Exam Details
Exam Code
:SC-200Exam Name
:Microsoft Security Operations AnalystCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:394 Q&AsLast Updated
:Mar 30, 2025
Microsoft Microsoft Certifications SC-200 Questions & Answers
-
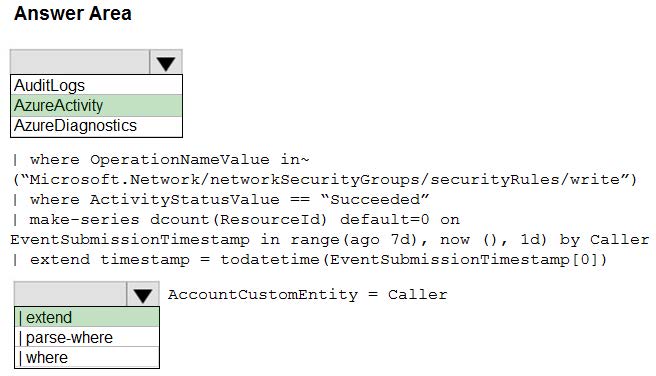
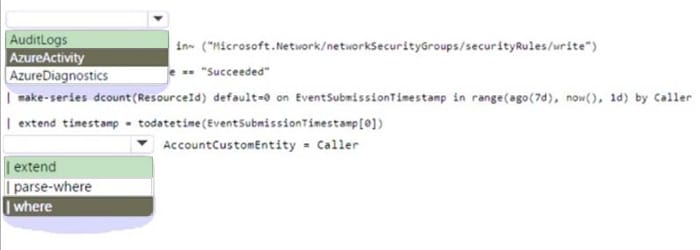
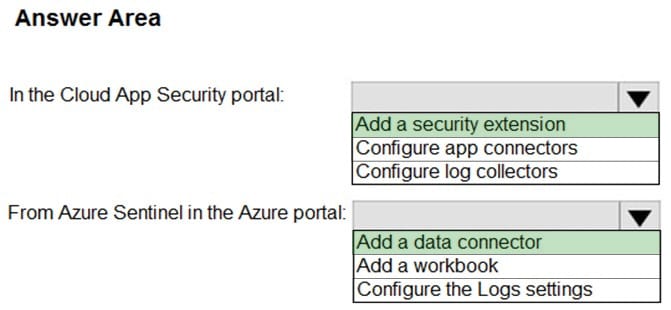
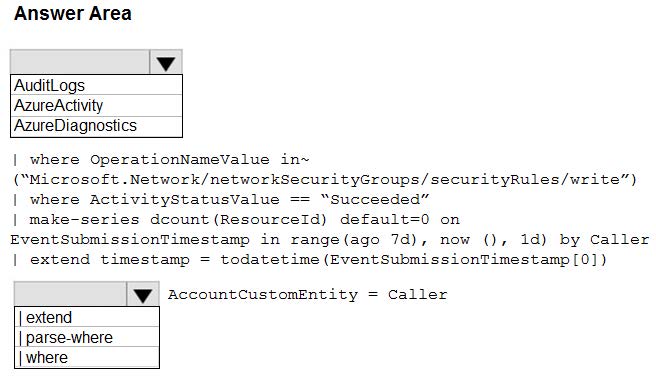
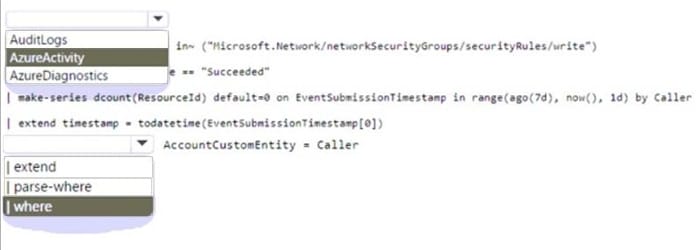
Question 231:
HOTSPOT
You have an Azure subscription that contains a Microsoft Sentinel workspace.
