Exam Details
Exam Code
:CV0-004Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:285 Q&AsLast Updated
:Mar 24, 2025
CompTIA CompTIA Certifications CV0-004 Questions & Answers
-
Question 91:
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
A. Security flaws need to be patched.
B. Updates could affect the current state of the VMs.
C. The cloud provider will be performing maintenance of the infrastructure.
D. The equipment is reaching end of life and end of support.
-
Question 92:
Which of the following communication methods between on-premises and cloud environments would ensure minimal-to-low latency and overhead?
A. Site-to-site VPN
B. Peer-to-peer VPN
C. Direct connection
D. peering
-
Question 93:
A company recently migrated to a public cloud provider. The company's computer incident response team needs to configure native cloud services tor detailed logging.
Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
A. Log retention
B. Tracing
C. Log aggregation
D. Log rotation
E. Hashing
F. Encryption
-
Question 94:
Which of the following vulnerability management concepts is best defined as the process of discovering vulnerabilities?
A. Scanning
B. Assessment
C. Remediation
D. Identification
-
Question 95:
A cloud engineer wants to replace the current on-premises. unstructured data storage with a solution in the cloud. The new solution needs to be cost-effective and highly scalable. Which of the following types of storage would be best to use?
A. File
B. Block
C. Object
D. SAN
-
Question 96:
Which of the following is true of SSDs?
A. SSDs do not have self-encrypting capabilities.
B. SSDs have small storage capacities.
C. SSDs can be used for high-IOP applications.
D. SSDs are used mostly in cold storage.
-
Question 97:
A cloud engineer is reviewing the following Dockerfile to deploy a Python web application:
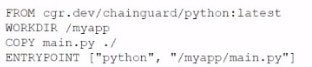
Which of the following changes should the engineer make lo the file to improve container security?
A. Add the instruction "JSER nonroot.
B. Change the version from latest to 3.11.
C. Remove the EHTRYPOIKT instruction.
D. Ensure myapp/main.pyls owned by root.
-
Question 98:
A cloud engineer is designing a cloud-native, three-tier application. The engineer must adhere to the following security best practices:
1.
Minimal services should run on all layers of the stack.
2.
The solution should be vendor agnostic.
3.
Virealization could be used over physical hardware.
Which of the following concepts should the engineer use to design the system to best meet these requirements?
A. Virtual machine
B. Micro services
C. Fan-out
D. Cloud-provided managed services
-
Question 99:
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application.
Which of the following is the best configuration approach to resolve this issue?
A. Scale vertically based on a trend.
B. Scale horizontally based on a schedule
C. Scale vertically based on a load.
D. Scale horizontally based on an event
-
Question 100:
A cloud administrator is building a company-standard VM image, which will be based on a public image. Which of the following should the administrator implement to secure the image?
A. ACLs
B. Least privilege
C. Hardening
D. Vulnerability scanning
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-004 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.