Exam Details
Exam Code
:HPE2-W05Exam Name
:Implementing Aruba IntroSpectCertification
:HP CertificationsVendor
:HPTotal Questions
:115 Q&AsLast Updated
:Mar 28, 2025
HP HP Certifications HPE2-W05 Questions & Answers
-
Question 11:
An admin is evaluating entity activity alerts for large internal downloads, excessive host access, accessing hosts with SSH, and host and port scans. Is this a correct reason for these types of alerts? (a malware seeking command and control.)
A. Yes
B. No
-
Question 12:
An admin is evaluating entity activity alerts for large internal downloads, excessive host access, accessing hosts with SSH, and host and port scans. Is this a correct reason for these types of alerts? (an attacker conducting reconnaissance on the network.)
A. Yes
B. No
-
Question 13:
Your company has found some suspicious conversations for some internal users. The security team suspects those users are communicating with entities in other countries. You have been assigned the task of identifying those users who are either uploading or downloading files from servers in other countries. Is this the best way to visualize conversations of suspected users in this scenario? (Visualizing Applications and Ports.)
A. Yes
B. No
-
Question 14:
Refer to the exhibit.
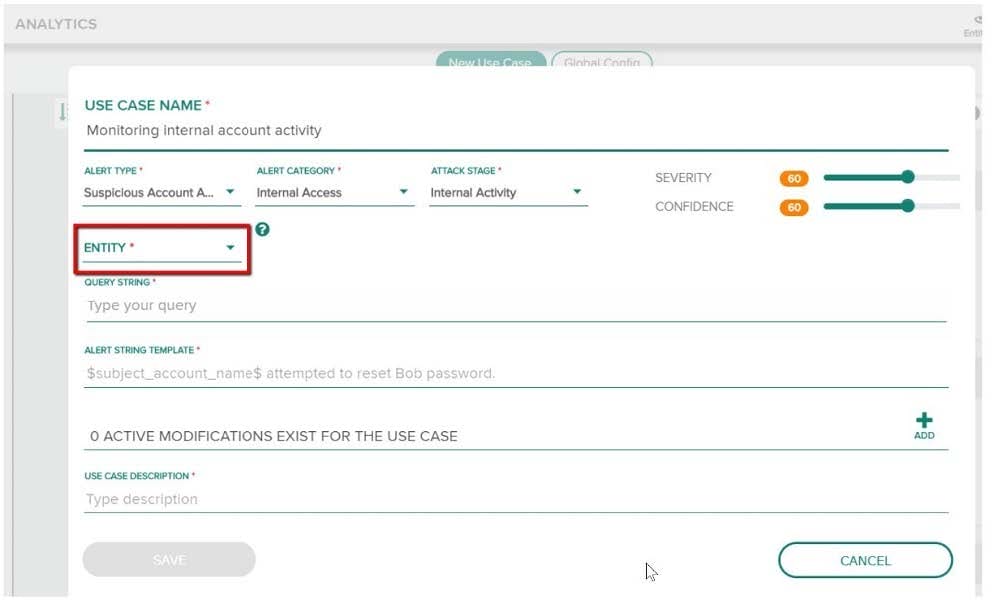
You have been assigned a task to monitor, analyze, and find those entities who are trying to access internal resources without having valid user credentials. You are creating an AD-based use case to look for this activity. Could you use this entity type to accomplish this? (Dest IP.)
A. Yes
B. No
-
Question 15:
Your company has found some suspicious conversations for some internal users. The security team suspects those users are communicating with entities in other countries. You have been assigned the task of identifying those users who are either uploading or downloading files from servers in other countries. Is this the best way to visualize conversations of suspected users in this scenario? (Visualizing conversation graphs.)
A. Yes
B. No
-
Question 16:
Refer to the exhibit.
