Exam Details
Exam Code
:CV0-004Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:285 Q&AsLast Updated
:Apr 01, 2025
CompTIA CompTIA Certifications CV0-004 Questions & Answers
-
Question 171:
A user's assigned cloud credentials are locked, and the user is unable to access the project's application. The cloud administrator reviews the logs and notices several attempts to log in with the user's account were made to a different application after working hours.
Which of the following is the best approach for the administrator to troubleshoot this issue?
A. Create new credentials for the user and restrict access to the authorized application.
B. Track the source of the log-in attempts and block the IP address of the source in the WAR
C. Reset the user's account and implement a stronger lock-out policy.
D. Install an IDS on the network to monitor suspicious activity
-
Question 172:
Which of the following storage resources provides higher availability and speed for currently used files?
A. Warm/HDD
B. Cold/SSD
C. Hot/SSD
D. Archive/HDD
-
Question 173:
A systems engineer is migrating a batch of 25 VMs from an on-premises compute cluster to a public cloud using the public cloud's migration agent. The migration job shows data copies at a rate of 250Mbps. After five servers migrate, the data copies at a rate of 25Mbps.
Which of the following should the engineer review first to troubleshoot?
A. The on-premises VM host hardware utilization
B. The on-premises ISP throttling rate
C. The IOPS on the SAN backing the on-premises cluster
D. The compute utilization of the VMs being migrated
-
Question 174:
Which of the following is a direct effect of cloud migration on an enterprise?
A. The enterprise must reorganize the reporting structure.
B. Compatibility issues must be addressed on premises after migration.
C. Cloud solutions will require less resources than on-premises installations.
D. Utility costs will be reduced on premises.
-
Question 175:
An organization's security policy states that software applications should not exchange sensitive data in cleartext. The security analyst is concerned about a software application that uses Base64 to encode credit card data.
Which of the following would be the best algorithm to replace Base64?
A. 3DES
B. AES
C. RC4
D. SHA-3
-
Question 176:
A developer is building an application that has multiple microservices that need to communicate with each other. The developer currently manually updates the IP address of each service.
Which of the following best resolves the communication issue and automates the process?
A. Service discovery
B. Fan-out
C. Managed container services
D. DNS
-
Question 177:
A developer at a small startup company deployed some code for a new feature to its public repository. A few days later, a data breach occurred. A security team investigated the incident and found that the database was hacked.
Which of the following is the most likely cause of this breach?
A. Database core dump
B. Hard-coded credentials
C. Compromised deployment agent
D. Unpatched web servers
-
Question 178:
A cloud engineer was deploying the company's payment processing application, but it failed with the following error log:
ERFOR:root: Transaction failed http 429 response, please try again
Which of the following are the most likely causes for this error? (Select two).
A. API throttling
B. API gateway outage
C. Web server outage
D. Oversubscription
E. Unauthorized access
F. Insufficient quota
-
Question 179:
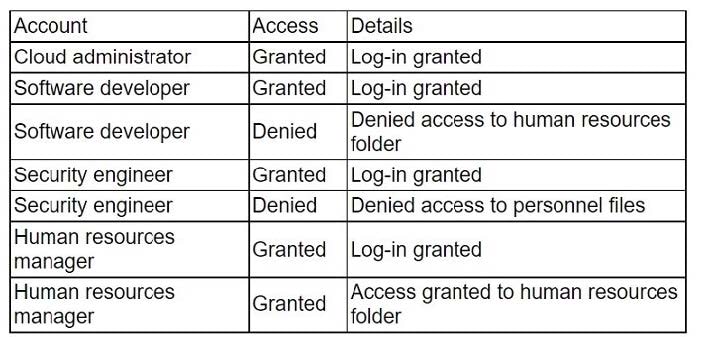
An administrator received a report that company data has been compromised. The compromise occurred on a holiday, and no one in the organization was working. While reviewing the logs from the holiday, the administrator noted the following details:
The most appropriate action for the cloud security analyst to recommend is using CIS- hardened images. These images are pre-configured by the Center for Internet Security to provide security benchmark standards that help in mitigating vulnerabilities in publicly available container images.
Which of the following accounts should the administrator disable to prevent a further breach?
A. Cloud administrator
B. Human resources manager
C. Security engineer
D. Software developer
-
Question 180:
A cloud administrator shortens the amount of time a backup runs. An executive in the company requires a guarantee that the backups can be restored with no data loss.
Which of th following backup features should the administrator lest for?
A. Encryption
B. Retention
C. Schedule
D. Integrity
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-004 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.