You need to create a hunting query using Kusto Query Language (KQL) that meets the following requirements:
1.
Identifies an anomalous number of changes to the rules of a network security group (NSG) made by the same security principal.
2.
Automatically associates the security principal with a Microsoft Sentinel entity.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
Question 232:
HOTSPOT
You have a Microsoft Sentinel workspace.
You need to configure a report visual for a custom workbook. The solution must meet the following requirements:
1.
The count and usage trend of AppDisplayName must be included.
2.
The TrendList column must be useable in a sparkline visual.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
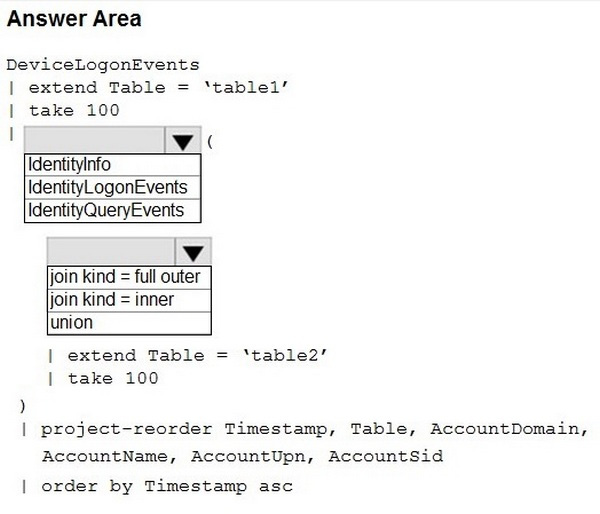
Question 233:
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You need to identify the 100 most recent sign-in attempts recorded on devices and AD DS domain controllers.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
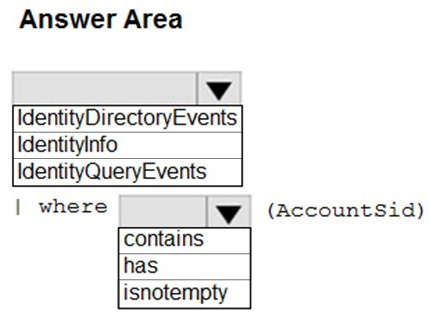
Question 234:
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You need to identify LDAP requests by AD DS users to enumerate AD DS objects.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
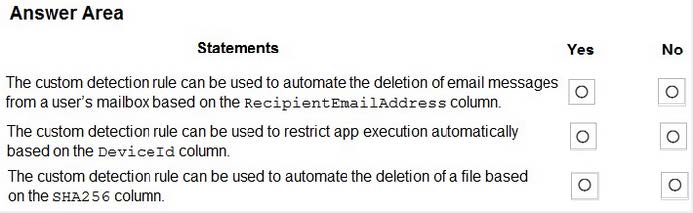
Question 235:
HOTSPOT
You have a custom detection rule that includes the following KQL query.

For each of the following statements, select Yes if True. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
-
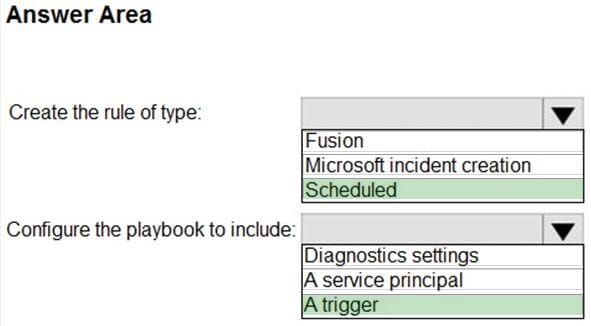
Question 236:
HOTSPOT
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
You need to identify all the interactive authentication attempts by the users in the finance department of your company.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
Question 237:
HOTSPOT
You have a Microsoft 365 E5 subscription that uses Microsoft Purview and contains a user named User1.
