Exam Details
Exam Code
:CS0-003Exam Name
:CompTIA Cybersecurity Analyst (CySA+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:509 Q&AsLast Updated
:Mar 31, 2025
CompTIA CompTIA Certifications CS0-003 Questions & Answers
-
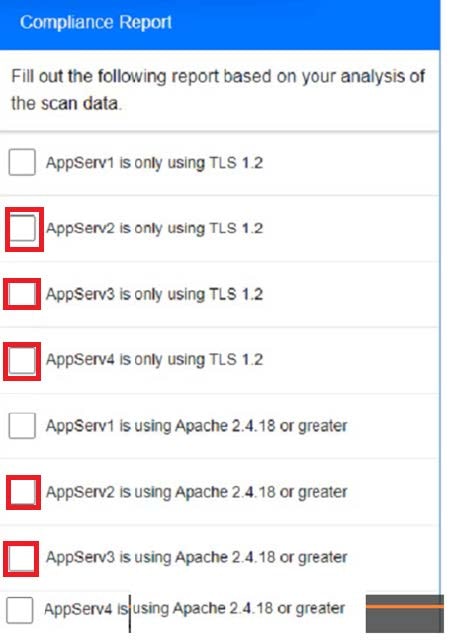
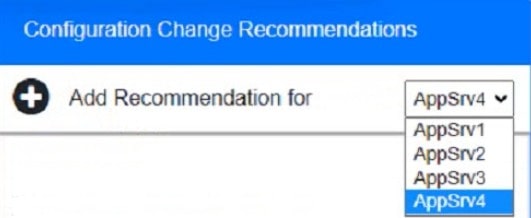
Question 131:
SIMULATION You are a cybersecurity analyst tasked with interpreting scan data from Company As servers You must verify the requirements are being met for all