Exam Details
Exam Code
:412-79V8Exam Name
:EC-Council Certified Security Analyst (ECSA)Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:200 Q&AsLast Updated
:
EC-COUNCIL EC-COUNCIL Certifications 412-79V8 Questions & Answers
-
Question 121:
Which of the following attacks is an offline attack?
A. Pre-Computed Hashes
B. Hash Injection Attack
C. Password Guessing
D. Dumpster Diving
-
Question 122:
Transmission control protocol accepts data from a data stream, divides it into chunks, and adds a TCP header creating a TCP segment. The TCP header is the first 24 bytes of a TCP segment that contains the parameters and state of an endto-end TCP socket. It is used to track the state of communication between two TCP endpoints. For a connection to be established or initialized, the two hosts must synchronize. The synchronization requires each side to send its own initial sequence number and to receive a confirmation of exchange in an acknowledgment (ACK) from the other side The below diagram shows the TCP Header format:
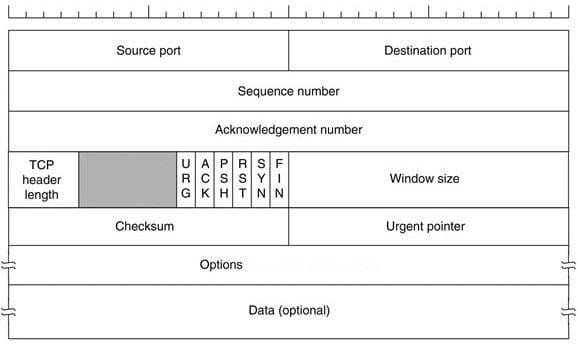
How many bits is a acknowledgement number?
A. 16 bits
B. 32 bits
C. 8 bits
D. 24 bits
-
Question 123:
Choose the correct option to define the Prefix Length.
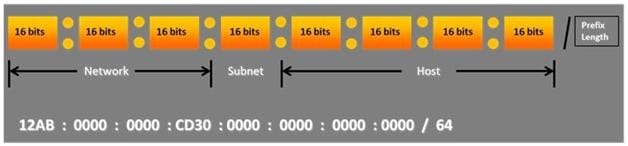
A. Prefix Length = Subnet + Host portions
B. Prefix Length = Network + Host portions
C. Prefix Length = Network + Subnet portions
D. Prefix Length = Network + Subnet + Host portions
-
Question 124:
Which of the following pen testing reports provides detailed information about all the tasks performed during penetration testing?
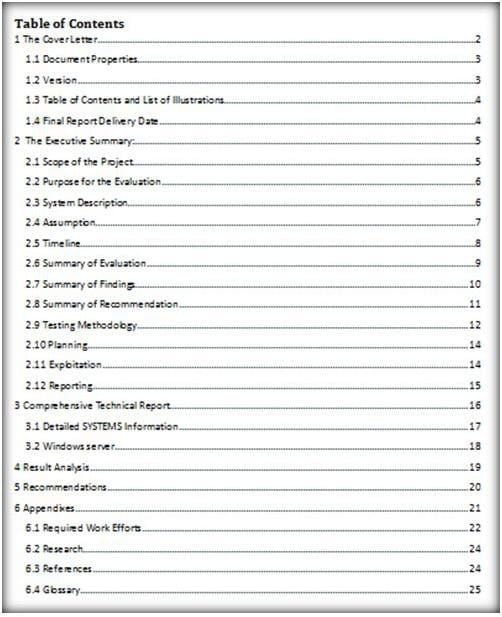
A. Client-Side Test Report
B. Activity Report
C. Host Report
D. Vulnerability Report
-
Question 125:
The Internet is a giant database where people store some of their most private information on the cloud, trusting that the service provider can keep it all safe. Trojans, Viruses, DoS attacks, website defacement, lost computers, accidental publishing, and more have all been sources of major leaks over the last 15 years.
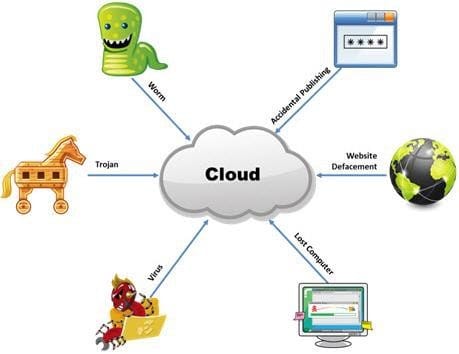
What is the biggest source of data leaks in organizations today?
A. Weak passwords and lack of identity management
B. Insufficient IT security budget
C. Rogue employees and insider attacks
D. Vulnerabilities, risks, and threats facing Web sites
-
Question 126:
A man enters a PIN number at an ATM machine, being unaware that the person next to him was watching. Which of the following social engineering techniques refers to this type of information theft?
A. Shoulder surfing
B. Phishing
C. Insider Accomplice
D. Vishing
-
Question 127:
Identify the person who will lead the penetration-testing project and be the client point of contact.
A. Database Penetration Tester
B. Policy Penetration Tester
C. Chief Penetration Tester
D. Application Penetration Tester
-
Question 128:
Due to illegal inputs, various types of TCP stacks respond in a different manner. Some IDSs do not take into account the TCP protocol's urgency feature, which could allow testers to evade the IDS.

Penetration tester needs to try different combinations of TCP flags (e.g. none, SYN/FIN, SYN/RST, SYN/ FIN/ACK, SYN/RST/ACK, and All Flags) to test the IDS. Which of the following TCP flag combinations combines the problem of initiation, midstream, and termination flags with the PSH and URG?
A. SYN/RST/ACK
B. SYN/FIN/ACK
C. SYN/FIN
D. All Flags
-
Question 129:
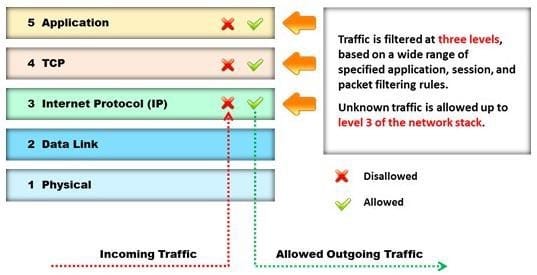
Identify the type of firewall represented in the diagram below: A. Stateful multilayer inspection firewall
B. Application level gateway
C. Packet filter
D. Circuit level gateway
-
Question 130:
Identify the correct formula for Return on Investment (ROI).
A. ROI = ((Expected Returns Cost of Investment) / Cost of Investment) * 100
B. ROI = (Expected Returns + Cost of Investment) / Cost of Investment
C. ROI = (Expected Returns - Cost of Investment) / Cost of Investment
D. ROI = ((Expected Returns + Cost of Investment) / Cost of Investment) * 100
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 412-79V8 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.