Exam Details
Exam Code
:MD-102Exam Name
:Endpoint AdministratorCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:351 Q&AsLast Updated
:Mar 23, 2025
Microsoft Microsoft Certifications MD-102 Questions & Answers
-
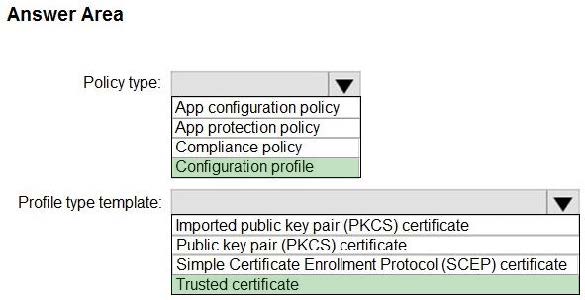
Question 221:
HOTSPOT
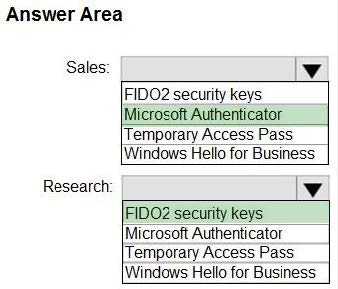
You have a Microsoft 365 tenant and an internal certification authority (CA).
You need to use Microsoft Intune to deploy the root CA certificate to managed devices.
Which type of Intune policy and profile type template should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
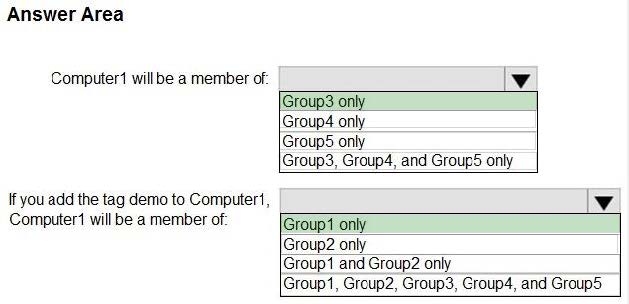
Question 222:
HOTSPOT
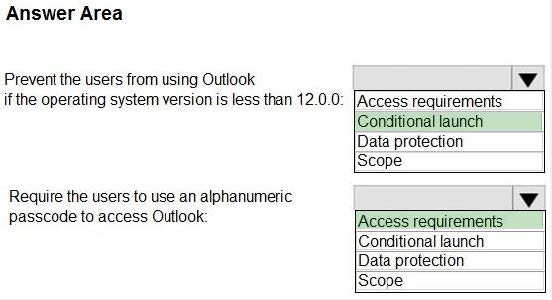
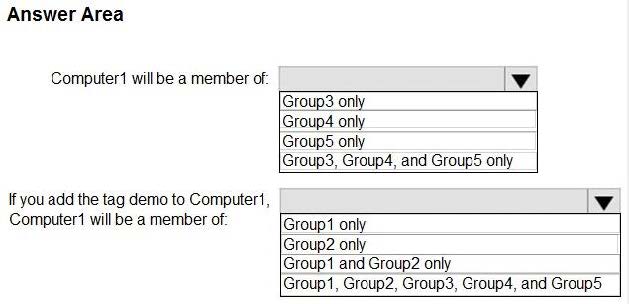
Your company uses Microsoft Defender for Endpoint. Microsoft Defender for Endpoint includes the device groups shown in the following table.
You onboard a computer to Microsoft Defender for Endpoint as shown in the following exhibit.

What is the effect of the Microsoft Defender for Endpoint configuration? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
-
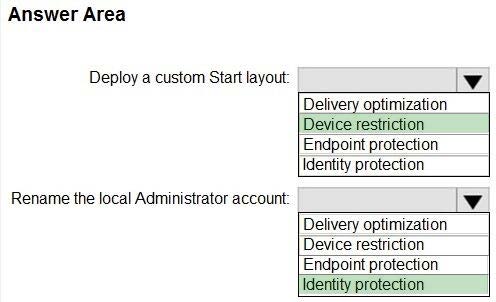
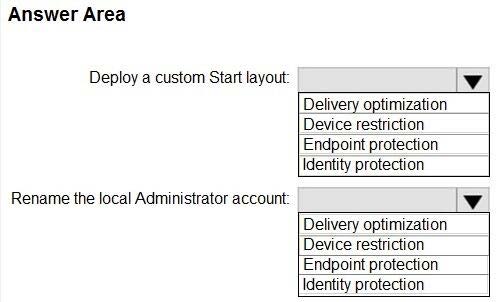
Question 223:
HOTSPOT
You have a Microsoft 365 subscription that uses Microsoft Intune and contains 100 Windows 10 devices.
