Exam Details
Exam Code
:300-620Exam Name
:Implementing Cisco Application Centric Infrastructure (DCACI)Certification
:CCNP Data CenterVendor
:CiscoTotal Questions
:309 Q&AsLast Updated
:Mar 28, 2025
Cisco CCNP Data Center 300-620 Questions & Answers
-
Question 131:
Refer to the exhibit.
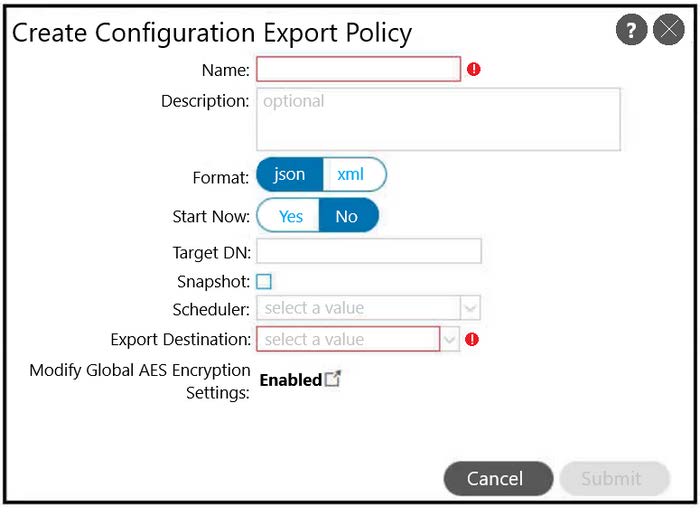
A customer must back up the current Cisco ACI configuration securely to the remote location using encryption and authentication. The backup job must run once per day. The customer's security policy mandates that any sensitive information including passwords must not be exported from the device. Which set of steps meets these requirements?
A. Export destination using FTP protocol. Use XML format.
B. Export destination using FTP protocol. Disable Global AES Encryption.
C. Export destination using SCP protocol. Disable Global AES Encryption.
D. Export destination using SCP protocol. Use XML format.
-
Question 132:
A Cisco APIC is configured with RADIUS authentication as the default. The network administrator must ensure that users can access the APIC GUI with a local account if the RADIUS server is unreachable. Which action must be taken to accomplish this goal?
A. Associate console authentication with the "RADIUS" realm
B. Reference the "local" realm in the fallback domain
C. Create an additional login domain that references local accounts
D. Enable the fallback check with the default authentication domain
-
Question 133:
Refer to the exhibit A Cisco ACI fabric is using out-of-band management connectivity. The APIC must access a routable host with an IP address of 192.168.11.2. Which action accomplishes this goal?
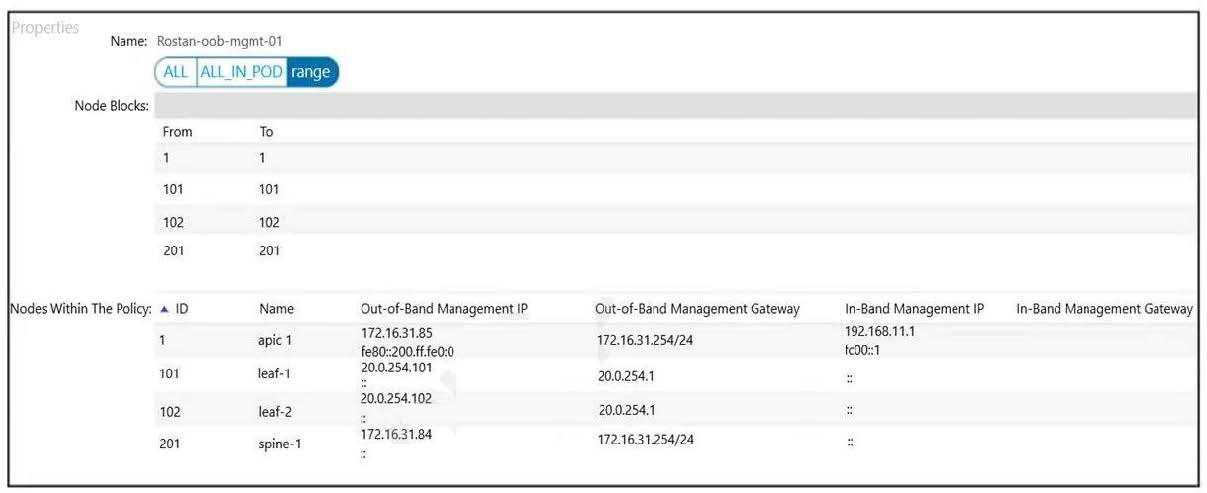
A. Change the switch APIC Connectivity Preference to in-band management
B. Modify the Pod Profile to use the default Management Access Policy
C. Add a Fabric Access Policy to allow management connections
D. Remove the in-band management address from the APIC
-
Question 134:
An engineer must securely export Cisco APIC configuration snapshots to a secure, offsite location The exported configuration must be transferred using an encrypted tunnel and encoded with a platform-agnostic data format that provides namespace support. Which configuration set must be used?
