Exam Details
Exam Code
:MD-100Exam Name
:Windows ClientCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:409 Q&AsLast Updated
:Mar 30, 2025
Microsoft Microsoft Certifications MD-100 Questions & Answers
-
Question 311:
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a computer named Computer1 that runs Windows 10.
A service named Application1 is configured as shown in the exhibit.

You discover that a user used the Service1 account to sign in to Computer1 and deleted some files.
You need to ensure that the identity used by Application1 cannot be used by a user to sign in to sign in to the desktop on Computer1. The solution must use the principle of least privilege.
Solution: On Computer1, you assign Service1 the deny log on as a service user right.
Does this meet the goal?
A. Yes
B. No
-
Question 312:
You install Windows 10 Enterprise on a new computer.
You need to force activation on the computer.
Which command should you run?
A. slmgr /upk
B. Sec-RDLicenseConfiguration-Force
C. Sec-MsolLicense-AddLicense
D. slmgr /ato
-
Question 313:
Your network contains an Active Directory domain that is synced to a Microsoft Azure Active Directory (Azure AD) tenant.
Your company purchases a Microsoft 365 subscription.
You need to migrate the Documents folder of users to Microsoft OneDrive for Business.
What should you configure?
A. One Drive Group Policy settings
B. roaming user profiles
C. Enterprise State Roaming
D. Folder Redirection Group Policy settings
-
Question 314:
Your network contains an Active Directory domain. The domain contains the computers shown in the following table.
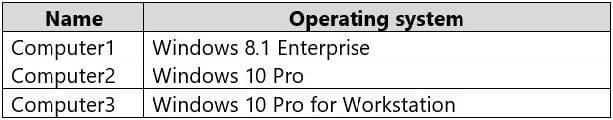
On which computers can you perform an in-place upgrade to Windows 10 Enterprise?
A. Computer3 only
B. Computed and Computer3 only
C. Computed only
D. Computed. Computed, and Computer3
-
Question 315:
You have a public computer named Computer1 that runs Windows 10/ Computer1 contains a folder named Folder1.
You need to provide a user named User1 with the ability to modify the permissions of Folder1. The solution must use the principle of least privilege.
Which NTFS permission should you assign to User1?
A. Full control
B. Modify
C. Write
D. Read and execute
-
Question 316:
Your network contains an Active Directory domain. The domain contains a computer named Computer1 that runs Windows 10. Computer1 contains a folder named Folder1.
You plan to share Folder1. Everyone will have Read share permissions, and administrators will have Full control share permission.
You need to prevent the share from appearing when users browse the network.
What should you do?
A. Enable access-based enumeration.
B. Deny the List NTFS permissions on Folded.
C. Add Folded to a domain-based DFS namespace.
D. Name the share Folded$.
-
Question 317:
You have a computer named Computer1 that runs Windows 10.
Computer1 was off for one year. During that time, two feature updates and 12 quality updates were released.
From the Microsoft Update Catalog website, you download the missing updates and save the updates to Computer1.
You need to ensure that Computer1 runs the latest version of Windows 10 and is fully updated. The solution must minimize the amount of time required to update the computer.
What should you do?
A. Install the last feature update, and then install the last quality update.
B. Install the last quality update, and then install both feature updates.
C. Install the last quality update, and then install the last feature update.
D. Install the last feature update, and then install all the quality updates released after the feature update.
E. Install all the quality and feature updates in the order in which they were released.
-
Question 318:
Your network contains an Active Directory domain. The domain contains computers that run Windows 10.
You must ensure that Windows BitLocker Drive Encryption is enabled on all client computers, even though a Trusted Platform Module (TPM) chip is installed in only some of them.
You need to accomplish this goal by using one Group Policy object (GPO).
What should you do?
A. Enable the Allow enhanced PINs for startup policy setting, and select the Allow BitLocker without a compatible TPM check box
B. Enable the Enable use of BitLocker authentication requiring preboot keyboard input on slates policy setting, and select the Allow BitLocker without a compatible TPM check box
C. Enable the Require additional authentication at startup policy setting, and select the Allow BitLocker without a compatible TPM check box
D. Enable the Control use of BitLocker on removable drives policy setting, and select the Allow BitLocker without a compatible TPM check box
-
Question 319:
You have a computer that runs Windows 10. You use the computer to test new Windows features. You need to configure the computer to receive preview builds of Windows 10 as soon as possible. What should you configure from Update and Security in the Settings app?
A. Windows Insider Program
B. Windows Update
C. Delivery Optimization
D. For developer
-
Question 320:
Your company has a computer named Computer1 that runs Windows 10. Computer1 is used to provide guests with access to the Internet. Computer1 is a member of a workgroup.
You want to configure Computer1 to use a user account sign in automatically when the computer is started. The user must not be prompted for a user name and password.
What should you do?
A. Configure Group Policy preferences.
B. Run the BCDBoot command.
C. Edit the Registry.
D. Run the MSConfig command.
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your MD-100 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.