Exam Details
Exam Code
:CS0-003Exam Name
:CompTIA Cybersecurity Analyst (CySA+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:509 Q&AsLast Updated
:Mar 23, 2025
CompTIA CompTIA Certifications CS0-003 Questions & Answers
-
Question 91:
An organization has tracked several incidents that are listed in the following table:
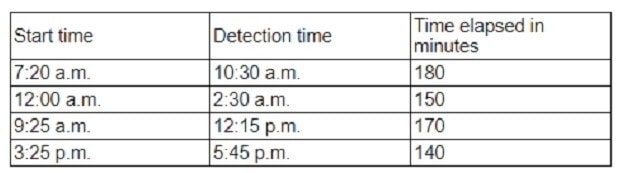
Which of the following is the organization's MTTD?
A. 140
B. 150
C. 160
D. 180
-
Question 92:
Which of the following would likely be used to update a dashboard that integrates.....?
A. Webhooks
B. Extensible Markup Language
C. Threat feed combination
D. JavaScript Object Notation
-
Question 93:
A Chief Information Security Officer wants to implement security by design, starting with the implementation of a security scanning method to identify vulnerabilities, including SQL injection, FRI, XSS, etc. Which of the following would most likely meet the requirement?
A. Reverse engineering
B. Known environment testing
C. Dynamic application security testing
D. Code debugging
-
Question 94:
An analyst is designing a message system for a bank. The analyst wants to include a feature that allows the recipient of a message to prove to a third party that the message came from the sender.
Which of the following information security goals is the analyst most likely trying to achieve?
A. Non-repudiation
B. Authentication
C. Authorization
D. Integrity
-
Question 95:
A security team identified several rogue Wi-Fi access points during the most recent network scan. The network scans occur once per quarter. Which of the following controls would best all ow the organization to identity rogue devices more quickly?
A. Implement a continuous monitoring policy.
B. Implement a BYOD policy.
C. Implement a portable wireless scanning policy.
D. Change the frequency of network scans to once per month.
-
Question 96:
An incident response analyst is investigating the root cause of a recent malware outbreak. Initial binary analysis indicates that this malware disables host security services and performs cleanup routines on it infected hosts, including deletion of initial dropper and removal of event log entries and prefetch files from the host. Which of the following data sources would most likely reveal evidence of the root cause? (Select two).
A. Creation time of dropper
B. Registry artifacts
C. EDR data
D. Prefetch files
E. File system metadata
F. Sysmon event log
-
Question 97:
A payroll department employee was the target of a phishing attack in which an attacker impersonated a department director and requested that direct deposit information be updated to a new account. Afterward, a deposit was made into the unauthorized account. Which of the following is one of the first actions the incident response team should take when they receive notification of the attack?
A. Scan the employee's computer with virus and malware tools.
B. Review the actions taken by the employee and the email related to the event
C. Contact human resources and recommend the termination of the employee.
D. Assign security awareness training to the employee involved in the incident.
-
Question 98:
A security analyst is responding to an indent that involves a malicious attack on a network. Data closet. Which of the following best explains how are analyst should properly document the incident?
A. Back up the configuration file for alt network devices
B. Record and validate each connection
C. Create a full diagram of the network infrastructure
D. Take photos of the impacted items
-
Question 99:
Which of the following should be updated after a lessons-learned review?
A. Disaster recovery plan
B. Business continuity plan
C. Tabletop exercise
D. Incident response plan
-
Question 100:
A manufacturer has hired a third-party consultant to assess the security of an OT network that includes both fragile and legacy equipment.
Which of the following must be considered to ensure the consultant does no harm to operations?
A. Employing Nmap Scripting Engine scanning techniques
B. Preserving the state of PLC ladder logic prior to scanning
C. Using passive instead of active vulnerability scans
D. Running scans during off-peak manufacturing hours
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CS0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.