You need to create Intune configuration profiles to perform the following actions on the devices:
1.
Deploy a custom Start layout.
2.
Rename the local Administrator account.
Which profile type template should you use for each action? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
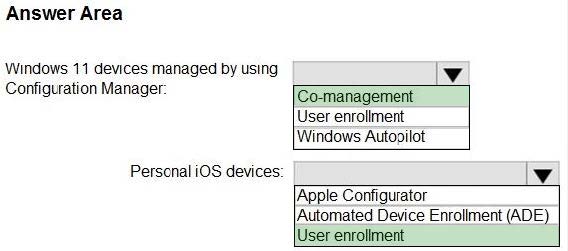
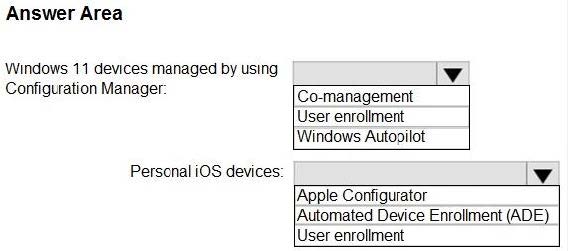
Question 224:
HOTSPOT
You have a Microsoft 365 subscription.
You plan to enable Microsoft Intune enrollment for the following types of devices:
1.
Existing Windows 11 devices managed by using Configuration Manager
2.
Personal iOS devices
The solution must minimize user disruption.
Which enrollment method should you use for each device type? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
Question 225:
HOTSPOT
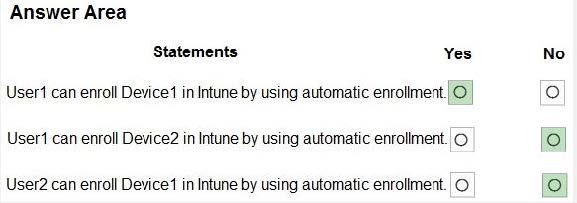
You have an Azure AD Premium P2 subscription that contains the users shown in the following table.
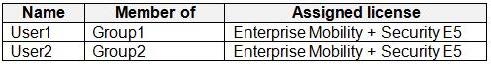
You purchase the devices shown in the following table.
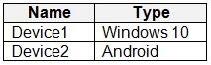
You configure automatic mobile device management (MDM) and mobile application management (MAM) enrollment by using the following settings:
1.
MDM user scope: Group1
2.
MAM user scope: Group2
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
-
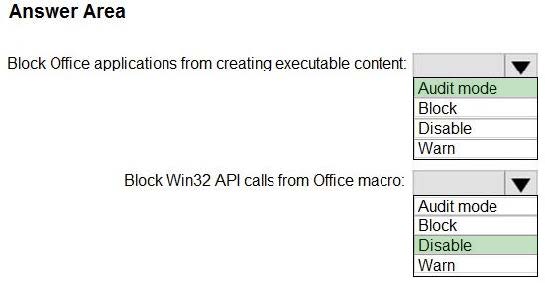
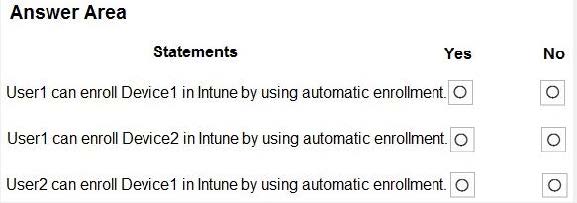
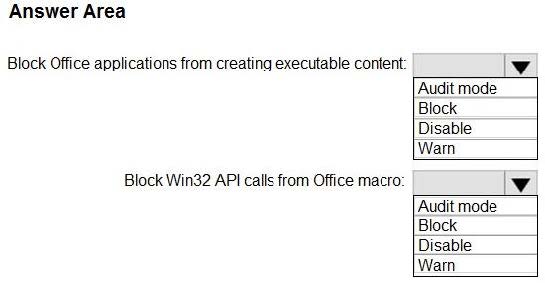
Question 226:
HOTSPOT
You have the MDM Security Baseline profile shown in the MDM exhibit. (Click the MDM tab.)