of the servers and recommend changes if you find they are not The company's hardening guidelines indicate the following:
1.
TLS 1 2 is the only version of TLS running.
2.
Apache 2.4.18 or greater should be used.
3.
Only default ports should be used.
INSTRUCTIONS
using the supplied data. record the status of compliance With the company's guidelines for each server.
The question contains two parts: make sure you complete Part 1 and Part 2. Make recommendations for Issues based ONLY on the hardening guidelines provided.
Part 1: AppServ1:
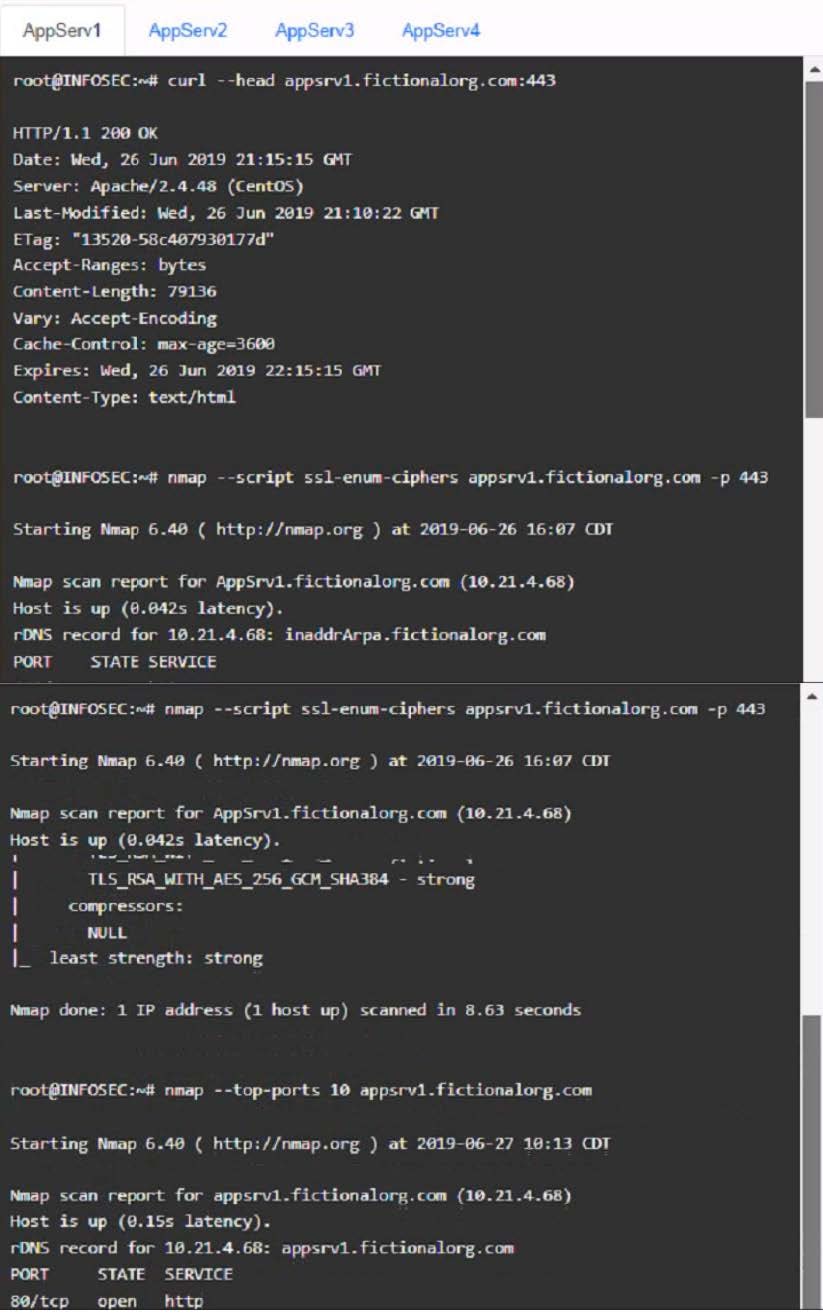
AppServ2:
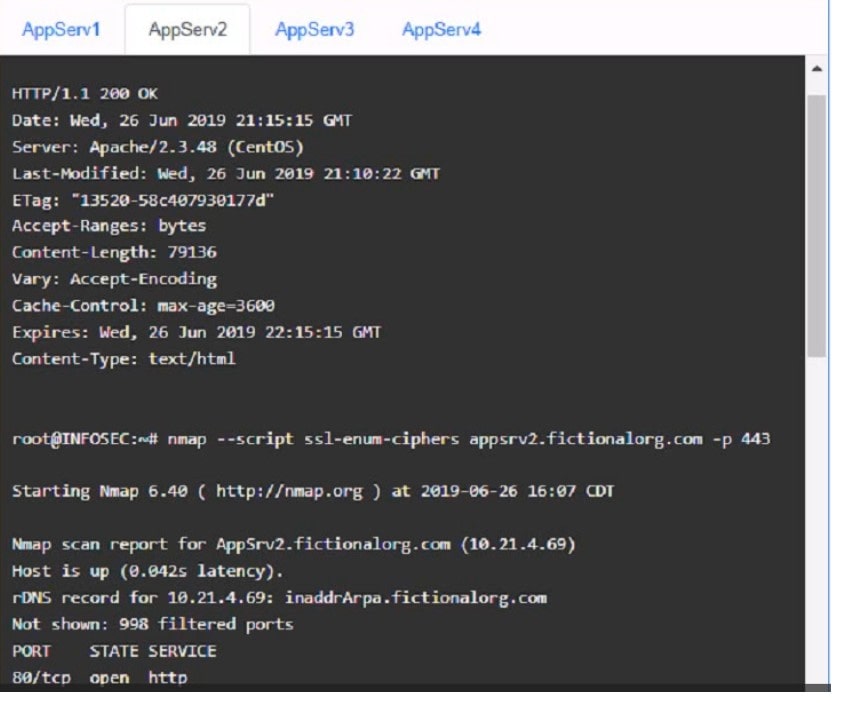
AppServ3:
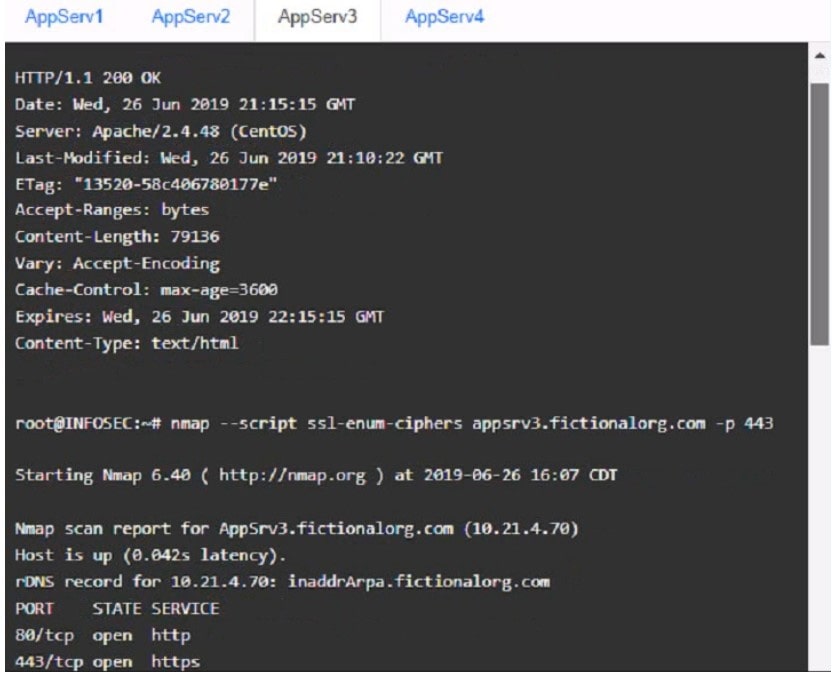
AppServ4:
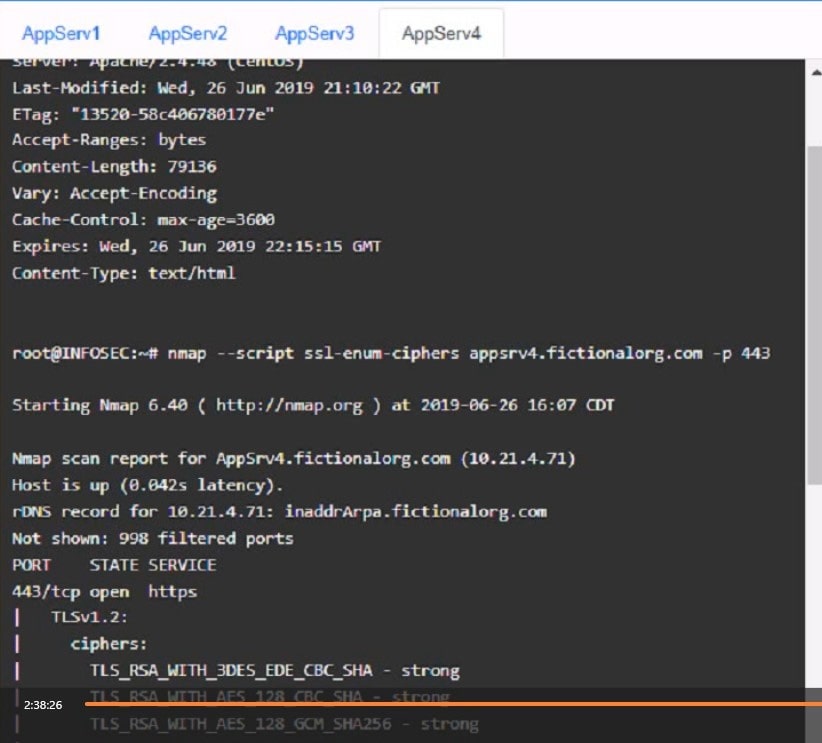
Part 2:
A. See the solution below in Explanation.
B. PlaceHoder
C. PlaceHoder
D. PlaceHoder
-
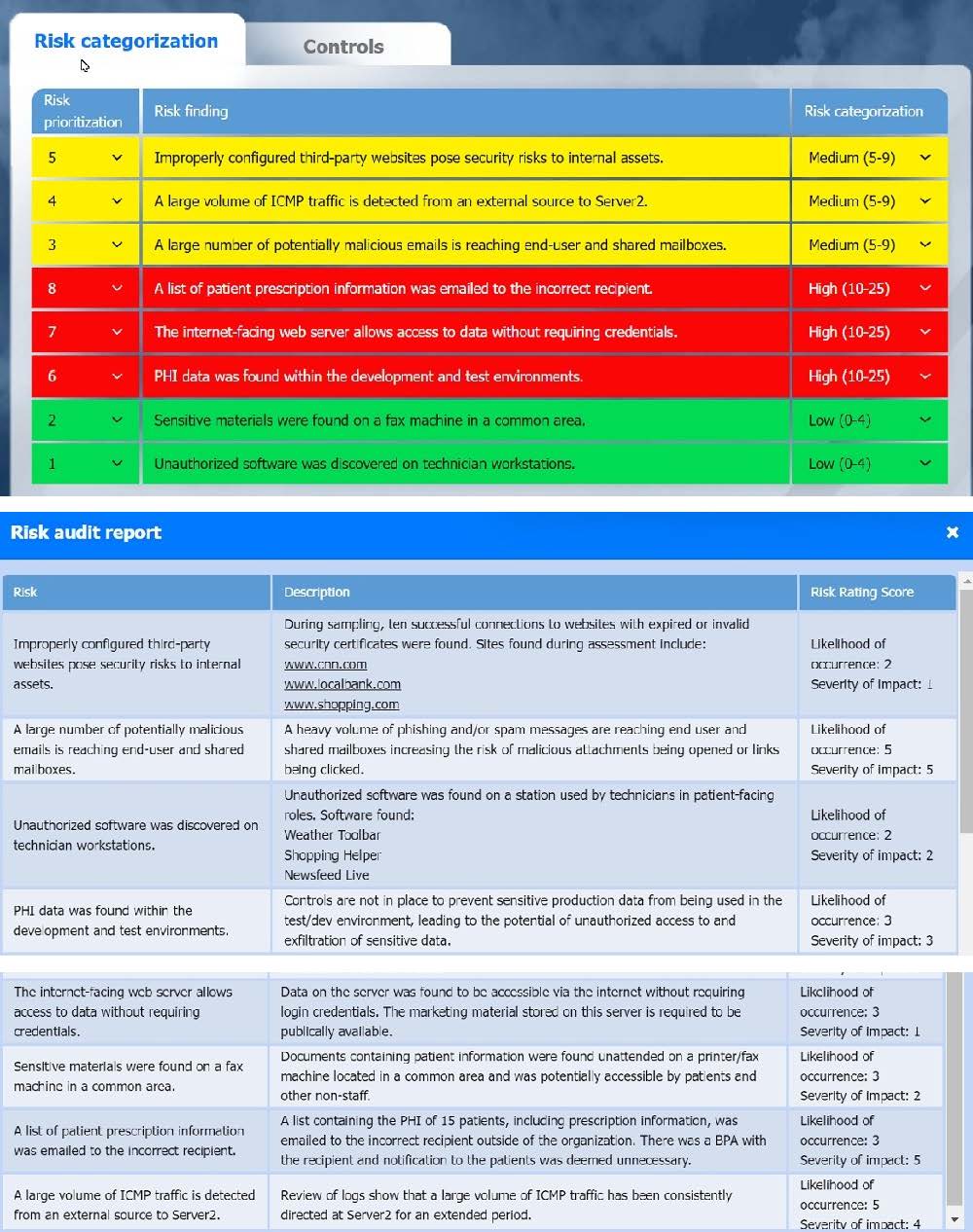
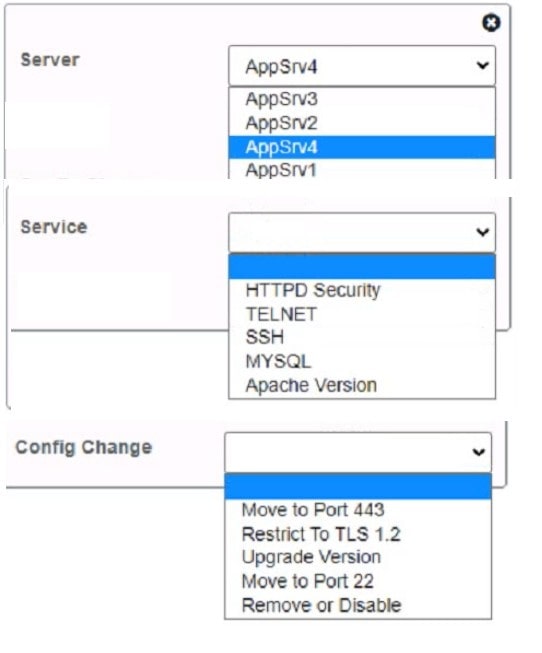
Question 132:
SIMULATION
A healthcare organization must develop an action plan based on the findings from a risk assessment. The action plan must consist of:
1.
Risk categorization
2.
Risk prioritization
3.
Implementation of controls
INSTRUCTIONS
Click on the audit report, risk matrix, and SLA expectations documents to review their contents.
On the Risk categorization tab, determine the order in which the findings must be prioritized for remediation according to the risk rating score. Then, assign a categorization to each risk.
