Exam Details
Exam Code
:CS0-003Exam Name
:CompTIA Cybersecurity Analyst (CySA+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:509 Q&AsLast Updated
:Mar 23, 2025
CompTIA CompTIA Certifications CS0-003 Questions & Answers
-
Question 451:
A security analyst is tasked with prioritizing vulnerabilities for remediation. The relevant company security policies are shown below:
1.
Security Policy 1006: Vulnerability Management
2.
The Company shall use the CVSSv3.1 Base Score Metrics (Exploitability and Impact) to prioritize the remediation of security vulnerabilities.
3.
In situations where a choice must be made between confidentiality and availability, the Company shall prioritize confidentiality of data over availability of systems and data.
4.
The Company shall prioritize patching of publicly available systems and services over patching of internally available system.
According to the security policy, which of the following vulnerabilities should be the highest priority to patch?
A. Name: THOR HAMMER CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H internal System
B. Name: CAP.SHIELD CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N External System
C. Name: LOKI.DAGGER CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H External System
D. Name: THANOS.GAUNTLET CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N Internal System
-
Question 452:
Which of the following will most likely ensure that mission-critical services are available in the event of an incident?
A. Business continuity plan
B. Vulnerability management plan
C. Disaster recovery plan
D. Asset management plan
-
Question 453:
Which of the following items should be included in a vulnerability scan report? (Choose two.)
A. Lessons learned
B. Service-level agreement
C. Playbook
D. Affected hosts
E. Risk score
F. Education plan
-
Question 454:
The Chief Executive Officer of an organization recently heard that exploitation of new attacks in the industry was happening approximately 45 days after a patch was released. Which of the following would best protect this organization?
A. A mean time to remediate of 30 days
B. A mean time to detect of 45 days
C. A mean time to respond of 15 days
D. Third-party application testing
-
Question 455:
A recent zero-day vulnerability is being actively exploited, requires no user interaction or privilege escalation, and has a significant impact to confidentiality and integrity but not to availability. Which of the following CVE metrics would be most accurate for this zero-day threat?
A. CVSS: 31/AV: N/AC: L/PR: N/UI: N/S: U/C: H: K/A: L
B. CVSS:31/AV:K/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:L
C. CVSS:31/AV:N/AC:L/PR:N/UI:H/S:U/C:L/I:N/A:H
D. CVSS:31/AV:L/AC:L/PR:R/UI:R/S:U/C:H/I:L/A:H
-
Question 456:
A company's user accounts have been compromised. Users are also reporting that the company's internal portal is sometimes only accessible through HTTP, other times; it is accessible through HTTPS. Which of the following most likely describes the observed activity?
A. There is an issue with the SSL certificate causinq port 443 to become unavailable for HTTPS access
B. An on-path attack is being performed by someone with internal access that forces users into port 80
C. The web server cannot handle an increasing amount of HTTPS requests so it forwards users to port 80
D. An error was caused by BGP due to new rules applied over the company's internal routers
-
Question 457:
A security analyst recently joined the team and is trying to determine which scripting language is being used in a production script to determine if it is malicious. Given the following script:
foreach ($user in Get-Content .\this.txt)
{
Get-ADUser $user -Properties primaryGroupID |select-object pr:
Add-ADGroupMember "Domain Users" -Members $user
Set-ADUser $user -Replace 0(primaryGroupID=513)
}
Which of the following scripting languages was used in the script?
A. PowerShel
B. Ruby
C. Python
D. Shell script
-
Question 458:
Which of the following tools would work best to prevent the exposure of PII outside of an organization?
A. PAM
B. IDS
C. PKI
D. DLP
-
Question 459:
An organization conducted a web application vulnerability assessment against the corporate website, and the following output was observed:
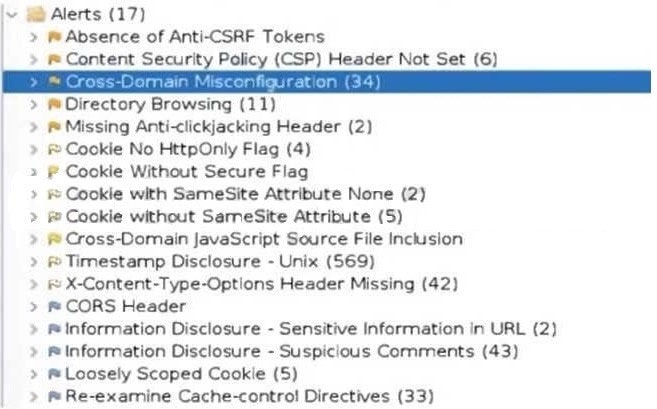
Which of the following tuning recommendations should the security analyst share?
