Exam Details
Exam Code
:MS-100Exam Name
:Microsoft 365 Identity and ServicesCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:535 Q&AsLast Updated
:Mar 24, 2025
Microsoft Microsoft Certifications MS-100 Questions & Answers
-
Question 71:
Your network contains an on-premises Active Directory domain.
You have a Microsoft 365 subscription.
You implement a directory synchronization solution that uses pass-through authentication.
You configure Microsoft Azure Active Directory (Azure AD) smart lockout as shown in the following exhibit.
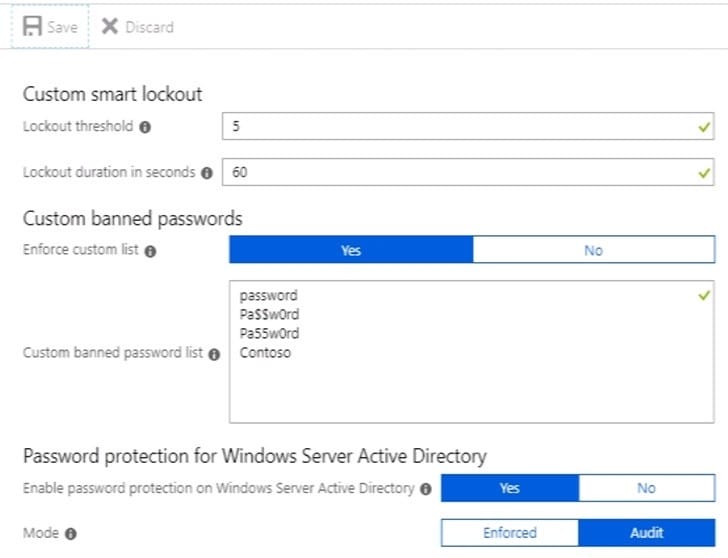
You discover that Active Directory users can use the passwords in the custom banned passwords list.
You need to ensure that banned passwords are effective for all users.
Which three actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. From a domain controller, install the Azure AD Password Protection Proxy.
B. From a domain controller, install the Microsoft AAD Application Proxy connector.
C. From Custom banned passwords, modify the Enforce custom list setting.
D. From Password protection for Windows Server Active Directory, modify the Mode setting.
E. From all the domain controllers, install the Azure AD Password Protection DC Agent.
F. From Active Directory, modify the Default Domain Policy.
-
Question 72:
You have a Microsoft Azure Active Directory (Azure AD) tenant named contoso.onmicrosoft.com.
An external user has a Microsoft account that uses an email address of [email protected].
An administrator named Admin1 attempts to create a user account for the external user and receives the error message shown in the following exhibit.
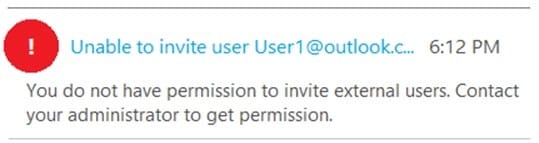
You need to ensure that Admin1 can add the user.
What should you do from the Azure Active Directory admin center?
A. Add a custom domain name named outlook.com.
B. Modify the Authentication methods.
C. Modify the External collaboration settings.
D. Assign Admin1 the Security administrator role.
-
Question 73:
You have a Microsoft 365 subscription that contains several Microsoft SharePoint Online sites.
You discover that users from your company can invite external users to access files on the SharePoint sites.
You need to ensure that the company users can invite only authenticated guest users to the sites.
What should you do?
A. From the Microsoft 365 admin center, configure a partner relationship.
B. From SharePoint Online Management Shell, run the Set-SPOSite cmdlet.
C. From the Azure Active Directory admin center, configure a conditional access policy.
D. From the SharePoint admin center, configure the sharing settings.
-
Question 74:
Your network contains an on-premises Active Directory domain. The domain contains 2,000 computers that run Windows 10.
You purchase a Microsoft 365 subscription.
You implement password hash synchronization and Azure Active Directory (Azure AD) Seamless Single Sign-On (Seamless SSO).
You need to ensure that users can use Seamless SSO from the Windows 10 computers.
What should you do?
A. Create a conditional access policy in Azure AD.
B. Deploy an Azure AD Connect staging server.
C. Join the computers to Azure AD.
D. Modify the Intranet zone settings by using Group Policy
-
Question 75:
You need to meet the security requirement for the vendors. What should you do?
A. From the Azure portal, modify the authentication methods.
B. From Azure Cloud Shell, run the New-AzureADMSInvitation and specify the -InvitedIserEmailAddress cmdlet.
C. From Azure Cloud Shell, run the Set-MsolUserPrincipalNameand specify the -tenantIDparameter.
D. From the Azure portal, add an identity provider.
-
Question 76:
You need to meet the security requirement for the vendors.
What should you do?
A. From Azure Cloud Shell, run the Set-MsolUserPrincipalName and specify the -tenantID parameter.
B. From Azure Cloud Shell, run the Set-AzureADUserExtension cmdlet.
C. Azure Cloud Shell, run the New-AzureADUser cmdlet and specify the-UserPrincipalName parameter.
D. From Azure Cloud Shell, run the New-AzureADMSInvitation cmdlet and specify the -InvitedUserEmailAddress parameter.
-
Question 77:
You need to assign User2 the required roles to meet the security requirements and the technical requirements. To which two roles should you assign User2? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
A. the Exchange View-only Organization Management role
B. the Microsoft 365 Records Management role
C. the Exchange Online Help Desk role
D. the Microsoft 365 Security Reader role
E. the Exchange Online Compliance Management role
-
Question 78:
To which Azure AD role should you add User4 to meet the security requirement?
A. Password administrator
B. Global administrator
C. Security administrator
D. Privileged role administrator
-
Question 79:
You need to meet the security requirement for Group1. What should you do?
A. Configure all users to sign in by using multi-factor authentication.
B. Modify the properties of Group1.
C. Assign Group1 a management role.
D. Modify the Password reset properties of the Azure AD tenant.
-
Question 80:
You need to meet the security requirement for the vendors. What should you do?
A. From the Azure portal, add an identity provider.
B. From Azure Cloud Shell, run the New-AzureADUser cmdlet and specify the -UserPrincipalName parameter.
C. From the Azure portal, create guest accounts.
D. From Azure Cloud Shell, run the New-AzureADUser cmdlet and specify the -UserType parameter.
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your MS-100 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.