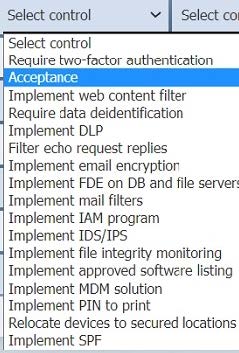
On the Controls tab, select the appropriate control(s) to implement for each risk finding.
Findings may have more than one control implemented. Some controls may be used more than once or not at all.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A. See the solution below in Explanation.
B. PlaceHoder
C. PlaceHoder
D. PlaceHoder
-
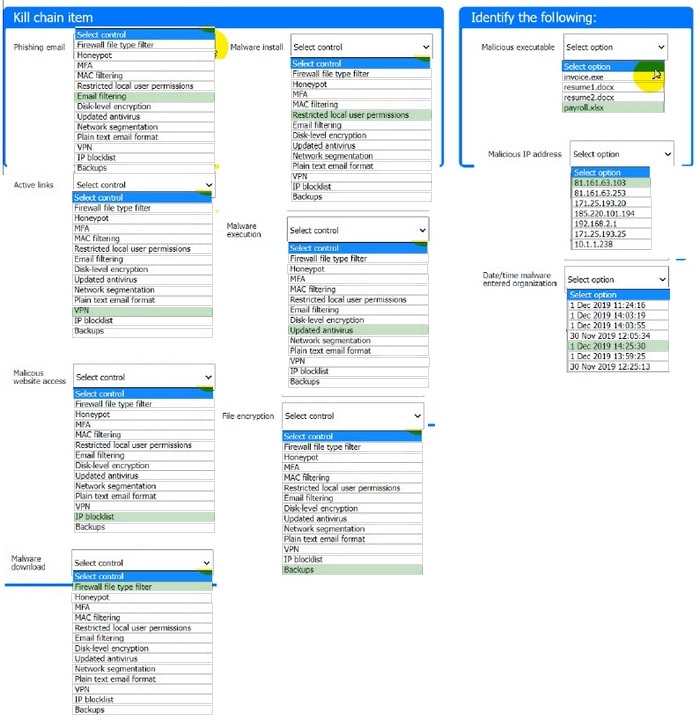
