Exam Details
Exam Code
:CAS-004Exam Name
:CompTIA Advanced Security Practitioner (CASP+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:740 Q&AsLast Updated
:Jun 29, 2025
CompTIA CompTIA Certifications CAS-004 Questions & Answers
-
Question 91:
A security administrator wants to enable a feature that would prevent a compromised encryption key from being used to decrypt all the VPN traffic. Which of the following should the security administrator use?
A. Salsa20 cipher
B. TLS-based VPN
C. PKI-based IKE IPSec negotiation
D. Perfect forward secrecy
-
Question 92:
An organization is designing a MAC scheme (or critical servers running GNU/Linux. The security engineer is investigating SELinux but is confused about how to read labeling contexts. The engineer executes the command stat ./secretfile and receives the following output:
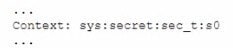
Which of the following describes the correct order of labels shown in the output above?
A. Role, type MLS level, and user identity
B. Role, user identity, object, and MLS level
C. Object MLS level, role, and type
D. User identity, role, type, and MLS level
E. Object, user identity, role, and MLS level
-
Question 93:
A company with only U S -based customers wants to allow developers from another country to work on the company's website However, the company plans to block normal internet traffic from the other country Which of the following strategies should the company use to accomplish this objective? (Select two).
A. Block foreign IP addresses from accessing the website
B. Have the developers use the company's VPN
C. Implement a WAP for the website
D. Give the developers access to a jump box on the network
E. Employ a reverse proxy for the developers
F. Use NAT to enable access for the developers
-
Question 94:
Which of the following is record-level encryption commonly used to do?
A. Protect database fields
B. Protect individual files
C. Encrypt individual packets
D. Encrypt the master boot record
-
Question 95:
A network security engineer is designing a three-tier web architecture that will allow a third- party vendor to perform the following audit functions within the organization's cloud environment
1.
Review communication between all infrastructure endpoints
2.
Identify unauthorized and malicious data patterns
3.
Perform automated, risk-mitigating configuration changes
Which of the following should the network security engineer include in the design to address these requirements?
A. Network edge NIPS
B. Centralized syslog
C. Traffic mirroring
D. Network flow
-
Question 96:
An IT department is currently working to implement an enterprise DLP solution. Due diligence and best practices must be followed in regard to mitigating risk. Which of the following ensures that authorized modifications are well planned and executed?
A. Risk management
B. Network management
C. Configuration management
D. Change management
-
Question 97:
A senior security analyst is helping the development team improve the security of an application that is being developed. The developers use third-party libraries and applications. The software in development used old, third-party packages that were not replaced before market distribution. Which of the following should be implemented into the SDLC to resolve the issue?
A. Software composition analysis
B. A SCAP scanner
C. ASAST
D. A DAST
-
Question 98:
During a network defense engagement, a red team is able to edit the following registry key:
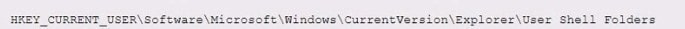
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Which of the following tools is the red team using to perform this action?
A. PowerShell
B. SCAP scanner
C. Network vulnerability scanner
D. Fuzzer
-
Question 99:
A company with customers in the United States and Europe wants to ensure its content is delivered to end users with low latency. Content includes both sensitive and public information. The company's data centers are located on the West Coast of the United States. Users on the East Coast of the United States and users in Europe are experiencing slow application response. Which of the following would allow the company to improve application response quickly?
A. Installing reverse caching proxies in both data centers and implementing proxy auto scaling
B. Using HTTPS to serve sensitive content and HTTP for public content
C. Using colocation services in regions where the application response is slow
D. Implementing a CDN and forcing all traffic through the CDN
-
Question 100:
A company recently deployed a SIEM and began importing logs from a firewall, a file server, a domain controller a web server, and a laptop. A security analyst receives a series of SIEM alerts and prepares to respond. The following is the alert information:
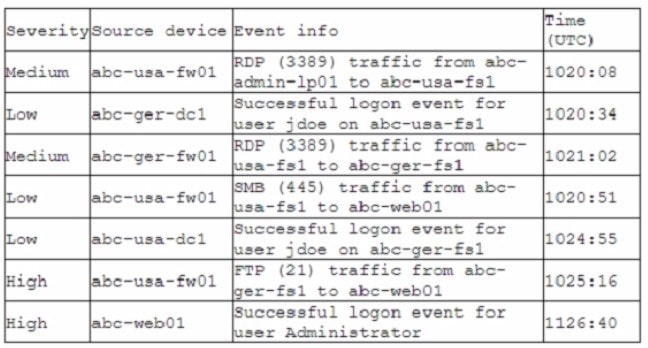
Which of the following should the security analyst do FIRST?
A. Disable Administrator on abc-uaa-fsl, the local account is compromised
B. Shut down the abc-usa-fsl server, a plaintext credential is being used
C. Disable the jdoe account, it is likely compromised
D. Shut down abc-usa-fw01; the remote access VPN vulnerability is exploited
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-1201
CompTIA A+ Certification: Core 1220-1202
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CAS-004 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.