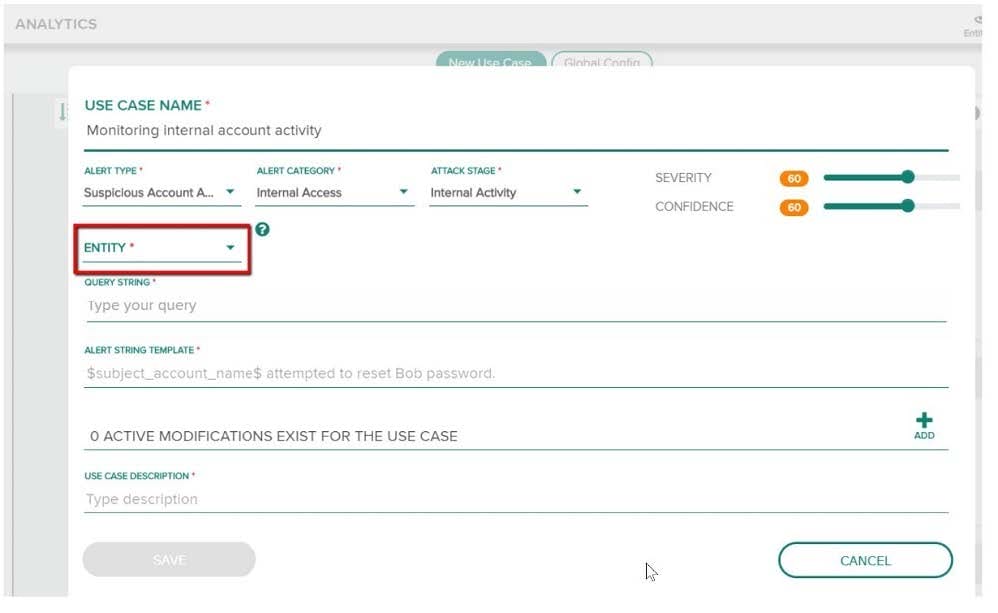
You have been assigned a task to monitor, analyze, and find those entities who are trying to access internal resources without having valid user credentials. You are creating an AD-based use case to look for this activity. Could you use this entity type to accomplish this? (Dest Host.)
A. Yes
B. No
-
Question 17:
Refer to the exhibit.
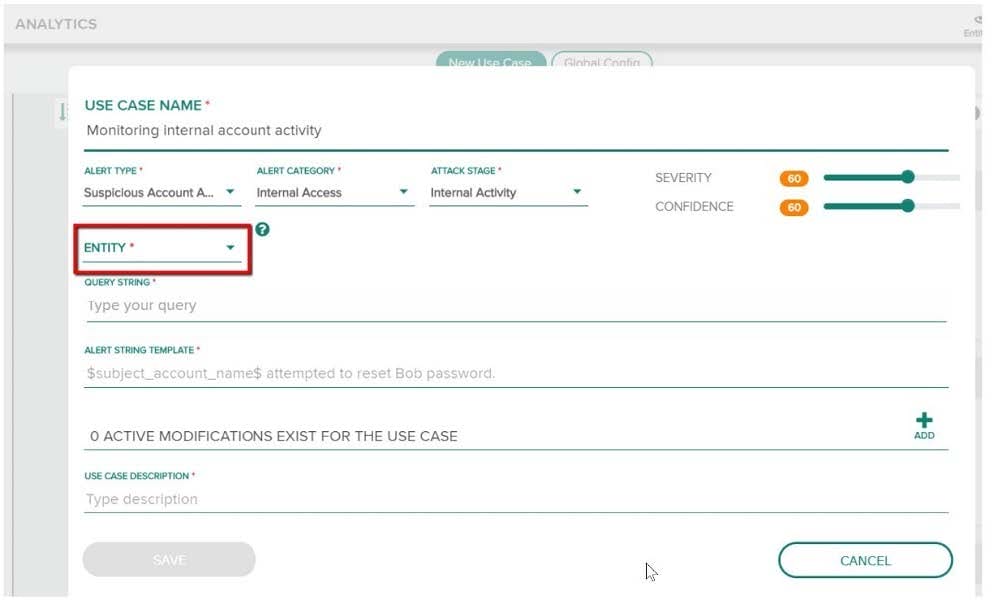
You have been assigned a task to monitor, analyze, and find those entities who are trying to access internal resources without having valid user credentials. You are creating an AD-based use case to look for this activity. Could you use this entity type to accomplish this? (Source Host.)
A. Yes
B. No
-
Question 18:
Refer to the exhibit.
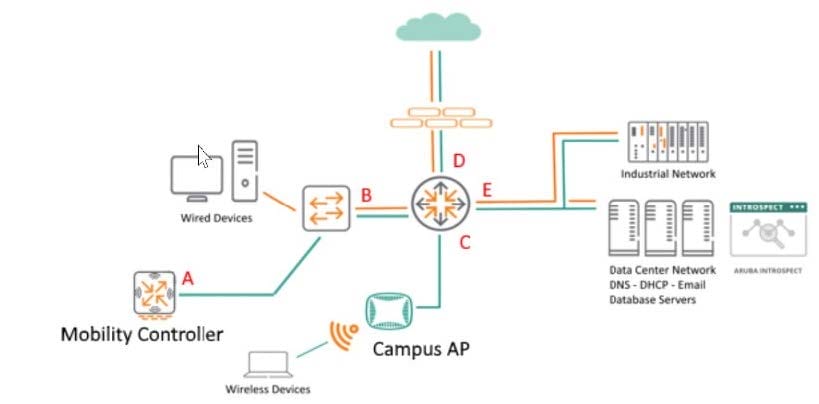
You are monitoring network traffic and considering DNS flow patterns. Where is a good location to place the Network Tap or Taps? (Location A.)