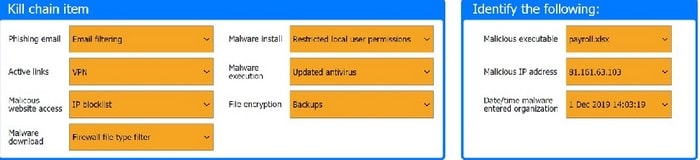
Question 133:
HOTSPOT
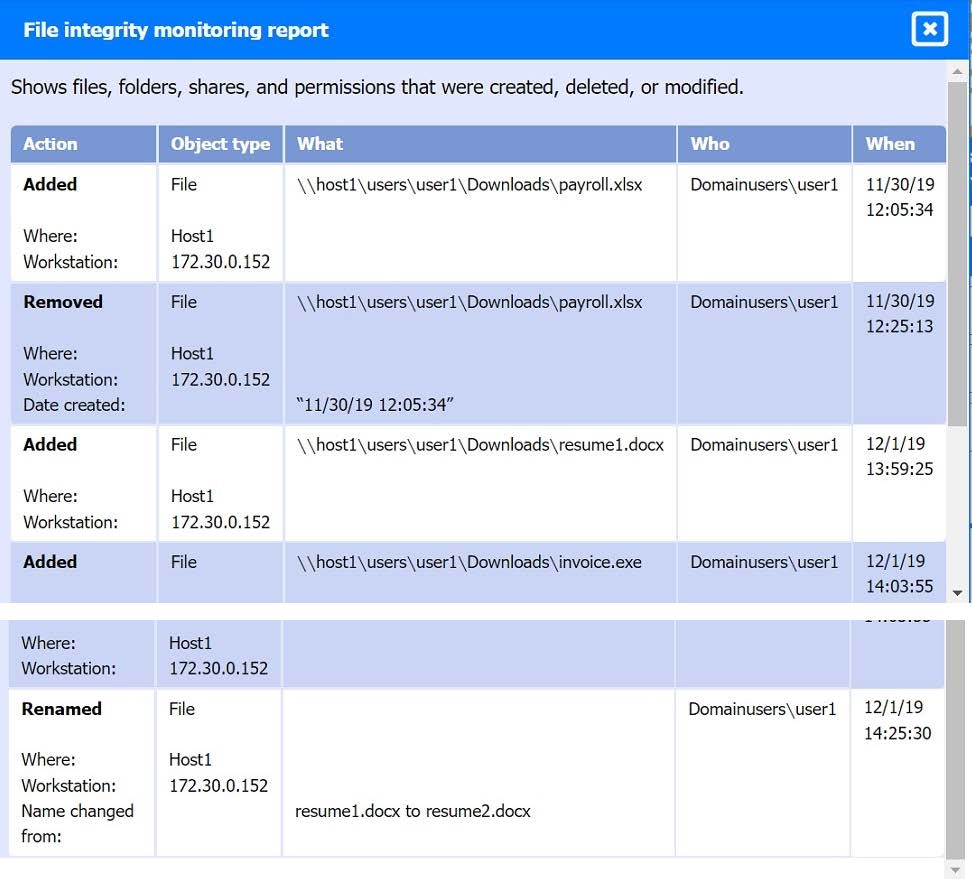
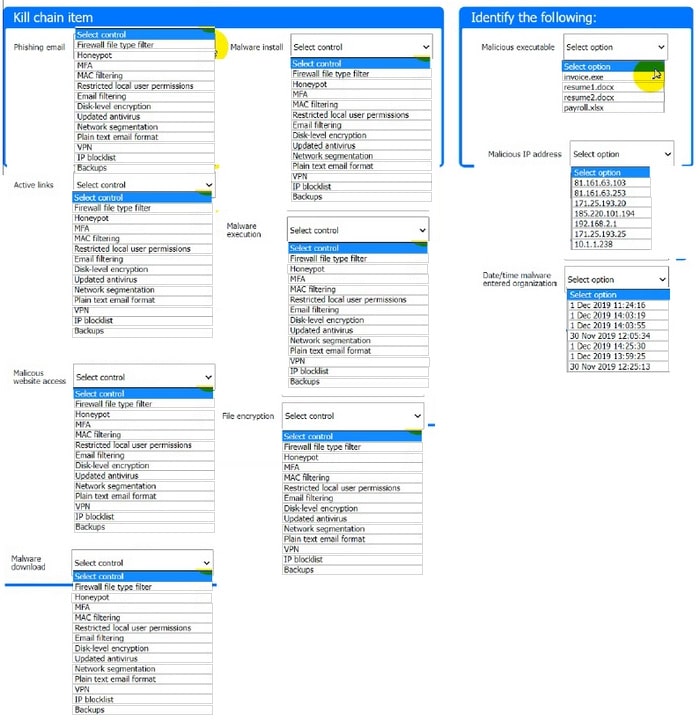
A company recently experienced a security incident. The security team has determined a user clicked on a link embedded in a phishing email that was sent to the entire company. The link resulted in a malware download, which was subsequently installed and