A. Set an HttpOnlvflaq to force communication by HTTPS
B. Block requests without an X-Frame-Options header
C. Configure an Access-Control-Allow-Origin header to authorized domains
D. Disable the cross-origin resource sharing header
-
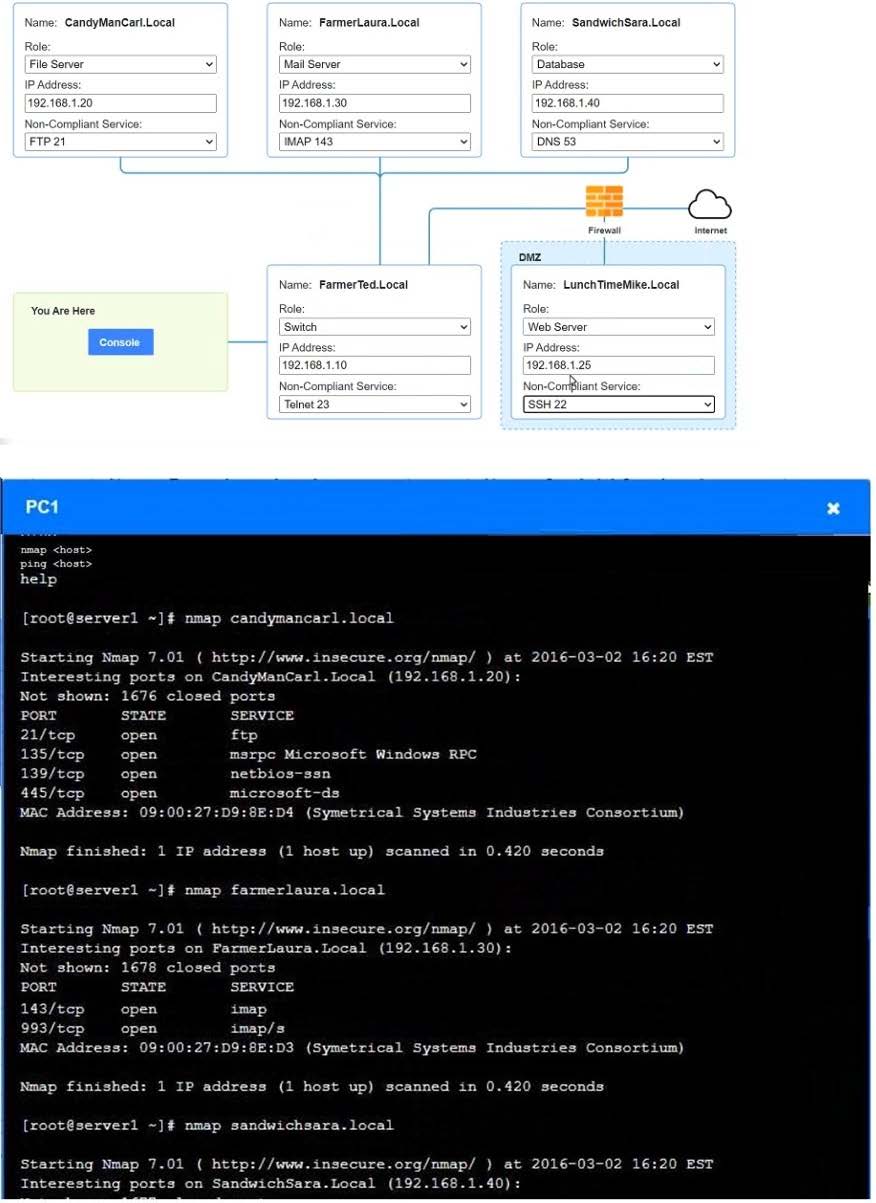
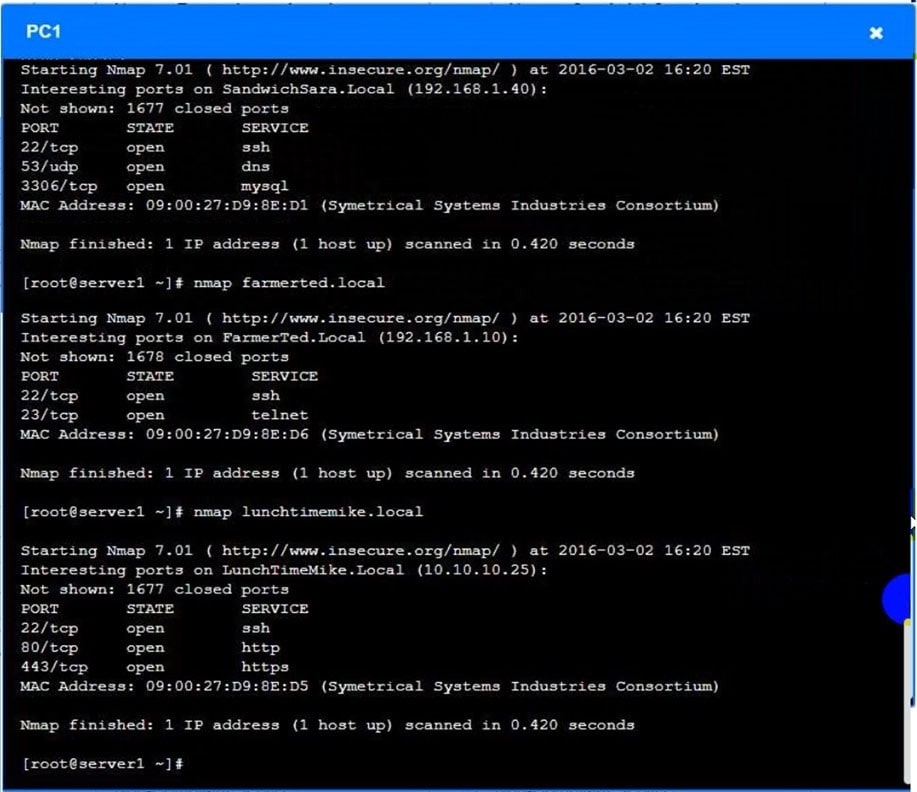
Question 460:
SIMULATION
You are a penetration tester who is reviewing the system hardening guidelines for a company. Hardening guidelines indicate the following.