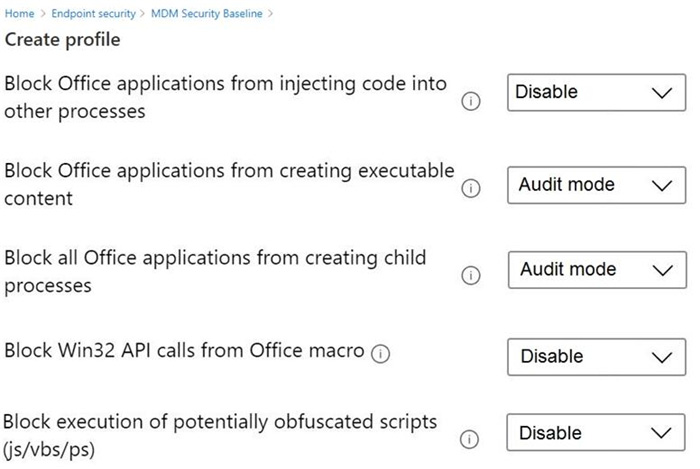
You have the ASR Endpoint Security profile shown in the ASR exhibit. (Click the ASR tab.)
You plan to deploy both profiles to devices enrolled in Microsoft Intune.
You need to identify how the following settings will be configured on the devices:
Block Office applications from creating executable content
Block Win32 API calls from Office macro
Currently, the settings are disabled locally on each device.
What are the effective settings on the devices? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
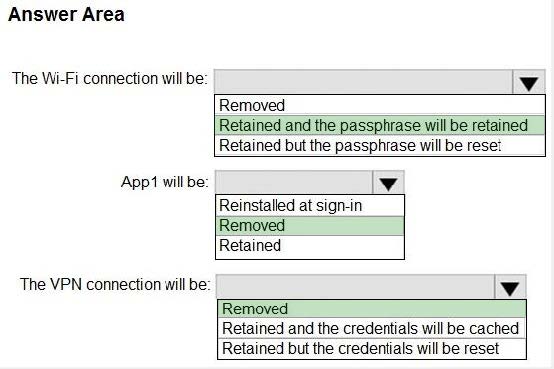
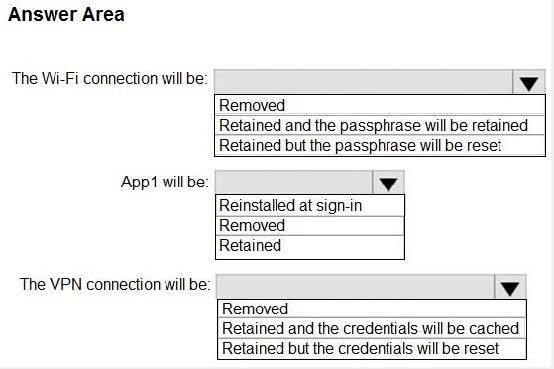
Question 227:
HOTSPOT
You have computers that run Windows 10 and are configured by using Windows Autopilot.
A user performs the following tasks on a computer named Computer1:
1.
Creates a VPN connection to the corporate network
2.
Installs a Microsoft Store app named App1
3.
Connections to a Wi-Fi network
You perform a Windows Autopilot Reset on Computer1.
What will be the state of the computer when the user signs in? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
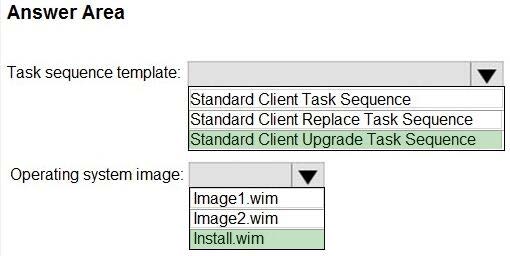
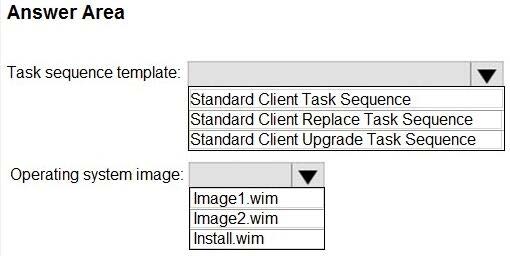
Question 228:
HOTSPOT
You have a Microsoft Deployment Toolkit (MDT) solution that is used to manage Windows 11 deployment tasks.
