Exam Details
Exam Code
:MD-100Exam Name
:Windows ClientCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:409 Q&AsLast Updated
:Mar 30, 2025
Microsoft Microsoft Certifications MD-100 Questions & Answers
-
Question 281:
You have a computer named Computer1 that runs Windows10. Computer1 is in a workgroup. Computer1 contains the users shown in the following table.
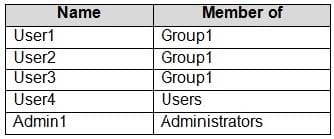
You need to apply the same Group Policy settings to only User1, User2 and User3. The solution must use a minimum number of local Group Policy objects (GPOs). How many local GPOs should you create?
A. 1
B. 2
C. 3
-
Question 282:
You have a workgroup computer named Computer1 that runs Windows 10. Computer1 contains five local user accounts. You need to ensure that all users who sign in to Computer1 see a picture named Image1.jpg as the desktop background. What should you do?
A. From the Settings app. modify the Background settings.
B. From the Local Group Policy Editor, modify the Desktop settings.
C. Rename Image1.jpg as Desktop.jpg and copy the picture to the C:\Windows\system32\folder.
D. Rename Image1.jpg as Desktop.jpg and copy the picture to the C:\Users\Default\Desktopfolder.
-
Question 283:
Your company has several mobile devices that run Windows 10.
You need configure the mobile devices to meet the following requirements:
1.
Windows updates may only be download when mobile devices are connect to Wi-Fi.
2.
Access to email and the Internet must be possible at all times. What should you do?
A. Open the Setting app and select Update and Security. Then select and configure Change active hours.
B. Open the Setting app and select Network and Internet. Then select Change connection properties, and set the Metered connection option for cellular network connections to On.
C. Open the Setting app and select Network and Internet Then select Data Usage and set a data limit.
D. Open the Setting app and select Update and Security. Then select and configure Delivery Optimization.
-
Question 284:
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected].
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission shown in the following table.
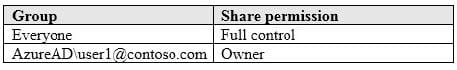
A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com by using [email protected].
User2 attempts to access Share1 and receives the following error message: "The username or password is incorrect."
You need to ensure that User2 can connect to Share1.
Solution: You create a local group on Computer1 and add the Guest account to the group.
You grant the group Modify access to Share1.
Does this meet the goal?
A. Yes
B. No
-
Question 285:
You have a computer named Computer1 that runs Windows 10. Computer1 contains a folder named Folder1.
You need to log any users who take ownership of the files in Folder1.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. Modify the folder attributes of Folder1.
B. Modify the Advanced Security Settings for Folder1.
C. From a Group Policy object (GPO), configure the Audit Sensitive Privilege Use setting.
D. From a Group Policy object (GPO), configure the Audit File System setting.
E. Install the Remote Server Administration Tools (RSAT).
-
Question 286:
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have a computer named Computer1 that runs Windows 10. The computer contains a folder.
The folder contains sensitive data.
You need to log which user reads the contents of the folder and modifies and deletes files in the folder.
Solution: From the properties of the folder, you configure the Auditing settings and from Audit Policy in the local Group Policy, you configure Audit object access.
Does this meet the goal?
A. Yes
B. No
-
Question 287:
Your network an Active Directory domain named adatum.com. The domain contains 50 computers that runs Windows 8.1. The computer has locally installed desktop application that are compatible with Windows 10.
You need to upgrade the computers to windows 10, The solution must preserver the locally installed desktop applications.
Solution. You use System image manager (Windows SIM) to create an answer file. You use Windows Deployment Service (WDS) to add an install image. You start each computer by using PXE, and then install the image.
Does this meet the goal?
A. Yes
B. No
-
Question 288:
Your network contains an Active Directory domain. The domain contains 1,000 computers that run Windows 10.
You configure Microsoft Edge settings by using domain and local Group Policy Objects (GPOs).
You need to generate a report that contains all the Microsoft Edge policy settings applied to a computer.
What should you do?
A. From PowerShell. run the Gec-GPO cmdlet.
B. From PowerShell. run the Gec-GPOReporc cmdlet.
C. From Microsoft Edge, open edge://policy.
D. From Microsoft Edge, open edge://settings.
-
Question 289:
Your network contains an Active Directory domain. The domain contains 1,000 computers that run Windows 10.
You discover that when users are on their lock screen, they see a different background image every day, along with tips for using different features in Windows 10.
You need to disable the tips and the daily background image for all the Windows 10 computers.
Which Group Policy settings should you modify?
A. Turn off the Windows Welcome Experience
B. Turn off Windows Spotlight on Settings
C. Do not suggest third-party content in Windows spotlight
D. Turn off all Windows spotlight features
-
Question 290:
You have 20 computers that run Windows 10.
You configure all the computers to forward all the events from all the logs to a computer named Computer1 that runs Windows 10.
When you sign in to Computer1, you cannot see any security events from other computers. You can see all the other forwarded events from the other computers.
You need to ensure that the security events are forwarded to Computer1.
What should you do?
A. On each computer, run wecutil ac /q.
B. On each computer, add the NETWORK SERVICE account to the Event Log Readers group.
C. On each computer, run winrm qc -q.
D. On Computer1, add the account of Computer1 to the Event Log Readers group.
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your MD-100 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.