Exam Details
Exam Code
:CAS-004Exam Name
:CompTIA Advanced Security Practitioner (CASP+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:743 Q&AsLast Updated
:Mar 30, 2025
CompTIA CompTIA Certifications CAS-004 Questions & Answers
-
Question 81:
A company is in the process of refreshing its entire infrastructure The company has a business-critical process running on an old 2008 Windows server If this server fails, the company would lose millions of dollars in revenue. Which of the following actions should the company should take?
A. Accept the risk as the cost of doing business
B. Create an organizational risk register for project prioritization
C. Calculate the ALE and conduct a cost-benefit analysis
D. Purchase insurance to offset the cost if a failure occurred
-
Question 82:
A security analyst has been provided the following partial Snort IDS rule to review and add into the company's Snort IDS to identify a CVE:
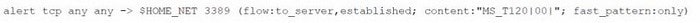
alert tcp any any -> $HOME_NET 3389 (flow:to_server,established; content:"MS_T120|00|"; fasc_pattern:only)
Which of the following should the analyst recommend to mitigate this type of vulnerability?
A. IPSec rules
B. OS patching
C. Two-factor authentication
D. TCP wrappers
-
Question 83:
A cyberanalyst for a government agency is concerned about how Pll is protected A supervisor indicates that a Privacy Impact Assessment must be done. Which of the following describes a function of a Privacy Impact Assessment?
A. To validate the project participants
B. To identify the network ports
C. To document residual risks
D. To evaluate threat acceptance
-
Question 84:
Which of the following best describes what happens if chain of custody is broken?
A. Tracking record details are not properly labeled.
B. Vital evidence could be deemed inadmissible.
C. Evidence is not exhibited in the court of law.
D. Evidence will need to be recollected.
-
Question 85:
A security administrator needs to recommend an encryption protocol after a legacy stream cipher was deprecated when a security flaw was discovered. The legacy cipher excelled at maintaining strong cryptographic security and provided great performance for a streaming video service. Which of the following AES modes should the security administrator recommend given these requirements?
A. CTR
B. ECB
C. OF8
D. GCM
-
Question 86:
A security engineer is assessing the security controls of loT systems that are no longer supported for updates and patching. Which of the following is the best mitigation for defending these loT systems?
A. Disable administrator accounts
B. Enable SELinux
C. Enforce network segmentation
D. Assign static IP addresses
-
Question 87:
A software development company wants to ensure that users can confirm the software is legitimate when installing it. Which of the following is the best way for the company to achieve this security objective?
A. Code signing
B. Non-repudiation
C. Key escrow
D. Private keys
-
Question 88:
A small bank is evaluating different methods to address and resolve the following requirements
1.
Must be able to store credit card data using the smallest amount of data possible
2.
Must be compliant with PCI DSS
3.
Must maintain confidentiality if one piece of the layer is compromised
Which of the following is the best solution for the bank?
A. Scrubbing
B. Tokenization
C. Masking
D. Homomorphic encryption
-
Question 89:
A PKI engineer is defining certificate templates for an organization's CA and would like to ensure at least two of the possible SAN certificate extension fields populate for documentation purposes. Which of the following are explicit options within this extension? (Select two).
A. Type
B. Email
C. OCSP responder
D. Registration authority
E. Common Name
F. DNS name
-
Question 90:
During a review of events, a security analyst notes that several log entries from the FIM system identify changes to firewall rule sets. While coordinating a response to the FIM entries, the analyst receives alerts from the DLP system that indicate an employee is sending sensitive data to an external email address. Which of the following would be the most relevant to review in order to gain a better understanding of whether these events are associated with an attack?
A. Configuration management tool
B. Intrusion prevention system
C. Mobile device management platform
D. Firewall access control list
E. NetFlow logs
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CAS-004 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.