Exam Details
Exam Code
:HP0-Y51Exam Name
:Building HP SDN and FlexNetwork SolutionsCertification
:Master ASEVendor
:HPTotal Questions
:60 Q&AsLast Updated
:Mar 29, 2025
HP Master ASE HP0-Y51 Questions & Answers
-
Question 11:
A company has HP MultiService Mobility (MSM) APs that receive DHCP addresses on several different subnets. The APs are controlled by an MSM Controller. The company is considering replacing the MSM Controller with a Unified Wired-Wireless controller. The administrator runs a proof of concept test in which some of these APs are discovered and controlled by the Unified Wired-Wireless controller. Now the administrator wants to return the APs to being controlled by the MSM Controller.
The network administrator performs these actions:
Ensures that the Colubris vendor-specific option in each AP subnet DHCP scope references the MSM Controller IP address
Reboots the APs.
The MSM Controller never succeeds in discovering the APs. A debug reveals that the APs are not contacting the controller at all.
Which action could fix this problem?
A. Reset the APs to the factory default settings
B. In each AP DHCP scope, delete the Colubris vendor-specific option
C. Add a DNS host entry that maps hp example com to 10.1.10.20.
D. Upload MSM software to the HP Wired-Wireless controller flash.
-
Question 12:
A company has an HP Network Protector SDN Application with these characteristics:
The Network Protector whitelist for all user VLANs includes site1.example.com. The blacklist for all user VLANs includes site1.example.com with a time range
of
9:00 to 17:00.
The Rep DV database includes site1 example.com with a reputation score of 90.
An endpoint attempts to browse to site1.example.com. How does Network Protector classify DNS requests for site1.example.com?
A. It always flags the requests as threats.
B. It flags the requests as threats between 17:00 and 9:00.
C. It flags the requests as threats between 9:00 to 17:00.
D. It never flags the requests as threats.
-
Question 13:
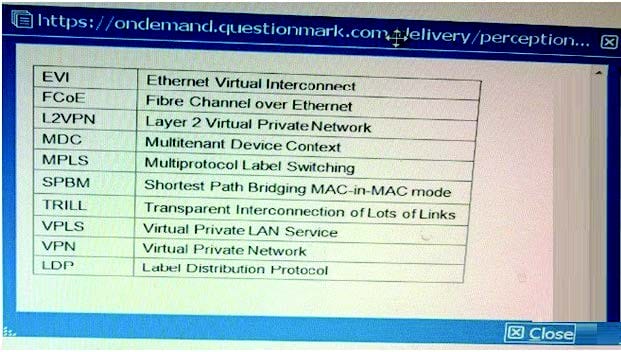
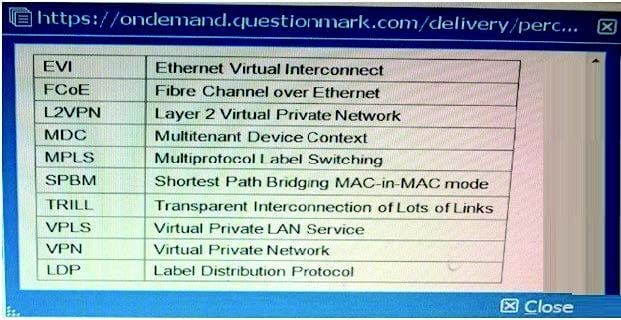
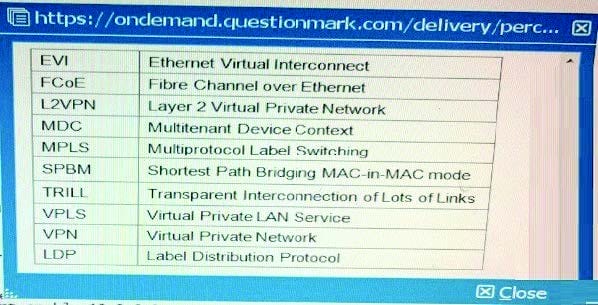
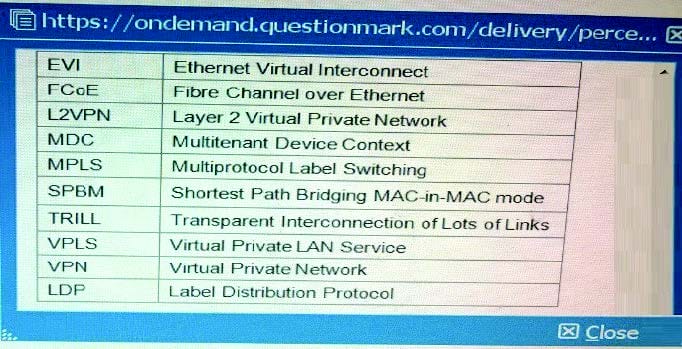
Table of Acronyms
Which common data center requirement does an HP EVI solution meet?
