Exam Details
Exam Code
:RC0-501Exam Name
:CompTIA Security+ Recertification ExamCertification
:CompTIA Security+Vendor
:CompTIATotal Questions
:349 Q&AsLast Updated
:Mar 29, 2025
CompTIA CompTIA Security+ RC0-501 Questions & Answers
-
Question 81:
Which of the following security controls does an iris scanner provide?
A. Logical
B. Administrative
C. Corrective
D. Physical
E. Detective
F. Deterrent
-
Question 82:
A database backup schedule consists of weekly full backups performed on Saturday at 12:00 a.m. and daily differential backups also performed at 12:00 a.m. If the database is restored on Tuesday afternoon, which of the following is the number of individual backups that would need to be applied to complete the database recovery?
A. 1
B. 2
C. 3
D. 4
-
Question 83:
A department head at a university resigned on the first day of the spring semester. It was subsequently determined that the department head deleted numerous files and directories from the server-based home directory while the campus was closed. Which of the following policies or procedures could have prevented this from occurring?
A. Time-of-day restrictions
B. Permission auditing and review
C. Offboarding
D. Account expiration
-
Question 84:
An organization is using a tool to perform a source code review. Which of the following describes the case in which the tool incorrectly identifies the vulnerability?
A. False negative
B. True negative
C. False positive
D. True positive
-
Question 85:
An organization's internal auditor discovers that large sums of money have recently been paid to a vendor that management does not recognize. The IT security department is asked to investigate the organizations the organization's ERP
system to determine how the accounts payable module has been used to make these vendor payments.
The IT security department finds the following security configuration for the accounts payable module:
New Vendor Entry ?Required Role: Accounts Payable Clerk
New Vendor Approval ?Required Role: Accounts Payable Clerk
Vendor Payment Entry ?Required Role: Accounts Payable Clerk
Vendor Payment Approval ?Required Role: Accounts Payable Manager
Which of the following changes to the security configuration of the accounts payable module would BEST mitigate the risk?
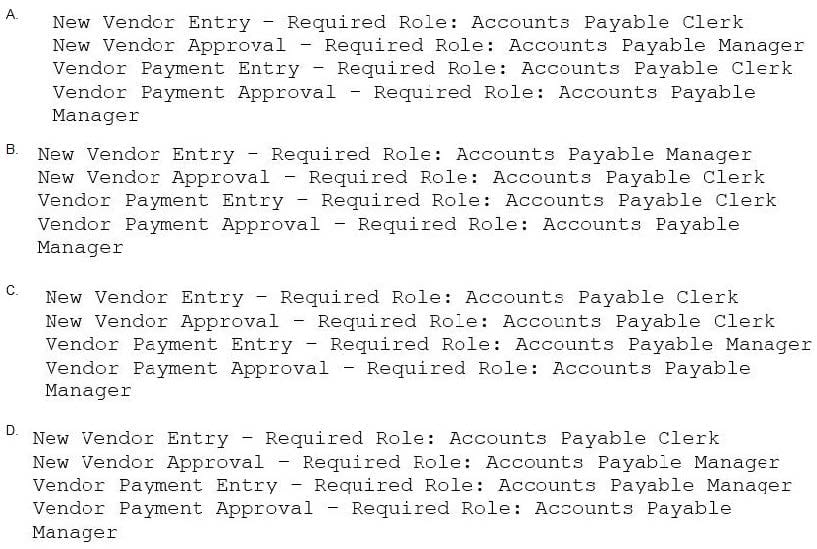
A. Option A
B. Option B
C. Option C
D. Option D
-
Question 86:
Malicious traffic from an internal network has been detected on an unauthorized port on an application server. Which of the following network-based security controls should the engineer consider implementing?
A. ACLs
B. HIPS
C. NAT
D. MAC filtering
-
Question 87:
A network administrator wants to implement a method of securing internal routing. Which of the following should the administrator implement?
A. DMZ
B. NAT
C. VPN
D. PAT
-
Question 88:
A security administrator is developing controls for creating audit trails and tracking if a PHI data breach is to occur. The administrator has been given the following requirements:
All access must be correlated to a user account.
All user accounts must be assigned to a single individual.
User access to the PHI data must be recorded.
Anomalies in PHI data access must be reported.
Logs and records cannot be deleted or modified.
Which of the following should the administrator implement to meet the above requirements? (Select three.)
A. Eliminate shared accounts.
B. Create a standard naming convention for accounts.
C. Implement usage auditing and review.
D. Enable account lockout thresholds.
E. Copy logs in real time to a secured WORM drive.
F. Implement time-of-day restrictions.
G. Perform regular permission audits and reviews.
-
Question 89:
Which of the following encryption methods does PKI typically use to securely project keys?
A. Elliptic curve
B. Digital signatures
C. Asymmetric
D. Obfuscation
-
Question 90:
Which of the following can be provided to an AAA system for the identification phase?
A. Username
B. Permissions
C. One-time token
D. Private certificate
Related Exams:
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your RC0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.