Exam Details
Exam Code
:SC-900Exam Name
:Microsoft Security Compliance and Identity FundamentalsCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:242 Q&AsLast Updated
:Mar 29, 2025
Microsoft Microsoft Certifications SC-900 Questions & Answers
-
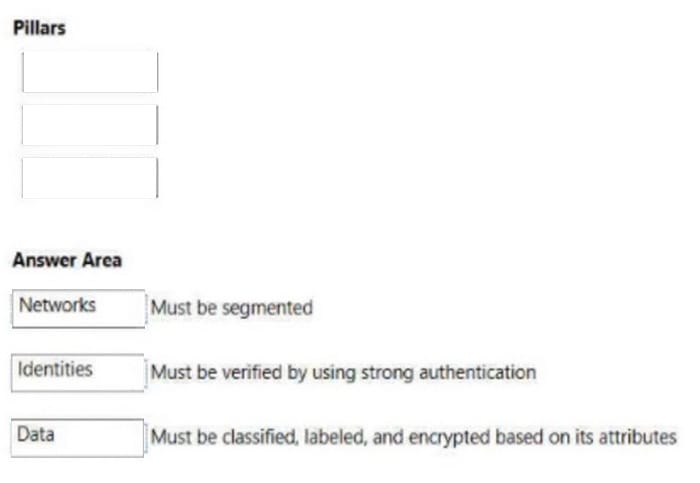
Question 111:
DRAG DROP
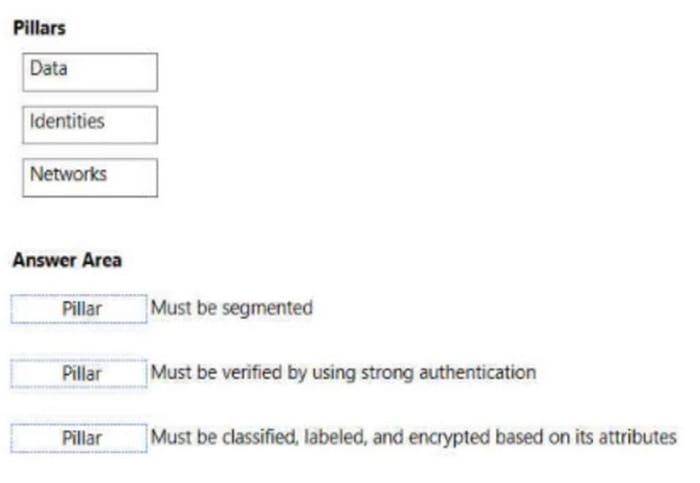
Match the pillars of Zero Trust to the appropriate requirements.
To answer, drag the appropriate pillar from the column on the left to its requirement on the right. Each pillar may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
Select and Place:
-
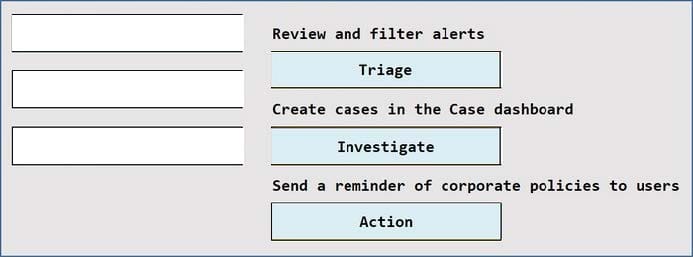
Question 112:
DRAG DROP
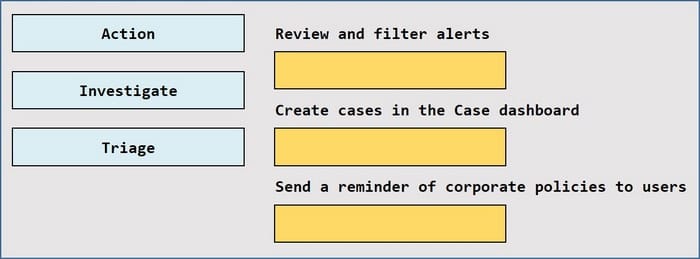
Match the Microsoft 365 insider risk management workflow step to the appropriate task.
To answer, drag the appropriate step from the column on the left to its task on the right. Each step may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
Select and Place:
-
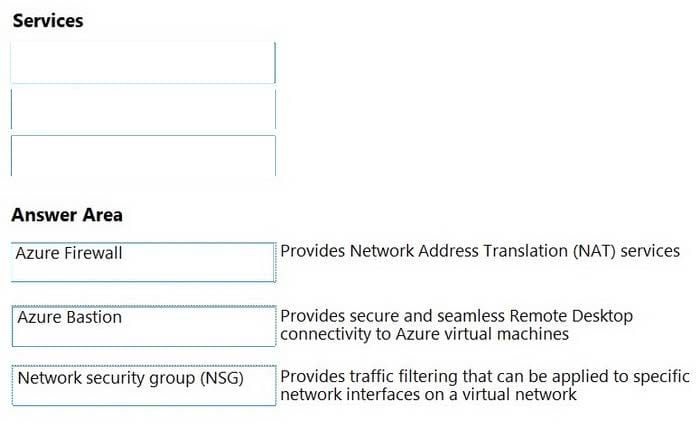
Question 113:
DRAG DROP
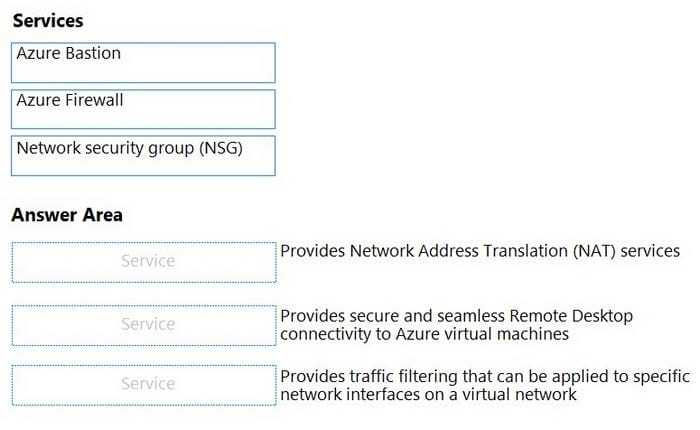
Match the Azure networking service to the appropriate description.
