Exam Details
Exam Code
:CV0-002Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:491 Q&AsLast Updated
:Mar 27, 2025
CompTIA CompTIA Certifications CV0-002 Questions & Answers
-
Question 111:
Based on demand, an IaaS provider wants to deploy a security application for its customers. Which of the following is the BEST technique for the IaaS provider to apply this to target systems?
A. Vendor application
B. Scripting
C. Orchestration
D. Custom programming
-
Question 112:
Upon discovery several SaaS applications are being utilized by users, and the InfoSec team needs to update a configuration file on all client machines. Which of the following file types is used to redirect users through a web proxy?
A. .dat
B. .tmp
C. .log
D. .pac
-
Question 113:
A new version of an e-commerce application was deployed using a standard template configuration of 4 vCPU and 8GB of RAM. The administrator has configured the application to automatically add 4 GB of RAM after 80% utilization of continuous use over a period of time.
Which of the following testing techniques should be used to test this scenario?
A. Integration testing
B. Load testing
C. Penetration testing
D. Automation testing
-
Question 114:
A cloud-based web proxy is blocking key sites that a business requires for operation. After validation, the sites are legitimate, and access is required for end users to complete their work. Which of the following is the BEST solution to allow access to the sites?
A. Instruct users to bypass the cloud-based web proxy.
B. Whitelist the URLs.
C. Blacklist the URLs.
D. Create a security group for those users and enforce MFA.
-
Question 115:
A SaaS customer reports that no one can access the application portal. After some troubleshooting, the cloud administrator finds a problem and provides a remedy by restarting the cluster. After documenting the solution, the support case is closed. Multiple tenants lose access to their hosts the following day.
Which of the following troubleshooting steps did the administrator miss?
A. Identify the problem.
B. Establish a theory.
C. Verify full system functionality.
D. Test the theory.
E. Establish a plan of action.
-
Question 116:
Ann, a cloud administrator, is reporting on how the organization has adhered to its marketing of 99.99999% system availability SLA. Given this scenario, which of the following should Ann include in her report?
A. System clock time
B. System idle percentage
C. System response time
D. System uptime
-
Question 117:
The sales department is preparing to launch a high-demand product for purchase through the company's online store. The senior engineer asks the junior engineer to review the sales cloud resources to plan for a surge in online traffic:
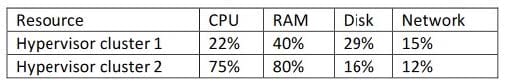
Given the metrics in the table above, which of the following resources should be adjusted to plan for future growth?
A. Propose additional memory for cluster 1.
B. Propose additional storage for cluster 1.
C. Propose additional guests for cluster 2.
D. Propose additional hosts for cluster 2.
-
Question 118:
To enhance availability, a company has expanded its public cloud presence to multiple regions from a single CSP. The company wants to ensure resources in the public cloud are highly available to users at company headquarters.
Which of the following is the BEST solution to fulfill this requirement?
A. Dual direct peering/connections from headquarters to one cloud region.
B. Dual VPN connections over a single ISP from headquarters to one cloud region.
C. Dual VPN connections over two separate ISPs from headquarters to both cloud regions.
D. Dual direct peering/connections over a single ISP from headquarters to both cloud regions
-
Question 119:
Given the metric below:
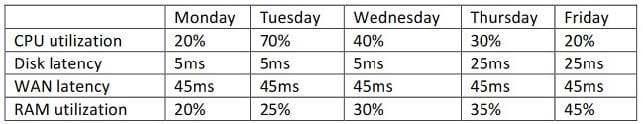
Using iSCSI storage reports across three datacenters, which of the following recorded metrics indicates an anomaly in the performance?
A. Disk latency
B. CPU utilization
C. WAN latency
D. RAM utilization
-
Question 120:
A cloud application development team needs to consider the following requirements to the built in as part of the application's authentication process:
-
Customers should have the flexibility to use their own identity stores within the authentication process.
-
Customers should not be asked to provide the credentials repeatedly for different applications with different permission sets.
Which of the following solutions would BEST help the team achieve the above business objectives? (Choose two.)
A. Certificates
B. Single sign-on
C. One-time passwords
D. Federation
E. Multifactor authentication
F. Hardware tokens
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-002 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.