A. Policy: Export Policy Protocol: TLS Format: JSON
B. Policy: Import Policy Protocol: TLS Format: XML
C. Policy: Import Policy Protocol: SCP Format: JSON
D. Policy: Export Policy Protocol: SCP Format: XML
-
Question 135:
A network engineer must allow secure access to the Cisco ACI out-of-band (OOB) management only from external subnets 10.0.0.0/24 and 192.168.20.0/25. Which configuration set accomplishes this goal?
A. Create a L3Out in the MGMT tenant in OOB VRF. Set External Management Network Instance Profile as a consumer of the OOB contract. Create an External EPG with two subnet entries with the external subnets.
B. Create a PBR service graph in the MGMT tenant. Create a management Profile with the required OOB EPG. Redirect all traffic going into ACI management to the external firewall. Create two subnet entries under the OOB Bridge domain with the required subnets.
C. Create an EPG and BD in the MGMT tenant in OOB VRF. Set OOB VRF to provide the contract. Set a new EPG to consume the OOB contract.
D. Create an OOB contract that allows the required ports. Provide the contract from the OOB EPG. Consume the contract by the OOB External Management Network Instance Profile. Create two subnet entries in the External Management Network Profile with the required subnets.
-
Question 136:
The Application team reports that a previously existing port group has disappeared from vCenter. An engineer confirms that the VMM domain association for the EPG is no longer present. Which action determines which user is responsible for the change?
A. Check the EPG audit logs for the "deletion" action and compare the affected object and user.
B. Evaluate the potential faults that are raised for that EPG.
C. Examine the health score and drill down to an object that affects the EPG combined score.
D. Inspect the server logs to see who was logging in to the APIC during the last few hours.
-
Question 137:
An application team tells the Cisco ACI network administrator that it wants to monitor the statistics of the unicast and BUM traffic that are seen in a certain EPG. Which statement describes the collection statistics?
A. All EPGs in the Cisco ACI tenant object must be enabled for statistics to be collected.
B. Cisco ACI does not capture statistics at the EPG level. Only statistics that pass through ACI contracts can be monitored.
C. EPG statistics can be collected only for VMM domains. If a physical domain exists, statistics are not collected.
D. The collection of statistics is enabled on the EPG level by enabling the statistics for unicast and BUM traffic.
-
Question 138:
A network engineer must backup the PRODUCTION tenant. The configuration backup should be stored on the APIC using a markup language and contain all secure information. Which export policy must be used to meet these requirement?
