sC target.company.com
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PT0-002 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.