To answer, drag the appropriate service from the column on the left to its description on the right. Each service may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
Select and Place:
-
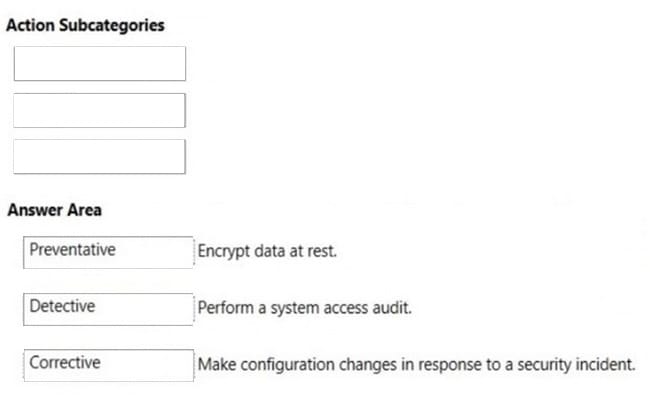
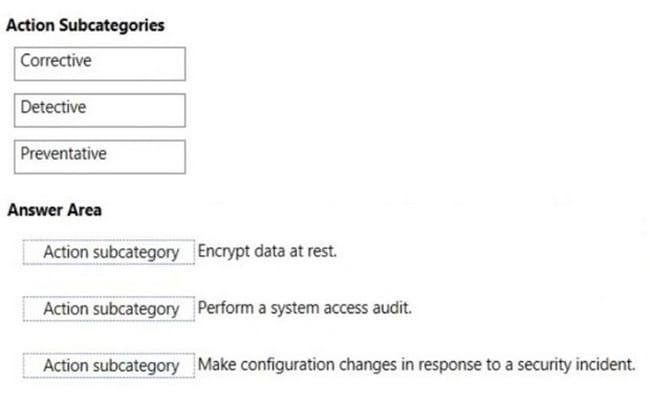
Question 114:
DRAG DROP
You are evaluating the compliance score in Compliance Manager.
Match the compliance score action subcategories to the appropriate actions.
To answer, drag the appropriate action subcategory from the column on the left to its action on the right. Each action subcategory may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
Select and Place:
-
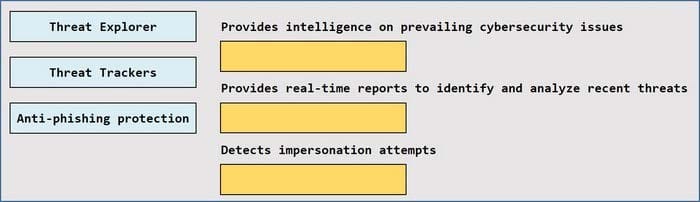
Question 115:
DRAG DROP
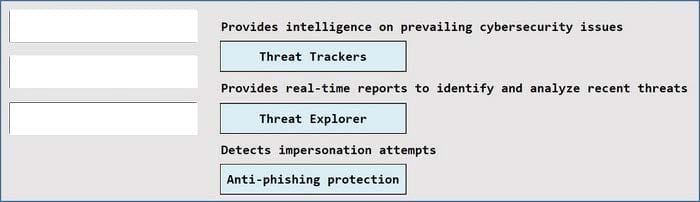
Match the Microsoft Defender for Office 365 feature to the correct description.
To answer, drag the appropriate feature from the column on the left to its description on the right. Each feature may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
Select and Place:
-
Question 116:
Which three tasks can be performed by using Azure Active Directory (Azure AD) Identity Protection? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
A. Configure external access for partner organizations.
B. Export risk detection to third-party utilities.
C. Automate the detection and remediation of identity based-risks.
D. Investigate risks that relate to user authentication.
E. Create and automatically assign sensitivity labels to data.
-
Question 117:
Which two Azure resources can a network security group (NSG) be associated with? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
A. a network interface
B. an Azure App Service web app
C. a virtual network
D. a virtual network subnet
E. E. a resource group
-
Question 118:
What is an assessment in Compliance Manager?
A. A grouping of controls from a specific regulation, standard or policy.
B. Recommended guidance to help organizations align with their corporate standards.
C. A dictionary of words that are not allowed in company documents.
D. A policy initiative that includes multiple policies.
-
Question 119:
What should you use to ensure that the members of an Azure Active Directory group use multi-factor authentication (MFA) when they sign in?
A. Azure Active Directory (Azure AD) Identity Protection
B. a conditional access policy
C. Azure role-based access control (Azure RBAC)
D. Azure Active Directory (Azure AD) Privileged Identity Management (PIM)
-
Question 120:
You need to keep a copy of all files in a Microsoft SharePoint site for one year, even if users delete the files from the site. What should you apply to the site?
A. a data loss prevention (DLP) policy
B. a retention policy
C. an insider risk policy
D. a sensitivity label policy
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SC-900 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.