Exam Details
Exam Code
:HP0-Y51Exam Name
:Building HP SDN and FlexNetwork SolutionsCertification
:Master ASEVendor
:HPTotal Questions
:60 Q&AsLast Updated
:Mar 29, 2025
HP Master ASE HP0-Y51 Questions & Answers
-
Question 31:
Refer to the exhibit.
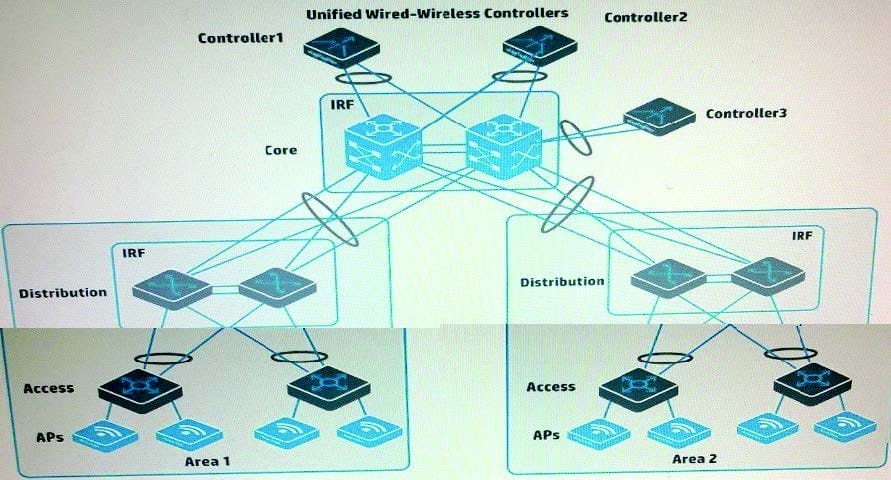
A company has two HP Unified Wired-Wireless controllers. The MSM APs in Area 1 in the exhibit are controlled by Controller1. The MSM APs in Area 2 in the exhibit are controlled by Controlled. The company purchases a Controlled to provide backup for both Controller1 and Controller2 (N+1 redundancy).
How does the administrator set up the APs in Area 1 so that they contact Controlled if Controller1 fails?
A. Create a roam group that includes Controller1, Controlled, and Controlled. Make sure that Controlled has the highest IP address
B. Create AP templates for the area 1 APs on Controlled and set its connection priority for these APs to 7.
C. Create a backup AC configuration group between Controller1 and Controlled. Enable Fast Backup on the group.
D. On Controller1, configure the new controller's IP address as the backup controller for the APs
-
Question 32:
A company has an HP BYOD solution with these requirements:
Employees can connect their own devices to an Employees SSID, which enforces Wi-Fi Protected Access 2 (WPA2) with 802.1X.
User Access Manager (UAM) is the RADIUS server for 802.1X authentication, and it enforces EAP-TLS.
The employees will first connect to an open SSID, access a portal page, and download the proper certificates for completing 802.1X authentication.
To meet these requirements, an administrator needs to deploy the correct certificate templates on UAM. What determine deploy?
A. Whether the company uses Active Directory (AD) or Open LDAP
B. Type of endpoint devices and the device operating systems (OS)
C. Government regulations with which the company must comply
D. Level of security that the company requires
-
Question 33:
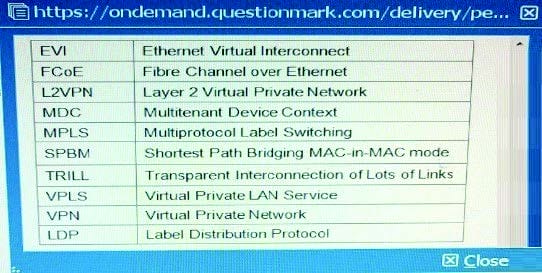
Table of Acronyms
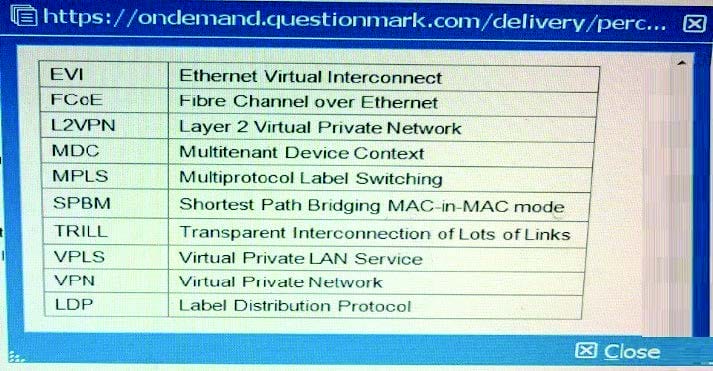
A company has a data center that hosts multiple tenants. The company is adding a second and third data center switch.
These are the IRF connections:
IRF 1 is the core of the first data center.
IRF 2 is the core of the second data center.
