Exam Details
Exam Code
:HPE2-W05Exam Name
:Implementing Aruba IntroSpectCertification
:HP CertificationsVendor
:HPTotal Questions
:115 Q&AsLast Updated
:Mar 28, 2025
HP HP Certifications HPE2-W05 Questions & Answers
-
Question 71:
During a discovery at a large company, the customer asks if they can run IntroSpect on a segment of the network and only monitor a small group of users and servers as a trial. As their IT staff becomes familiar with the analytics, they want to expand the installation to the entire enterprise. Would this be a valid option for the customer? (The customer can deploy the analyzer at the first site and use whitelist/blacklist functions to contain the scope of the analytics to the smaller site.)
A. Yes
B. No
-
Question 72:
During a discovery at a large company, the customer asks if they can run IntroSpect on a segment of the network and only monitor a small group of users and servers as a trial. As their IT staff becomes familiar with the analytics, they want to expand the installation to the entire enterprise. Would this be a valid option for the customer? (It is easy to support growth with the Scale-out Analyzer appliance, as Analyzer Nodes may be added over time to support the larger demand from the full environment.)
A. Yes
B. No
-
Question 73:
Refer to the exhibit.
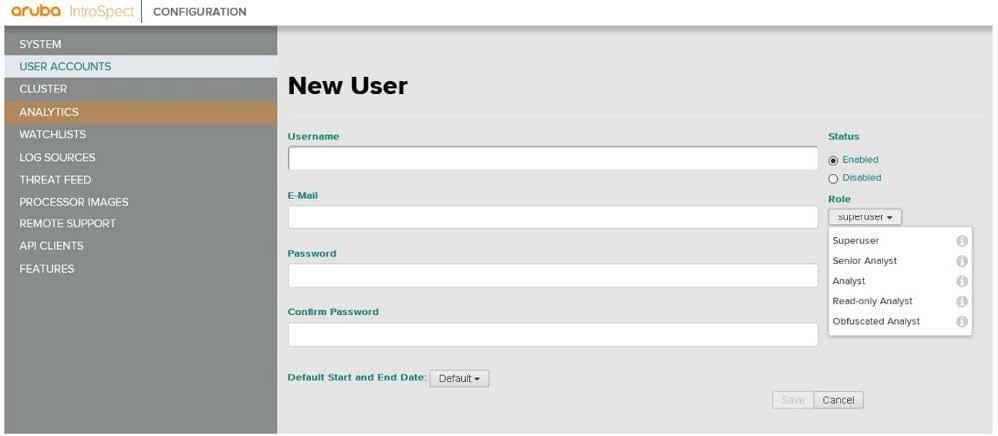
Would this be a correct option when configuring a user account for a ClearPass to use to communicate with IntroSpect? (The email address needs to match the username used in ClearPass.)
A. Yes
B. No
-
Question 74:
Refer to the exhibit.
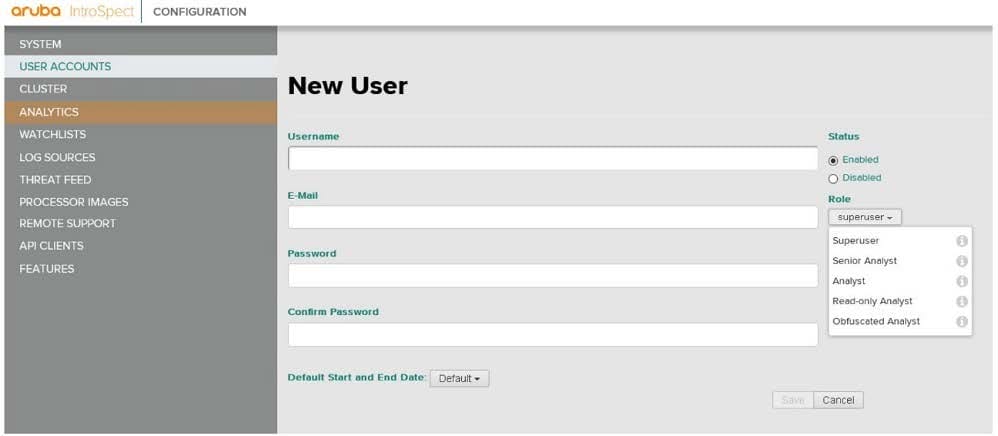
Would this be a correct option when configuring a user account for a ClearPass to use to communicate with IntroSpect? (The username must be the host name of the ClearPass server, and the email address needs to be the username on the ClearPass server.)