MDT contains the operating system images shown in the following table.
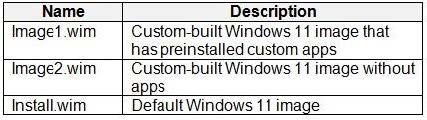
You need to perform a Windows 11-place upgrade on several computers that run Windows 10.
From the Deployment Workbench, you open the New Task Sequence Wizard.
You need to identify which task sequence template and which operating system image to use for the task sequence. The solution must minimize administrative effort.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
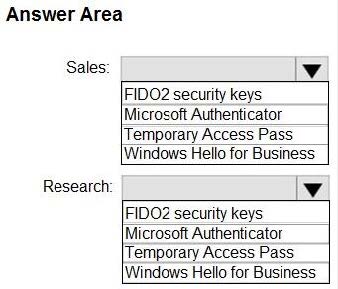
Question 229:
HOTSPOT
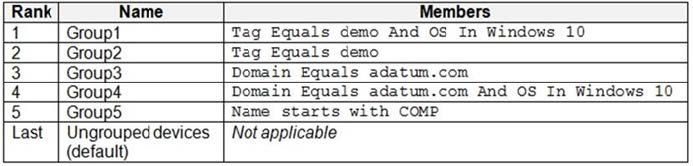
You have a Microsoft 365 subscription.
You need to enable passwordless authentication for all users. The solution must meet the following requirements:
1.
Users in the research department cannot use mobile devices and must authenticate from unmanaged Linux devices by using an alternative method.
2.
To access services, users in the sales department must authenticate by using their mobile phone.
3.
Administrative effort must be minimized.
Which authentication method should you use for each department? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
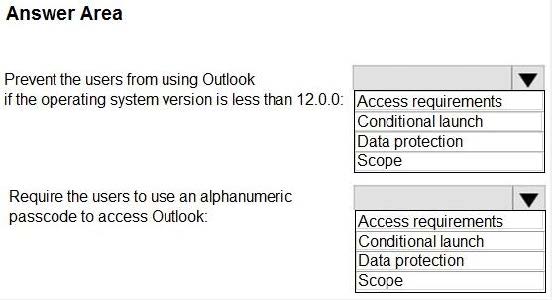
Question 230:
HOTSPOT
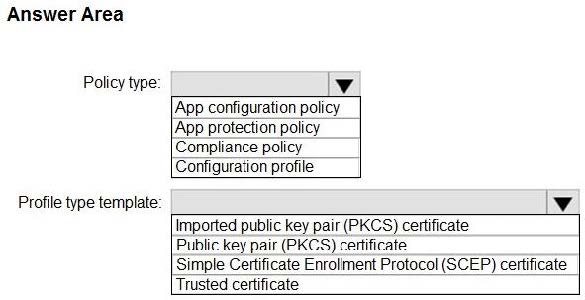
You have a Microsoft 365 subscription.
Users have iOS devices that are not enrolled in Microsoft Intune.
You create an app protection policy for the Microsoft Outlook app as shown in the exhibit. (Click the Exhibit tab.)
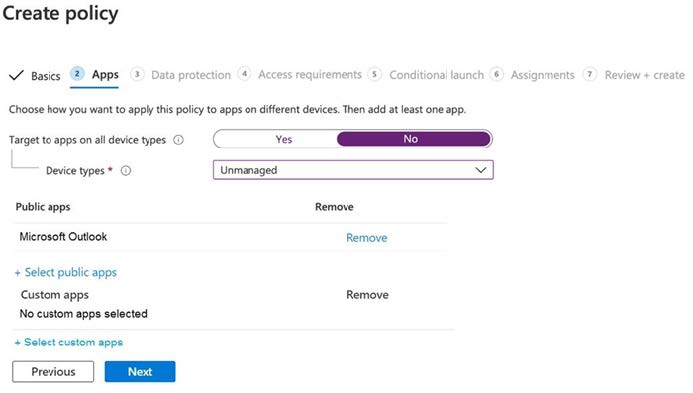
You need to configure the policy to meet the following requirements:
Prevent the users from using the Outlook app if the operating system version is less than 12.0.0.
Require the users to use an alphanumeric passcode to access the Outlook app.
What should you configure in an app protection policy for each requirement? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Hot Area:
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your MD-102 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.