Exam Details
Exam Code
:HPE2-W05Exam Name
:Implementing Aruba IntroSpectCertification
:HP CertificationsVendor
:HPTotal Questions
:115 Q&AsLast Updated
:Mar 28, 2025
HP HP Certifications HPE2-W05 Questions & Answers
-
Question 31:
A security analyst is monitoring the traffic which is accessing internal and external resources. They find abnormal activity, indicating communication between a compromised internal user(host) and internal infrastructure, and found a suspicious malware activity. Is this a correct attack stage classification for this activity? (Exfiltration.)
A. Yes
B. No
-
Question 32:
While looking at the conversations page you notice one user account logging into a number of servers on a regular basis. Is this information that you can draw from this activity? (This could be a service account and should be excluded from correlating Logon events with devices, or every device it logs into will be credited to it as the owner.)
A. Yes
B. No
-
Question 33:
Refer to the exhibit.
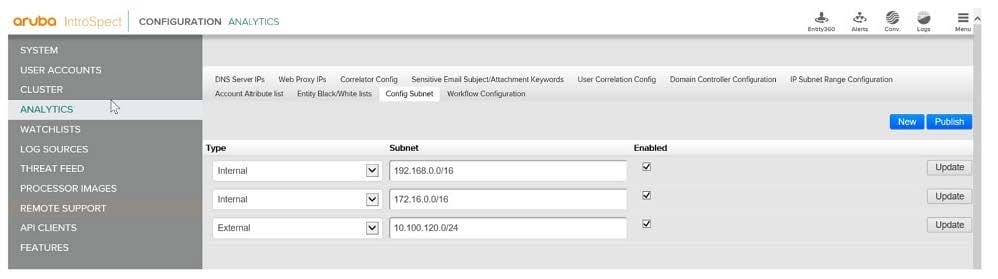
You are working with an IntroSpect Analyzer which is configured to monitor your network. You have navigated to the andldquo;Config Subnetsandrdquo; page to verify whether the internal and external subnets are configured properly. Is this a correct assessment of the screen? (The 10.100.120 subnet is incorrectly listed as external.)
A. Yes
B. No
-
Question 34:
An alert goes off for the internal DNS server, and while investigating the logs you notice that the hostnames in the queries are random alphanumeric characters. Is this a logical investigation step? (Contact the DNS admin and request that they enable root hints in the DNS server.)
A. Yes
B. No
-
Question 35:
While investigating alerts in the Analyzer you notice a host desktop with a low risk score has been sending regular emails from an internal account to the same external account. Upon investigation you see that the emails all have attachments. Would this be correct assessment of the situation? (Your next step should be to find what user account logs into this desktop, and look at activity of their devices this user has access to.)
A. Yes
B. No
-
Question 36:
Refer to the exhibit.
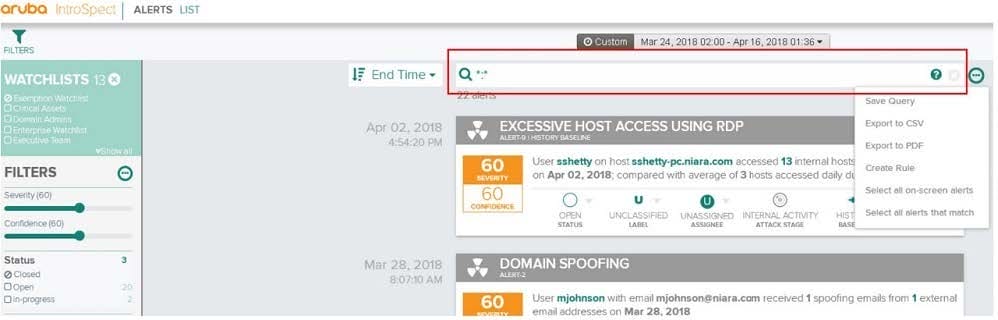
You are logged into the IntroSpect and have navigated to the Alerts list. You are trying to filter the alerts to show all malware alerts for users. Is this a correct search query? (alertcategory:malware* AND username:any)
A. Yes
B. No
-
Question 37:
While investigating alerts in the Analyzer you notice a host desktop with a low risk score has been sending regular emails from an internal account to the same external account. Upon investigation you see that the emails all have attachments. Would this be correct assessment of the situation? (This desktop should be added to a watch list and audited for a time to determine if this is real threat activity.)
A. Yes
B. No
-
Question 38:
While investigating alerts in the Analyzer you notice a host desktop with a low risk score has been sending regular emails from an internal account to the same external account. Upon investigation you see that the emails all have attachments. Would this be correct assessment of the situation? (The user on this host spends way too much time sending email, but should not be considered a risk until the risk score climbs above 60.)
A. Yes
B. No
-
Question 39:
Refer to the exhibit.
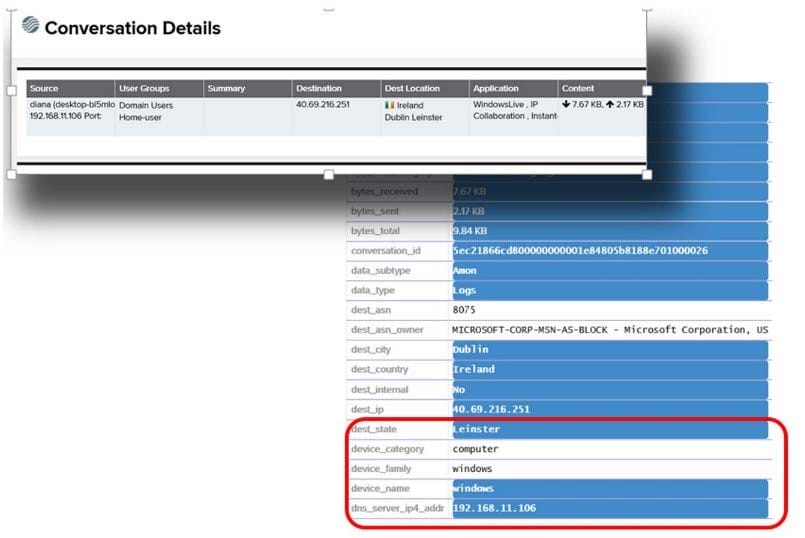
You are a security analyst for a company that has deployed an Aruba infrastructure, such as Mobility Controllers, ClearPass, and Airwave. Recently they have deployed Aruba IntroSpect for security analytics. You are looking at the conversation details of an entity. Is this statement correct about the details highlighted? (These details came from the ClearPass server and it has been integrated as a context server in the IntroSpect.)
A. Yes
B. No
-
Question 40:
You are looking in the conversation page on the IntroSpect Analyzer. Is this a valid method for determining which source the conversation data come from? (Click on the different options under Applications to filter for application types like DNS and HTTP.)
A. Yes
B. No
Related Exams:
HP0-D15
Administering HP CloudSystem Matrix SolutionsHP0-D20
Architecting the HP Matrix Operating EnvironmentHP2-E56
Selling HP SMB SolutionsHP2-H88
Selling HP Business Personal Systems Hardware 2019HP2-I14
Selling HP Supplies 2020HP2-I15
Selling HP Business Personal Systems Hardware 2020HP2-I17
Selling HP Printing Hardware 2020HP2-I44
Selling HP Workstations 2022HP2-I73
Selling HP Retail and Hospitality Solutions 2024HP2-N51
HP Application Lifecycle Management 12.x Software
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HPE2-W05 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.