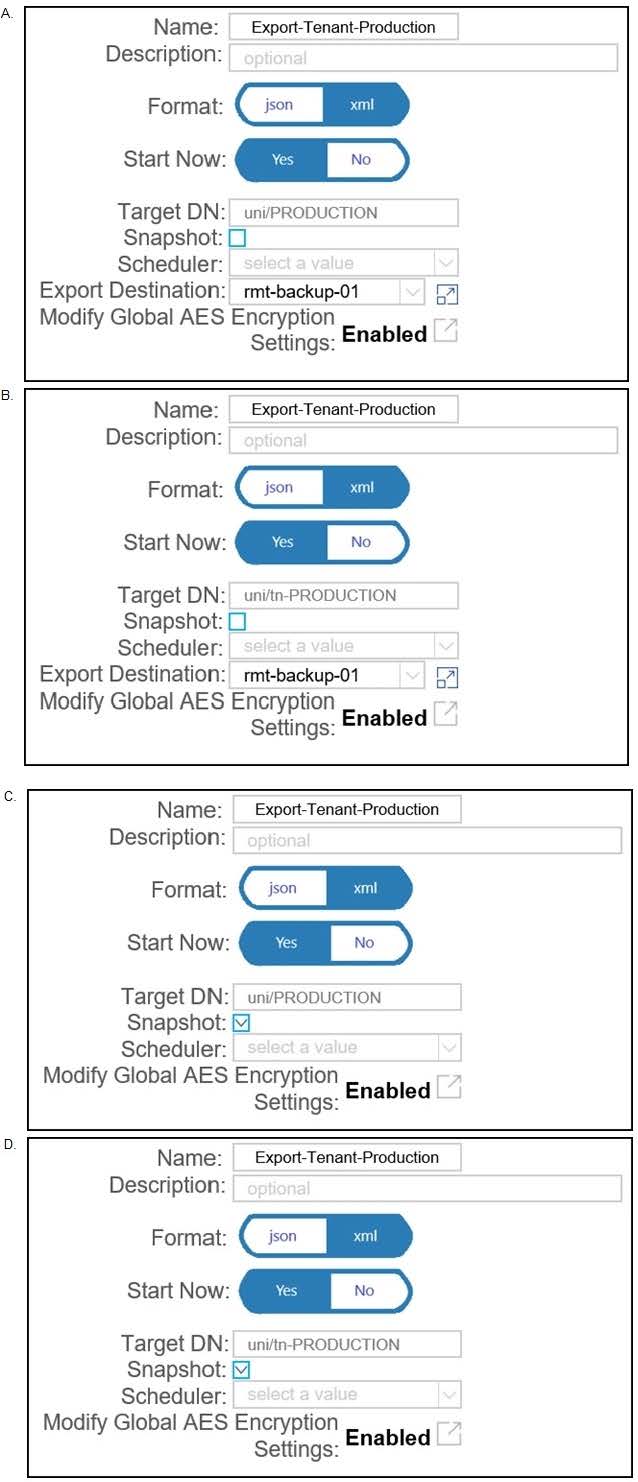
A. Option A
B. Option B
C. Option C
D. Option D
-
Question 139:
An administrator must migrate the vSphere Management VMkernel of all ESXi hosts in the production cluster from the standard default virtual switch to a VDS that is integrated with APIC in a VMM domain. Which action must be completed in this scenario?
A. The Management VMkernel EPG resolution must be set to Pre-Provision.
B. The administrator must create an in-band VMM Management EPG before performing the migration.
C. The administrator must set the Management VMkernel BD resolution immediacy to On-Demand.
D. The VMkernel Management BD must be located under the Management Tenant.
-
Question 140:
An engineer must create a backup of the Cisco ACI fabric for disaster recovery purposes. The backup must be transferred over a secure and encrypted transport. The backup file must contain all user and password related information. The engineer also wants to process and confirm the backup file validity by using a Python script. This requires the data structure to have a format similar to a Python dictionary. Which configuration set must be used to meet these requirements?
A. Under the Create Remote location settings, select Protocol: FTP Under the Export policy, select
-Format: XML
-Modify Global AES Encryption Settings: Enabled
B. Under the Create Remote location settings, select Protocol: FTP Under the Export policy, select
-Format: XML
-Modify Global AES Encryption Settings: Disabled
C. Under the Create Remote location settings, select Protocol: SCP Under the Export policy, select
-Format: JSON
-Modify Global AES Encryption Settings: Disabled
D. Under the Create Remote location settings, select Protocol: SCP Under the Export policy, select
-Format: JSON
-Modify Global AES Encryption Settings: Enabled
Related Exams:
300-610
Designing Cisco Data Center Infrastructure (DCID)300-615
Troubleshooting Cisco Data Center Infrastructure (DCIT)300-620
Implementing Cisco Application Centric Infrastructure (DCACI)300-630
Implementing Cisco Application Centric Infrastructure - Advanced (DCACIA)300-635
Automating and Programming Cisco Data Center Solutions (DCAUTO)350-601
Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 300-620 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.