Exam Details
Exam Code
:SY0-601Exam Name
:CompTIA Security+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:1334 Q&AsLast Updated
:Mar 29, 2025
CompTIA CompTIA Certifications SY0-601 Questions & Answers
-
Question 101:
A systems engineer thinks a business system has been compromised and is being used to exfiltrated data to a competitor The engineer contacts the CSIRT The CSIRT tells the engineer to immediately disconnect the network cable and to not do anything else.
Which of the following is the most likely reason for this request?
A. The CSIRT thinks an insider threat is attacking the network
B. Outages of business-critical systems cost too much money
C. The CSIRT does not consider the systems engineer to be trustworthy
D. Memory contents including fileles malware are lost when the power is turned off
-
Question 102:
A major manufacturing company updated its internal infrastructure and just started to allow OAuth application to access corporate data Data leakage is being reported.
Which of following most likely caused the issue?
A. Privilege creep
B. Unmodified default
C. TLS
D. Improper patch management
-
Question 103:
A retail store has a business requirement to deploy a kiosk computer In an open area The kiosk computer's operating system has been hardened and tested. A security engineer is concerned that someone could use removable media to
install a rootkit.
Which should the security engineer configure to BEST protect the kiosk computer?
A. Measured boot
B. Boot attestation
C. UEFI
D. EDR
-
Question 104:
A security administrator is compiling information from all devices on the local network in order to gain better visibility into user activities. Which of the following is the best solution to meet this objective?
A. SIEM
B. HIDS
C. CASB
D. EDR
-
Question 105:
Which of the following incident response phases should the proper collection of the detected 'ocs and establishment of a chain of custody be performed before?
A. Containment
B. Identification
C. Preparation
D. Recovery
-
Question 106:
While performing a threat-hunting exercise, a security analyst sees some unusual behavior occurring in an application when a user changes the display name. The security analyst decides to perform a static code analysis and receives the following pseudocode:
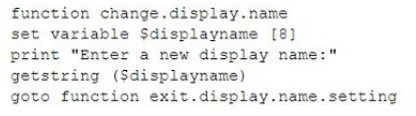
Which of the following attack types best describes the root cause of the unusual behavior?
A. Server-side request forgery
B. Improper error handling
C. Buffer overflow
D. SQL injection
-
Question 107:
A security team is engaging a third-party vendor to do a penetration test of a new proprietary application prior to its release. Which of the following documents would the third-party vendor most likely be required to review and sign?
A. SLA
B. NDA
C. MOU
D. AUP
-
Question 108:
A Chief Information Security Officer (CISO) wants to implement a new solution that can protect against certain categories of websites, whether the employee is in the offer or away. Which of the following solutions should the CISO implement?
A. VAF
B. SWG
C. VPN
D. WDS
-
Question 109:
While reviewing the /etc/shadow file, a security administrator notices files with the same values. Which of the following attacks should the administrator be concerned about?
A. Plaintext
B. Birthdat
C. Brute-force
D. Rainbow table
-
Question 110:
An engineer is using scripting to deploy a network in a cloud environment. Which the following describes this scenario?
A. SDLC
B. VLAN
C. SDN
D. SDV
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-601 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.