A. It enhances multi-data center solutions by extending Layer 2 connectivity across data centers connected at Layer 3.
B. It provides network administrators with more control over and visibility into communications between virtual machines (VMs).
C. It increases resilience and high availability within a data center transforming Layer 2 connections into a single fabric.
D. It enhances security for communications between data centers by automatically establishing encrypted tunnels between sites.
-
Question 14:
A company has an external SDN application that works with an HP VAN SDN Controller. The application programmer has tried testing several RESTful API calls but receives authentication errors. What does the administrator need to explain to the programmer?
A. Every RESTful API call must include an X-Auth token. The token can be obtained by sending a calf with valid credentials https.Controller_IP.8443/sdn/v2.0/ auth
B. Every RESTful API call must include a valid username and password. The only exception is when the AuthRequired parameter is set to false in restful conf file.
C. Every RESTful API call must include an X-Auth token. The token must be created by a valid certification authority (CA) and installed on both the controller and external application in advance.
D. The application must be installed with a certificate that is signed by the same certification authority (CA) that signed the VAN SDN Controller certificate.
-
Question 15:
Table of Acronyms
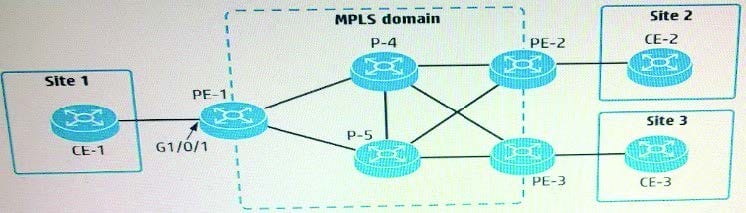
Refer to the exhibit.
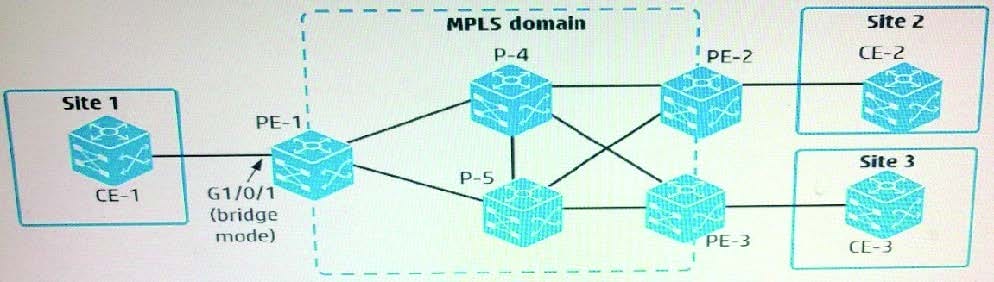
An administrator is configuring an MPLS and VPLS Martini to connect customer Sites 1, 2, and
3. The administrator has created Virtual Switch Instance (VSI) "CustomerA" for this purpose. How should the administrator connect customer Site 1 to the VPLS solution?
A. Create a service instance on the VLAN assigned to g1/0/1. Also create a global cross-connect group, and bind the CustomerA VSI and the service instance in that group.
B. Create a service instance on g1/0/1. Also create a global cross-connect group, and bind the CustomerA VSI and the service instance in that group.
C. Create a service instance on the VLAN assigned to g1/0/1. Bind (cross-connect) that instance to the CustomerA VSI.
D. Create a service instance on g1/0/1. Bind (cross-connect) that instance to the CustomerA VSI.
-
Question 16:
Table of Acronyms Refer to the exhibit.
An administrator wants to establish a remote LDP session between PE-1 (loopback IP address 10.0 0.1) and PE-2 (loopback IP address; 10.0.0.2). What is required to do this?