IRF 3 is the core of the third data center
The three data centers are fully interconnected with dark fiber. IRF 1, IRF 2, and IRF 3 have connections to a WAN and to the Internet.
Which option for the connections between the data centers provides the best resiliency and stability?
A. SPBM configured across IRF 1, IRF 2, and IRF 3
B. MSTP running on the links
C. IRF 1, IRF 2, and IRF 3 combined into a single IRF virtual device
D. A link aggregation that consists of all of the links
-
Question 34:
Table of Acronyms
A company is using Multi-CE (MCE) to create a multi-tenant data center solution. Administrators want to isolate all functions in a VPN instance "Management".
Each switch has an IP address in 10.0.2.0/24 on its Management Ethernet port, and HP IMC manages the switch on these IP addresses. Administrators assign
the Management Ethernet interfaces to the "Management" VPN instance. IMC begins losing data from the switches. How should administrators fix the problem on each switch?
A. Set VPN instance "Management" as the default VPN instance.
B. Specify VPN instance "Management" for settings such as the SNMP trap destination
C. Create a static route to 10.0.2.0/24 through next hop "vpn-instance Management".
D. Enable route leaking globally and on VPN instance "Management".
-
Question 35:
Table of Acronyms
Which HP IMC module helps companies to manage TRILL and SPBM solutions, as well as converged LAN/SAN solutions?
A. HP VAN Connection Manager
B. HP VAN SDN Manager
C. HP VAN Resource Manager
D. HP VAN Fabric Manager
-
Question 36:
Table of Acronyms
A company is deploying an HP VAN SDN Controller solution, which is installed with the HP Network Protector application. The administrator configures the solution to control HP Provision switches and must choose the OpenFlow instance failover mode. Which customer requirement should cause the administrator to choose standalone mode?
A. The solution must work with a single VAN SDN Controller rather than a team of controllers.
B. The company requires N+2 redundancy for the VAN SDN Controller functionality and the malware protection.
C. OpenFlow must be confined to the guest VLAN, which has the devices against which Network Protector guards the network
D. It is vital to protect user connectivity if the controller fails, even if the network is temporarily less protected against malware
-
Question 37:
A company is considering TRILL and SPBM as options for the data center architecture. The company is interested in how the solution handles load-balancing unicast traffic. What correctly describes the TRILL and SPBM options?
A. TRILL can use Equal Cost Multi-Path (ECMP). SPBM selects one best path to each SPBM switch in each B-VLAN, but can select different paths for different B-VLANs
B. SPBM can use Equal Cost Multi-Path (ECMP). TRILL does not support ECMP for unicasts, but can load-balance multicast, depending on the tree configuration.
C. Neither SPBM nor TRILL can use Equal Cost Multi-Path (ECMP). Both technologies can send traffic for different VLAN VLANs or I-SIDs on different links.
D. Both SPBM and TRILL can use Equal Cost Multi-Path (ECMP) to load-balance unicasts. provided that ECMP is enable at hardware level.
-
Question 38:
An administrator has set up an HP BYOD solution for an HP MSM760 controller and its APs.
These are the specifications:
Guests should only have to register and log in once After that, the guest device should be automatically logged in.
User Access Manager (UAM) provides the portal in which guests register their own accounts.
The MSM760 is connected to a Comware switch, which redirects unregistered guests to the UAM portal.
Currently guests can reach the portal, register for their accounts, and log in. However, guests report that they cannot reach the Internet after they log in. When the administrator asks the guests to disconnect from the wireless network and then connect again, they succeed in reaching the Internet.
What could fix this problem?
A. In the Comware switch settings, add the guest router to the free rule list
B. In the DHCP scope for the onboardmg VLAN, lower the lease time to about 10 seconds.
C. Configure SOAP settings for the MSM controller on UAM.
D. Configure the Comware switch to accept dynamic authorization updates from UAM.
-
Question 39:
A Company has APs that are deployed relatively close together. These APs are controlled by an HP Unified Wired-Wireless controller. Which setting helps to prevent the APs from interfering with each other while also letting the APs extend their coverage area if one of the AP fails?
A. Channel reuse
B. Dynamic frequency selection (DFS)
C. Transmit power control (TPC)
D. Fair scheduling
-
Question 40:
A company has an HP Unified Wired-Wireless controller that controls HP MultiService Mobility (MSM) APs. The network administrator wants to implement protection against rogue APs in the company's campus environment. Only APs that have approved MAC addresses should be allowed to operate and support clients. Controlled APs should send disassociation frames to prevent clients from connecting to rogue APs.
The administrator sets up APs to monitor the area and creates a permitted MAC address list with the approved AP MAC addresses. The administrator has not configured any other Intrusion Detection System (IDS) settings. Which additional step must the administrator complete?
A. Enable a dynamic blacklist.
B. Configure the permitted vendor and permitted SSID lists.
C. Enable countermeasures.
D. Deploy the permitted MAC address list as a static attack list to each controlled AP
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HP0-Y51 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.