Exam Details
Exam Code
:PT0-003Exam Name
:CompTIA PenTest+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:272 Q&AsLast Updated
:Apr 02, 2025
CompTIA CompTIA Certifications PT0-003 Questions & Answers
-
Question 81:
A penetration tester recently performed a social-engineering attack in which the tester found an employee of the target company at a local coffee shop and over time built a relationship with the employee. On the employee's birthday, the tester
gave the employee an external hard drive as a gift.
Which of the following social-engineering attacks was the tester utilizing?
A. Phishing
B. Tailgating
C. Baiting
D. Shoulder surfing
-
Question 82:
A penetration tester has obtained a low-privilege shell on a Windows server with a default configuration and now wants to explore the ability to exploit misconfigured service permissions. Which of the following commands would help the tester START this process?
A. certutil 璾rlcache 璼plit
-
Question 83:
Which of the following expressions in Python increase a variable val by one (Choose two.)
A. val++
B. +val
C. val=(val+1)
D. ++val
E. val=val++
F. val+=1
-
Question 84:
Which of the following documents describes specific activities, deliverables, and schedules for a penetration tester?
A. NDA
B. MSA
C. SOW
D. MOU
-
Question 85:
A penetration tester has prepared the following phishing email for an upcoming penetration test:
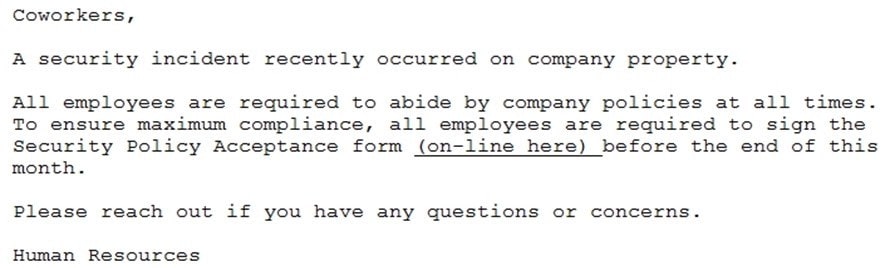
Which of the following is the penetration tester using MOST to influence phishing targets to click on the link?
A. Familiarity and likeness
B. Authority and urgency
C. Scarcity and fear
D. Social proof and greed
-
Question 86:
A company has recruited a penetration tester to conduct a vulnerability scan over the network. The test is confirmed to be on a known environment. Which of the following would be the BEST option to identify a system properly prior to performing the assessment?
A. Asset inventory B. DNS records
C. Web-application scan
D. Full scan
-
Question 87:
A penetration tester exploited a unique flaw on a recent penetration test of a bank. After the test was completed, the tester posted information about the exploit online along with the IP addresses of the exploited machines. Which of the following documents could hold the penetration tester accountable for this action?
A. ROE
B. SLA
C. MSA
D. NDA
-
Question 88:
A penetration tester needs to perform a test on a finance system that is PCI DSS v3.2.1 compliant. Which of the following is the MINIMUM frequency to complete the scan of the system?
A. Weekly
B. Monthly
C. Quarterly
D. Annually
-
Question 89:
A penetration tester who is performing a physical assessment of a company's security practices notices the company does not have any shredders inside the office building. Which of the following techniques would be BEST to use to gain confidential information?
A. Badge cloning
B. Dumpster diving
C. Tailgating
D. Shoulder surfing
-
Question 90:
The following PowerShell snippet was extracted from a log of an attacker machine: A penetration tester would like to identify the presence of an array. Which of the following line numbers would define the array?
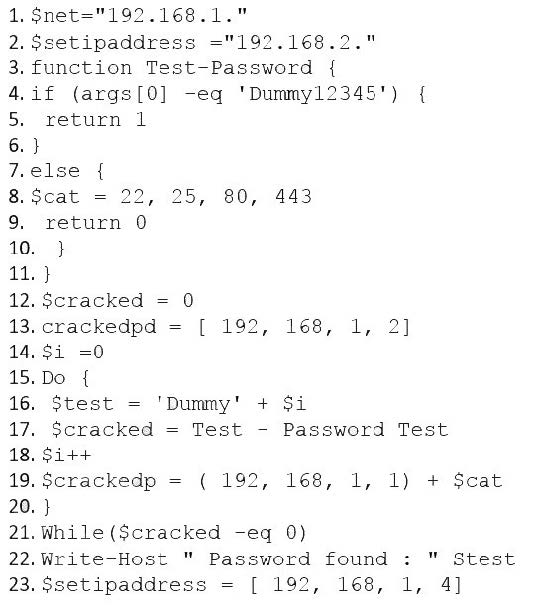
A. Line 8
B. Line 13
C. Line 19
D. Line 20
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PT0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.