Exam Details
Exam Code
:SY0-501Exam Name
:CompTIA Security+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:1423 Q&AsLast Updated
:Sep 04, 2023
CompTIA CompTIA Certifications SY0-501 Questions & Answers
-
Question 1381:
A security analyst is reviewing the following output from an IPS:
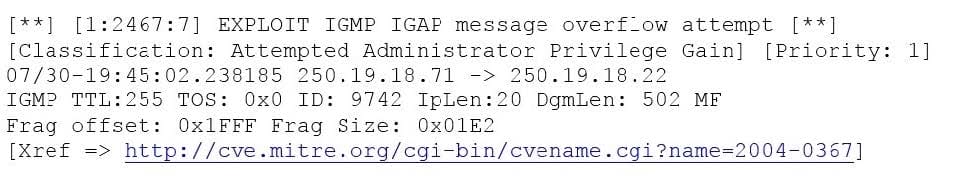
Given this output, which of the following can be concluded? (Select two.)
A. The source IP of the attack is coming from 250.19.18.22.
B. The source IP of the attack is coming from 250.19.18.71.
C. The attacker sent a malformed IGAP packet, triggering the alert.
D. The attacker sent a malformed TCP packet, triggering the alert.
E. The TTL value is outside of the expected range, triggering the alert.
-
Question 1382:
An organization has determined it can tolerate a maximum of three hours of downtime. Which of the following has been specified?
A. RTO
B. RPO
C. MTBF
D. MTTR
-
Question 1383:
Multiple employees receive an email with a malicious attachment that begins to encrypt their hard drives and mapped shares on their devices when it is opened. The network and security teams perform the following actions:
Shut down all network shares.
Run an email search identifying all employees who received the malicious message.
Reimage all devices belonging to users who opened the attachment. Next, the teams want to re-enable the network shares.
Which of the following BEST describes this phase of the incident response process?
A. Eradication
B. Containment
C. Recovery
D. Lessons learned
-
Question 1384:
Refer to the following code:
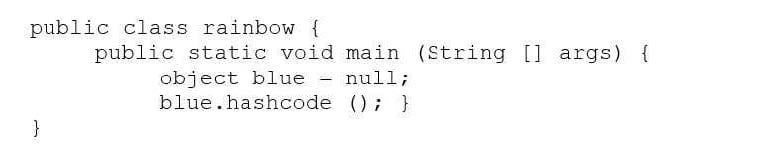
Which of the following vulnerabilities would occur if this is executed?
A. Page exception
B. Pointer deference
C. NullPointerException
D. Missing null check
-
Question 1385:
Which of the following explains why vendors publish MD5 values when they provide software patches for their customers to download over the Internet?
A. The recipient can verify integrity of the software patch.
B. The recipient can verify the authenticity of the site used to download the patch.
C. The recipient can request future updates to the software using the published MD5 value.
D. The recipient can successfully activate the new software patch.
-
Question 1386:
A security analyst wishes to increase the security of an FTP server. Currently, all traffic to the FTP server is unencrypted. Users connecting to the FTP server use a variety of modern FTP client software. The security analyst wants to keep the same port and protocol, while also still allowing unencrypted connections. Which of the following would BEST accomplish these goals?
A. Require the SFTP protocol to connect to the file server.
B. Use implicit TLS on the FTP server.
C. Use explicit FTPS for connections.
D. Use SSH tunneling to encrypt the FTP traffic.
-
Question 1387:
Which of the following best describes routine in which semicolons, dashes, quotes, and commas are removed from a string?
A. Error handling to protect against program exploitation
B. Exception handling to protect against XSRF attacks.
C. Input validation to protect against SQL injection.
D. Padding to protect against string buffer overflows.
-
Question 1388:
Which of the following threat actors is MOST likely to steal a company's proprietary information to gain a market edge and reduce time to market?
A. Competitor
B. Hacktivist
C. Insider
D. Organized crime.
-
Question 1389:
A penetration tester is crawling a target website that is available to the public. Which of the following represents the actions the penetration tester is performing?
A. URL hijacking
B. Reconnaissance
C. White box testing
D. Escalation of privilege
-
Question 1390:
Which of the following characteristics differentiate a rainbow table attack from a brute force attack? (Select two.)
A. Rainbow table attacks greatly reduce compute cycles at attack time.
B. Rainbow tables must include precomputed hashes.
C. Rainbow table attacks do not require access to hashed passwords.
D. Rainbow table attacks must be performed on the network.
E. Rainbow table attacks bypass maximum failed login restrictions.
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.