Exam Details
Exam Code
:SY0-601Exam Name
:CompTIA Security+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:1334 Q&AsLast Updated
:Mar 29, 2025
CompTIA CompTIA Certifications SY0-601 Questions & Answers
-
Question 91:
A security engineer learns that a non-critical application was compromised. The most recent version of the application includes a malicious reverse proxy while the application is running. Which of the following should the engineer is to quickly contain the incident with the least amount of impact?
A. Configure firewall rules to block malicious inbound access.
B. Manually uninstall the update that contains the backdoor.
C. Add the application hash to the organization's blocklist.
D. Tum off all computers that have the application installed.
-
Question 92:
Users report access to an application from an internal workstation is still unavailable to a specific server, even after a recent firewall rule implementation that was requested for this access. ICMP traffic is successful between the two devices. Which of the following tools should the security analyst use to help identify if the traffic is being blocked?
A. nmap
B. tracert
C. ping
D. ssh
-
Question 93:
While researching a data exfiltration event, the security team discovers that a large amount of data was transferred to a file storage site on the internet. Which of the following controls would work best to reduce the risk of further exfiltration using this method?
A. Data loss prevention
B. Blocking IP traffic at the firewall
C. Containerization
D. File integrity monitoring
-
Question 94:
Which of the following can reduce vulnerabilities by avoiding code reuse?
A. Memory management
B. Stored procedures
C. Normalization
D. Code obfuscation
-
Question 95:
Which of the following can be used to calculate the total loss expected per year due to a threat targeting an asset?
A. EF x asset value
B. ALE / SLE
C. MTBF x impact
D. SLE x ARO
-
Question 96:
Which of the following would provide guidelines on how to label new network devices as part of the initial configuration?
A. IP schema
B. Application baseline configuration
C. Standard naming convention policy
D. Wireless LAN and network perimeter diagram
-
Question 97:
A security administrator needs to provide secure access to internal networks for external partners The administrator has given the PSK and other parameters to the third-party security administrator. Which of the following is being used to establish this connection?
A. Kerberos
B. SSL/TLS
C. IPSec
D. SSH
-
Question 98:
A cybersecurity analyst at Company A is working to establish a secure communication channel with a counter part at Company B, which is 3,000 miles (4.828 kilometers) away. Which of the following concepts would help the analyst meet this goal m a secure manner?
A. Digital signatures
B. Key exchange
C. Salting
D. PPTP
-
Question 99:
A network engineer receives a call regarding multiple LAN-connected devices that are on the same switch. The devices have suddenly been experiencing speed and latency issues while connecting to network resources. The engineer enters the command show mac address-table and reviews the following output
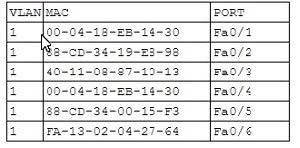
Which of the following best describes the attack that is currently in progress?
A. MAC flooding
B. Evil twin
C. ARP poisoning
D. DHCP spoofing
-
Question 100:
A software developer used open-source libraries to streamline development. Which of the following is the greatest risk when using this approach?
A. Unsecure root accounts
B. Lack of vendor support
C. Password complexity
D. Default settings
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-601 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.