1.
There must be one primary server or service per device.
2.
Only default port should be used
3.
Non-secure protocols should be disabled.
4.
The corporate internet presence should be placed in a protected subnet Instructions :
Using the available tools, discover devices on the corporate network and the services running on these devices.
You must determine
1.
ip address of each device
2.
The primary server or service each device
3.
The protocols that should be disabled based on the hardening guidelines
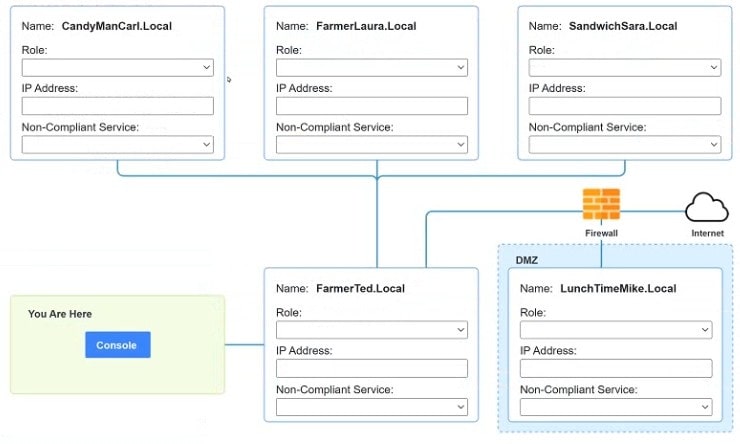
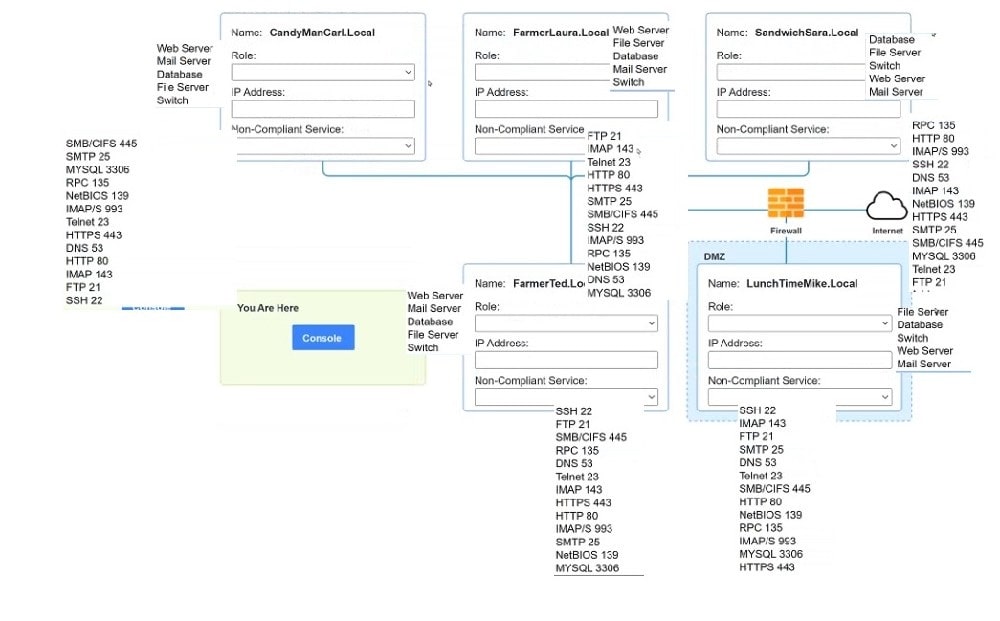
A. see the answer below in explanation.
B. PlaceHoder
C. PlaceHoder
D. PlaceHoder
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CS0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.