A. Yes
B. No
-
Question 19:
Refer to the exhibit.
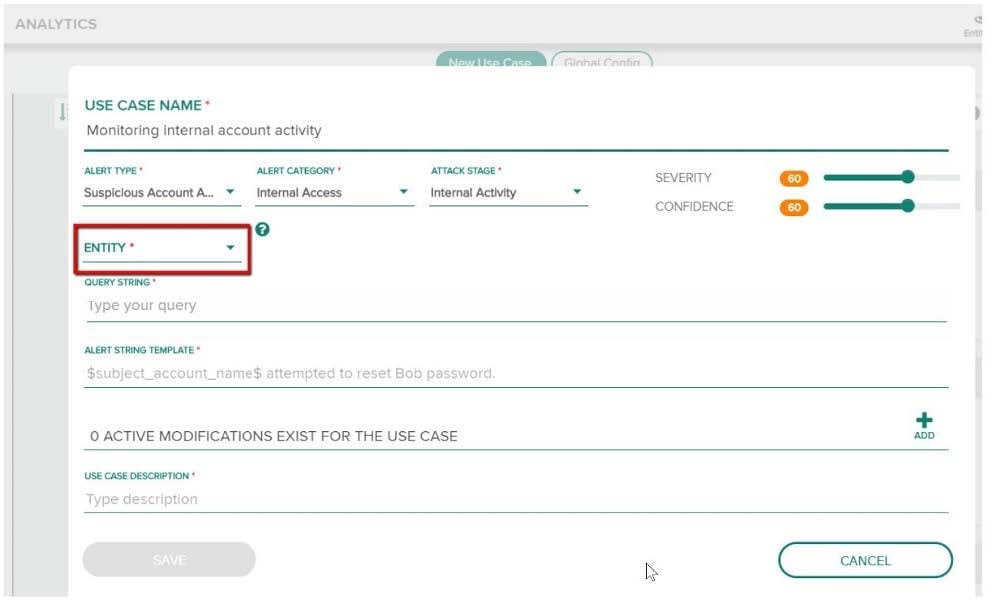
You have been assigned a task to monitor, analyze, and find those entities who are trying to access internal resources without having valid user credentials. You are creating an AD-based use case to look for this activity. Could you use this entity type to accomplish this? (Host name.)
A. Yes
B. No
-
Question 20:
Refer to the exhibit.
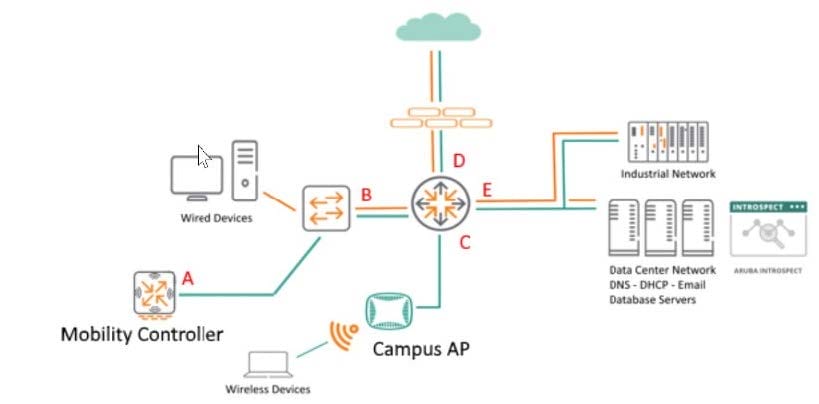
You are monitoring network traffic and considering DNS flow patterns. Where is a good location to place the Network Tap or Taps? (Location B will capture wired clients DNS requests while Location A will capture wireless client DNS.)
A. Yes
B. No
Related Exams:
HP0-D15
Administering HP CloudSystem Matrix SolutionsHP0-D20
Architecting the HP Matrix Operating EnvironmentHP2-E56
Selling HP SMB SolutionsHP2-H88
Selling HP Business Personal Systems Hardware 2019HP2-I14
Selling HP Supplies 2020HP2-I15
Selling HP Business Personal Systems Hardware 2020HP2-I17
Selling HP Printing Hardware 2020HP2-I44
Selling HP Workstations 2022HP2-I73
Selling HP Retail and Hospitality Solutions 2024HP2-N51
HP Application Lifecycle Management 12.x Software
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HPE2-W05 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.