Exam Details
Exam Code
:SC-400Exam Name
:Microsoft Information Protection AdministratorCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:362 Q&AsLast Updated
:Mar 24, 2025
Microsoft Microsoft Certifications SC-400 Questions & Answers
-
Question 241:
You plan to implement inside 365 E5 subscription.
You plan to implement insider risk management for users that manage sensitive data associated with a project.
You need to create a protection policy for the users. The solution must meet the following requirements:
1.
Minimize the impact on users who are NOT part of the project.
2.
Minimize administrative effort. What should you do first?
A. From the Microsoft Entra admin center, create a security group.
B. From the Microsoft Purview compliance portal, create an insider risk management policy.
C. From the Microsoft Purview compliance portal, create a priority user group.
D. From the Microsoft Entra admin center, create a risky users policy.
-
Question 242:
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the user viewed them.
When you search the audit log in the Microsoft Purview compliance portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-Mailbox -Identity "User1" -AuditEnabled $true command.
Does that meet the goal?
A. Yes
B. No
-
Question 243:
You have a Microsoft 365 subscription.
You create and run a content search from the Microsoft Purview compliance portal.
You need to download the results of the content search.
What should you obtain first?
A. a certificate
B. a password
C. an export key
D. a pin
-
Question 244:
You have a Microsoft 365 E5 subscription.
You need to review the compliance of the subscription with the General Data Protection Regulation (GDPR) by using Compliance Manager. The solution must minimize administrative effort.
What should you create first?
A. an assessment
B. an alert policy to monitor for score changes
C. a template
D. review assessments
-
Question 245:
You have a Microsoft 365 E5 subscription that contains two users named User1 and Admin1. Admin1 manages audit retention policies for the subscription.
You need to ensure that the audit logs of User1 will be retained for 10 years.
What should you do first?
A. Assign a Microsoft Purview Audit (Premium) add-on license to User1.
B. Assign a 10-year audit log retention add-on license to Admin1.
C. Assign a Microsoft Purview Audit (Premium) add-on license to Admin1.
D. Assign a 10-year audit log retention add-on license to User1.
-
Question 246:
You have a Microsoft 365 subscription.
The Global Administrator role is assigned to your user account.
You have a user named Admin1.
You create an eDiscovery case named Case1.
You need to ensure that Admin1 can view the results of Case1.
What should you do first?
A. From the Microsoft Entra admin center, assign a role group to Admin1.
B. From the Microsoft Purview compliance portal, assign a role group to Admin1.
C. From the Microsoft 365 admin center, assign a role to Admin1.
-
Question 247:
You have a Microsoft 365 subscription linked to a Microsoft Entra tenant that contains a user named User1.
You need to grant User1 permission to search Microsoft 365 audit logs. The solution must use the principle of least privilege.
Which role should you assign to User1?
A. the Reviewer role in the Microsoft Purview compliance portal
B. the View-Only Audit Logs role in the Exchange admin center
C. the Compliance Management role in the Exchange admin center
D. the Security Reader role in the Microsoft Entra admin center
-
Question 248:
You have a Microsoft 365 E5 subscription that contains a user named User1 and a Microsoft SharePoint Online site named Site1. You create the alert policy shown in the following exhibit.
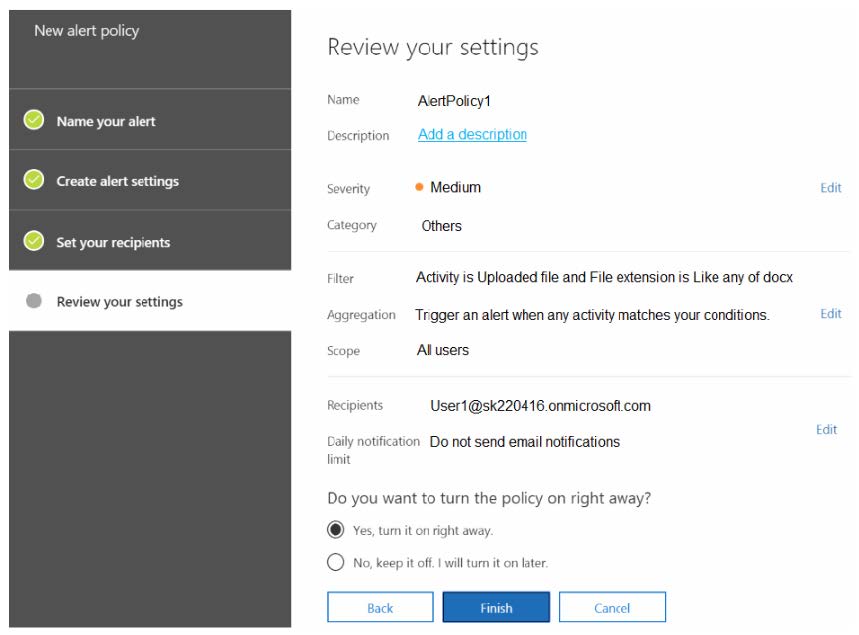
To Site1, User1 uploads the files shown in the following table.
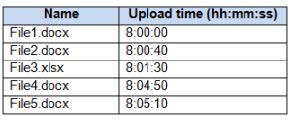
How many alerts will be generated in response to the file uploads?
A. 1
B. 2
C. 3
D. 4
E. 5
-
Question 249:
You have a Microsoft 365 subscription.
A. Recipients: “user””#1-2””@contoso.com”
B. Recipients: (“[email protected]” “[email protected]”)
C. Recipients: (“user””#1-1””@contoso.com”)
D. Recipients= “[email protected]” OR Recipients= “[email protected]”
-
Question 250:
You have a Microsoft 365 E5 tenant that has data loss prevention (DLP) policies.
You need to create a report that includes the following:
1.
Documents that have a matched DLP policy.
2.
Documents that have had a sensitivity label changed.
3.
Documents that have had a sensitivity label changed.
What should you use?
A. a content search
B. an eDiscovery case
C. communication compliance reports
D. Activity explorer
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SC-400 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.