Exam Details
Exam Code
:N10-007Exam Name
:CompTIA Network+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:1251 Q&AsLast Updated
:
CompTIA CompTIA Certifications N10-007 Questions & Answers
-
Question 111:
A network technician receives the following command output from a Linux-based machine:
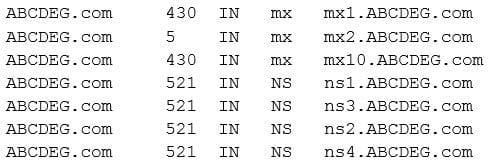
Which of the following commands did the network technician run?
A. iptables –f ABCDEG.com
B. dig –t ANY ABCDEG.com
C. NMAP –t ABCDEG.com
D. netstat –a ACDEG.com
-
Question 112:
Allowing data to be centrally stored and accessed by multiple devices on an isolated subnet is BEST understood as:
A. NAS
B. iSCSI
C. SAN
D. FCoE
-
Question 113:
A network technician has installed multiple new lightweight access points across the network. Which of the following devices should the technician use to manage the new access points?
A. Wireless controller
B. SSH
C. DHCP server
D. Content filter
E. WiFi analyzer
-
Question 114:
Management is concerned there is excessive traffic on the network. A network technician wants to run a quick port scan to see any systems that have open ports. Which of the following tools should be used to do this?
A. tcpdump
B. dig
C. nmap
D. netstat
-
Question 115:
A company's web-based application has a database that is set up for high availability in case of a failure. Which of the following is necessary to achieve this type of setup?
A. A virtual IP pointing to the active DB
B. A static IP pointing to the passive DB
C. A private IP pointing to the web front end
D. A private IP pointing to the web proxy
-
Question 116:
A network technician is creating a diagram of network termination points in the building. The technician diagrammed the core network room and now needs to diagram the auxiliary network closets. Which of the following is the technician MOST likely going to add to the diagram?
A. IDF
B. MDF
C. VRF
D. TDM
-
Question 117:
A company runs Linux servers in its own datacenter and also on a popular public cloud service provider. The servers hosted by the cloud provider can only be accessed with proper authorization and are only accessed by the company's datacenter. Which of the following BEST describes the type of cloud architecture being used? (Choose two.)
A. Private
B. Hybrid
C. Public
D. IaaS
E. PaaS
F. SaaS
-
Question 118:
A technician wants to have the ability to transfer files from home to the company's network on a regular basis. Which of the following is a remote access protocol the technician can utilize to bypass interactive user authentication by using a list of known host public keys?
A. FTP
B. SCP
C. TFTP
D. Telnet
-
Question 119:
Which of the following policies would be the MOST useful for defining the proper procedures when an employee is terminated abruptly?
A. Offboarding
B. Remote access
C. AUP
D. Incident response
E. DLP
-
Question 120:
Which of the following network topologies typically has all devices on a network directly connected to every other network device?
A. Mesh
B. Star
C. Ad hoc
D. Ring
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your N10-007 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.