A. Yes
B. No
-
Question 75:
Refer to the exhibit.
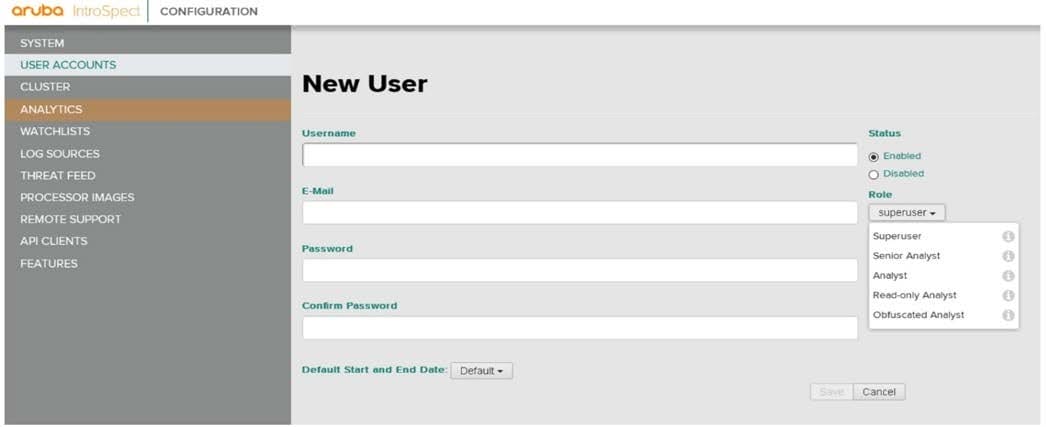
Would this be a correct option when configuring a user account for a ClearPass to use to communicate with IntroSpect? (The username and email address must match.)
A. Yes
B. No
-
Question 76:
While reviving the logs at a customer site you notice that one particular device is accessing multiple
servers in the environment, using a number of different user accounts. When you question the IT admin,
they tell you that the computer is a JumpBox and running software used to monitor all of the servers in the
environment.
Would this be a logical next step? (As a next step, you should audit all of the accounts that are being used
on the JumpBox to determine if the JumpBox is being accessed by unauthorized accounts.)
A. Yes
B. No
-
Question 77:
While reviving the logs at a customer site you notice that one particular device is accessing multiple
servers in the environment, using a number of different user accounts. When you question the IT admin,
they tell you that the computer is a JumpBox and running software used to monitor all of the servers in the
environment.
Would this be a logical next step? (You can safely ignore this activity as this is normal behavior for a
JumpBox.)
A. Yes
B. No
-
Question 78:
A company wants to integrate ClearPass with the IntroSpect. Is this a supported version? (ClearPass 6.7.4.)
A. Yes
B. No
-
Question 79:
A company wants to integrate ClearPass with the IntroSpect. Is this a supported version? (ClearPass 6.7.3.)
A. Yes
B. No
-
Question 80:
While discussing network security with an associate, the associate asks why a company would need internal monitoring when they have firewalls and Wireless Intrusion Protection configured. Is this an appropriate response? (You point out that while these security measures are required, there are other attack vectors in a network that are simply not protected by these.)
A. Yes
B. No
Related Exams:
HP0-D15
Administering HP CloudSystem Matrix SolutionsHP0-D20
Architecting the HP Matrix Operating EnvironmentHP2-E56
Selling HP SMB SolutionsHP2-H88
Selling HP Business Personal Systems Hardware 2019HP2-I14
Selling HP Supplies 2020HP2-I15
Selling HP Business Personal Systems Hardware 2020HP2-I17
Selling HP Printing Hardware 2020HP2-I44
Selling HP Workstations 2022HP2-I73
Selling HP Retail and Hospitality Solutions 2024HP2-N51
HP Application Lifecycle Management 12.x Software
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only HP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your HPE2-W05 exam preparations and HP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.