Exam Details
Exam Code
:98-367Exam Name
:Security FundamentalsCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:277 Q&AsLast Updated
:Mar 25, 2025
Microsoft Microsoft Certifications 98-367 Questions & Answers
-
Question 201:
A brute force attack:
A. Uses response filtering
B. Tries all possible password variations
C. Uses the strongest possible algorithms
D. Targets all the ports
-
Question 202:
You create a web server for your school. When users visit your site, they get a certificate error that says your site is not trusted.
What should you do to fix this problem?
A. Install a certificate from a trusted Certificate Authority (CA).
B. Use a digital signature.
C. Generate a certificate request.
D. Enable Public Keys on your website.
-
Question 203:
The default password length for a Windows Server domain controller is:
A. 0
B. 5
C. 7
D. 14
-
Question 204:
What does NAT do?
A. It encrypts and authenticates IP packets.
B. It provides caching and reduces network traffic.
C. It translates public IP addresses to private addresses and vice versa.
D. It analyzes incoming and outgoing traffic packets.
-
Question 205:
You are trying to connect to an FTP server on the Internet from a computer in a school lab. You cannot get a connection. You try on another computer with the same results. The computers in the lab are able to browse the Internet.
You are able to connect to this FTP server from home.
What could be blocking the connection to the server?
A. A layer-2 switch
B. A wireless access point
C. A firewall
D. A layer-2 hub
-
Question 206:
You are setting up Remote Desktop on your computer. Your computer is a member of a domain. Your firewall configuration is shown in the following image:
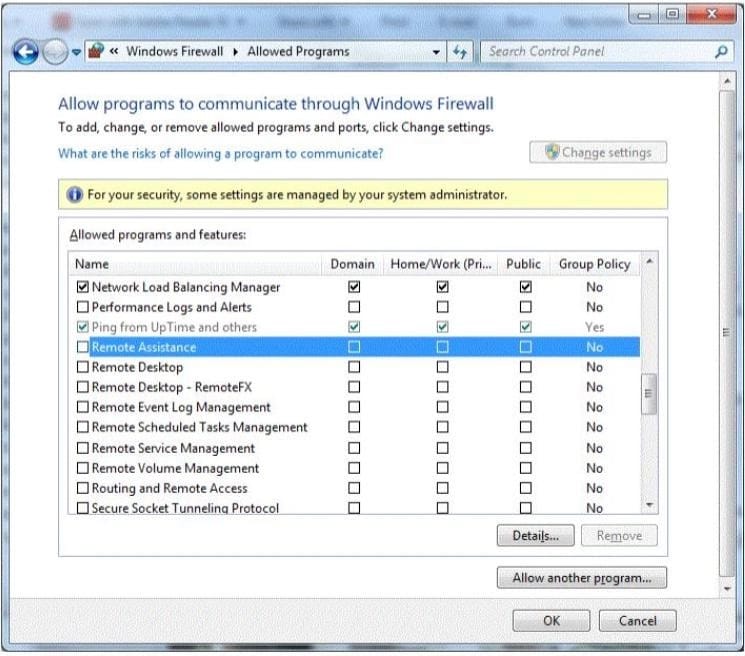
You need to allow Remote Desktop to be able to get through your firewall for users on your company's network. Which settings should you enable?
A. Remote Assistance: Home/Work (Private)
B. Remote Desktop: Public
C. Remote Desktop: Home/Work (Private)
D. Remote Assistance: Domain
-
Question 207:
The primary method of authentication in an SSL connection is passwords.
To answer, choose the option "No change is needed" if the underlined text is correct. If the underlined text is not correct, choose the correct answer.
A. No change is needed
B. Certificates
C. IPsec
D. Biometrics
-
Question 208:
What is a common method for password collection?
A. Email attachments
B. Back door intrusions
C. SQL Injection
D. Network sniffers
-
Question 209:
Which provides the highest level of security in a firewall?
A. Stateful inspection
B. Outbound packet filters
C. Stateless inspection
D. Inbound packet filters
-
Question 210:
Before you deploy Network Access Protection (NAP), you must install:
A. Internet Information Server (IIS)
B. Network Policy Server (NPS)
C. Active Directory Federation Services
D. Windows Update Service
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 98-367 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.