A. Both PE-1 and PE-2 have a VPN instance that is defined with the same route distinguisher (RD)
B. Both PE-1 and PE-2 advertise the same label for their loopback IP address
C. Both PE-1 and PE-2 use ordered mode for LDP.
D. Both PE-1 and PE-2 advertise their loopback IP address with OSPF and with LDP.
-
Question 17:
A company has an HP BYOD solution to let guests connect to a Guest SSID and log in through a registration page. The company needs an Employee SSID which enforces Wi-Fi Protected Access 2 (WPA2) with 802.1X. Employees must authenticate with certificates. Before authenticating with a device for the first time, the employees should be able to connect to the Guest SSID, access the guest registration page, and download valid certificates.
How does the administrator configure User Access Manager (UAM) to allow employees to download certificates from the registration page?
A. The User Endpoint Settings, create an Endpoint Configuration Distribution Policy that permits the employee groups.
B. In the Guest Manager settings for the employee manager, enable auto-registration in certificate mode.
C. In the Guest access policy, make sure that a policy binds the Employee SSID to an access rule with the onboarding VLAN ID.
D. In the Employee access service, make sure that a policy binds the Employee SSID to an access rule with the onboarding VLAN ID.
-
Question 18:
Table of Acronyms Refer to the exhibit.
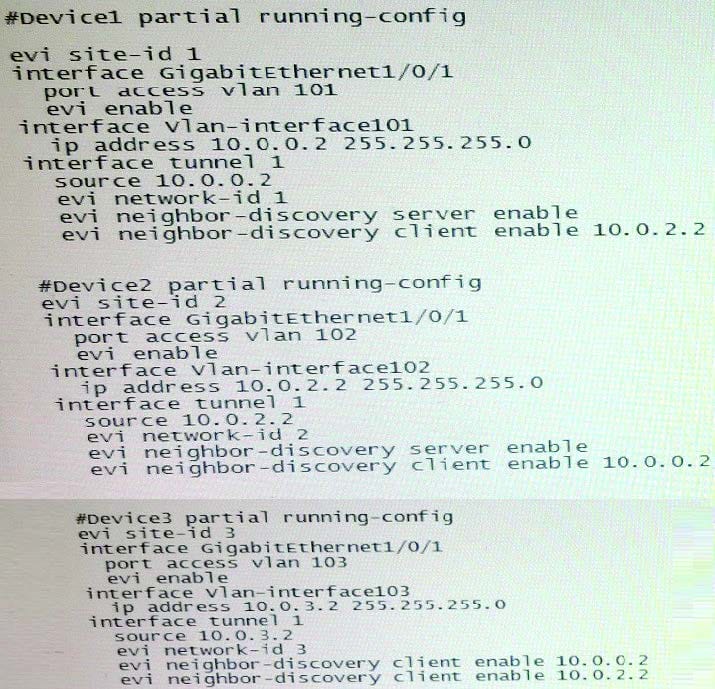
A company has three data centers, each with a connection to a service provider network. The administrator has configured the settings shown in the exhibit, but the EVI links are not coming up. What should the administrator do to correct the problem?
A. Change the EVI site ID on each device to match.
B. Add destination IP addresses to the tunnel interfaces.
C. Enable 1S-1S on the VLAN interfaces that connect to the service provider.
D. Change the EVI network ID on each device to match.
-
Question 19:
Table of Acronyms
An administrator is setting up an EVI solution on four HP Comware switches. The switches reach each other on these IP address:
Switch1 = 10.1.1.1
Switch2 = 10 2.2 2
Switch3 = 10.3.3.3
Switch4 = 10.4.4.4
The administrator wants to make Switch1 and Switch2 potential EVI Network Discovery Protocol (ENDP) servers. What is the proper configuration on the Switch1 EVI tunnel interface?
A. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.1.1.1
B. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.2.2.2
C. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
D. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
-
Question 20:
Which OpenFlow use case is an example of Network Functions Virtualization (NFV)?
A. Use OpenFlow to deploy configurations using IMC VAN SDN Manager.
B. Use OpenFlow to implement a router on an open-vswitch.
C. Use OpenFlow to replace the need of an snmp-agent on the switch.
D. Use OpenFlow to implement traffic prioritization on the edge.
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HP0-Y51 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.