User1 shares a Microsoft Power BI report file from the Microsoft OneDrive folder of your company to an external user by using Microsoft Teams.
You need to identify which Power BI report file was shared.
How should you configure the search? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
Question 238:
HOTSPOT
You have an Azure subscription named Sub1 that uses Microsoft Defender for Cloud.
You have an Azure DevOps organization named AzDO1.
You need to integrate Sub1 and AzDO1. The solution must meet the following requirements:
1.
Detect secrets exposed in pipelines by using Defender for Cloud.
2.
Minimize administrative effort.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
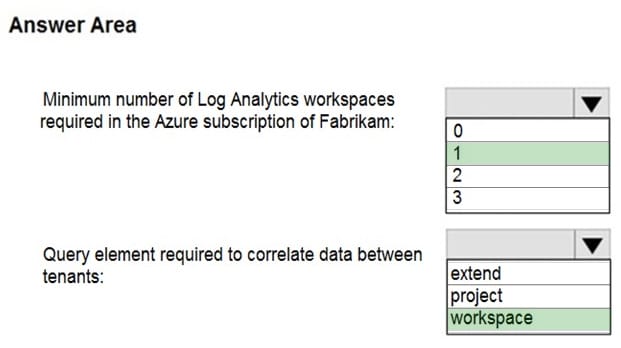
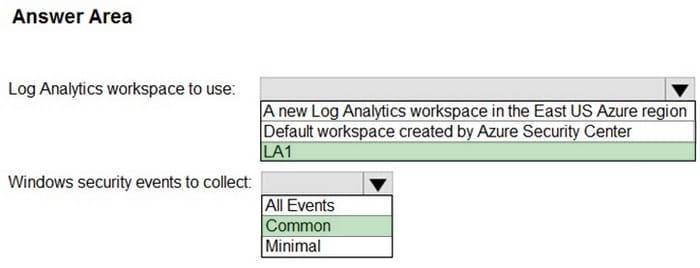
Question 239:
HOTSPOT
You have an Azure subscription that is linked to a hybrid Azure AD tenant and contains a Microsoft Sentinel workspace named Sentinel1.
You need to enable User and Entity Behavior Analytics (UEBA) for Sentinel and configure UEBA to use data collected from Active Directory Domain Services (AD DS).
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
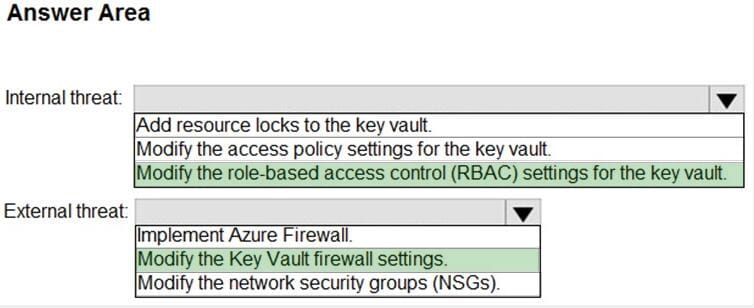
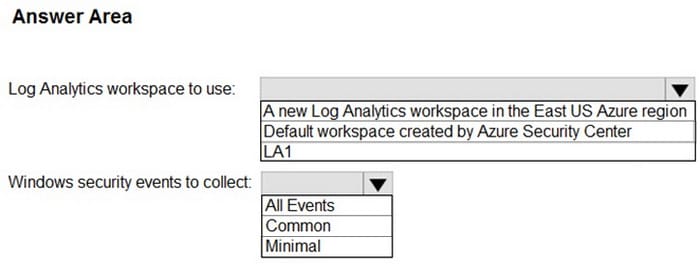
Question 240:
HOTSPOT
You have a Microsoft Sentinel workspace that contains a custom workbook.
You need to query the number of daily security alerts. The solution must meet the following requirements:
1.
Identify alerts that occurred during the last 30 days.
2.
Display the results in a timechart.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SC-200 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.