run. INSTRUCTIONS Part 1 Review the artifacts associated with the security incident. Identify the name of the malware, the malicious IP address, and the date and time when the malware executable entered the organization. Part 2
Review the kill chain items and select an appropriate control for each that would improve the security posture of the organization and would have helped to prevent this incident from occurring. Each control may only be used once, and not all controls will be used.

Firewall log:
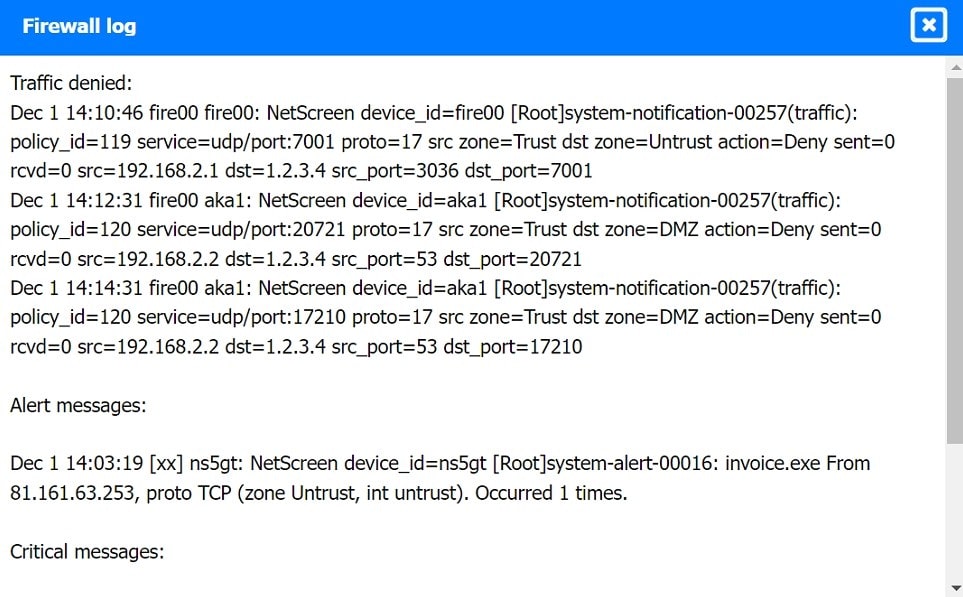
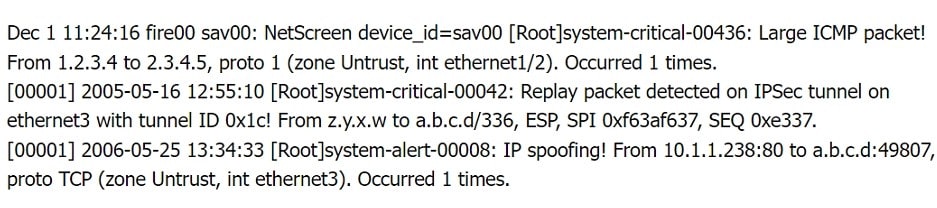
File integrity Monitoring Report:
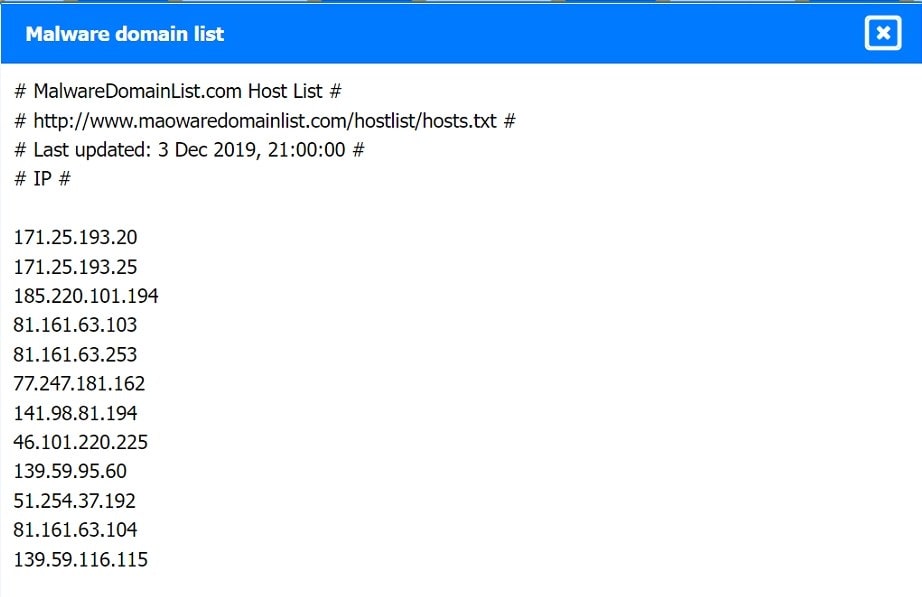
Malware domain list:
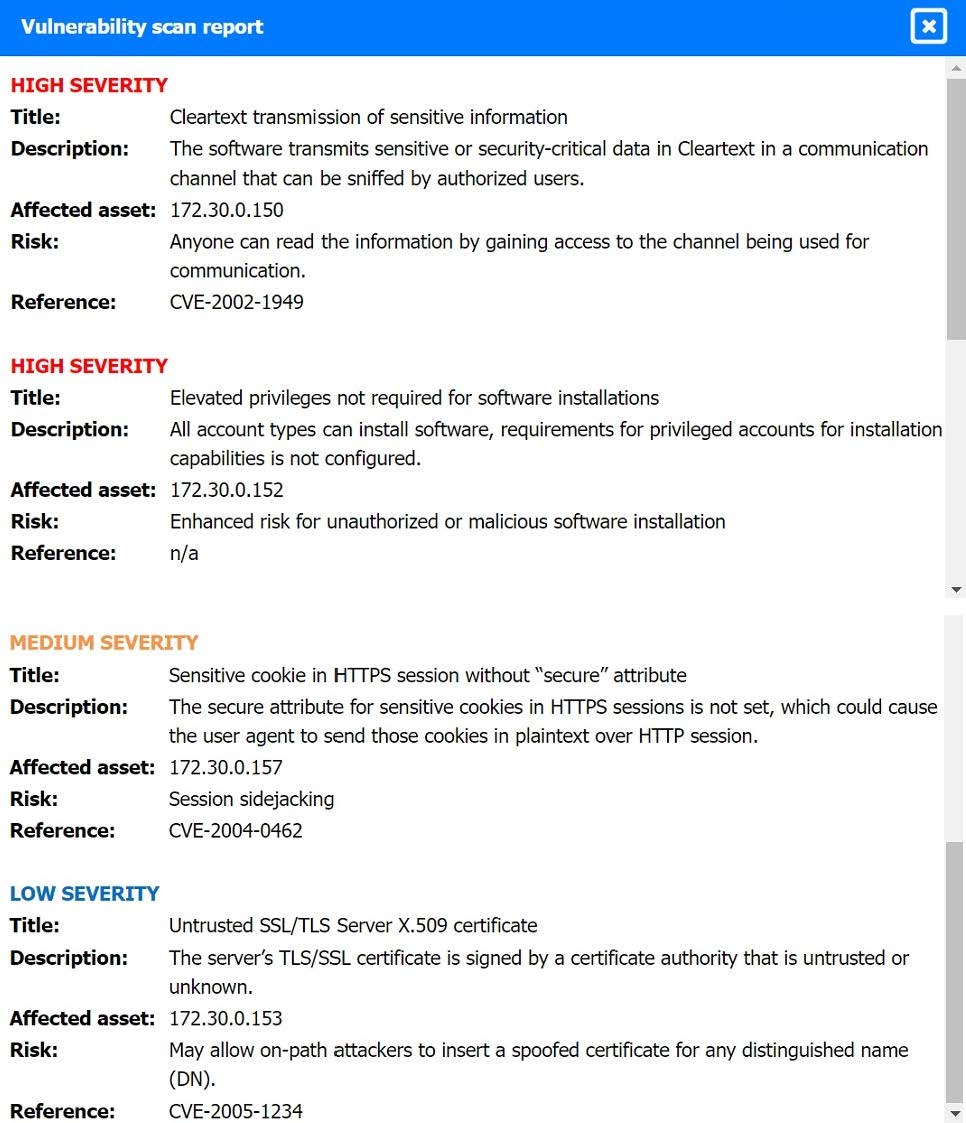
Vulnerability Scan Report:
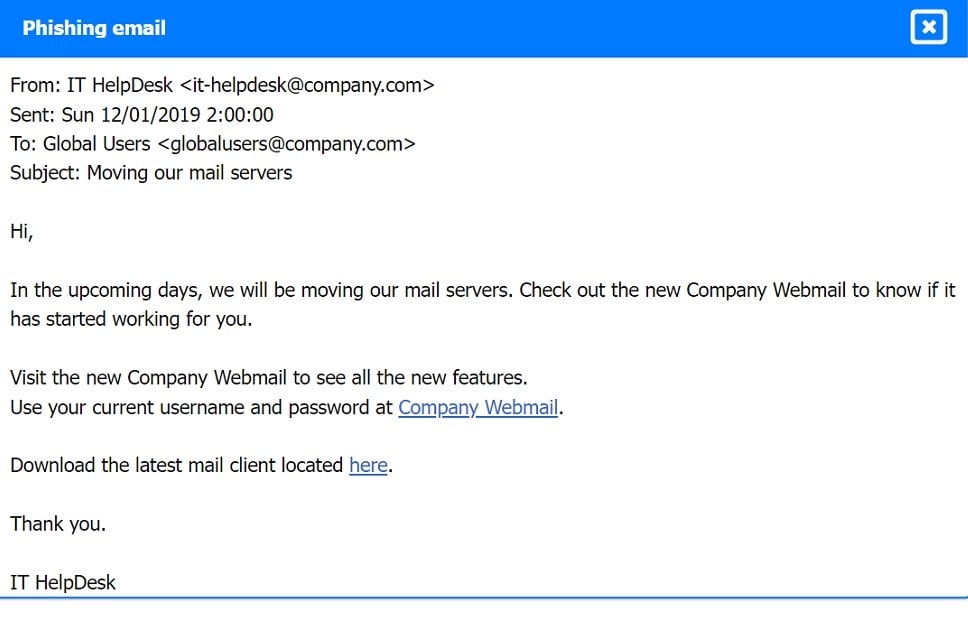
Phishing Email:
Hot Area:
-
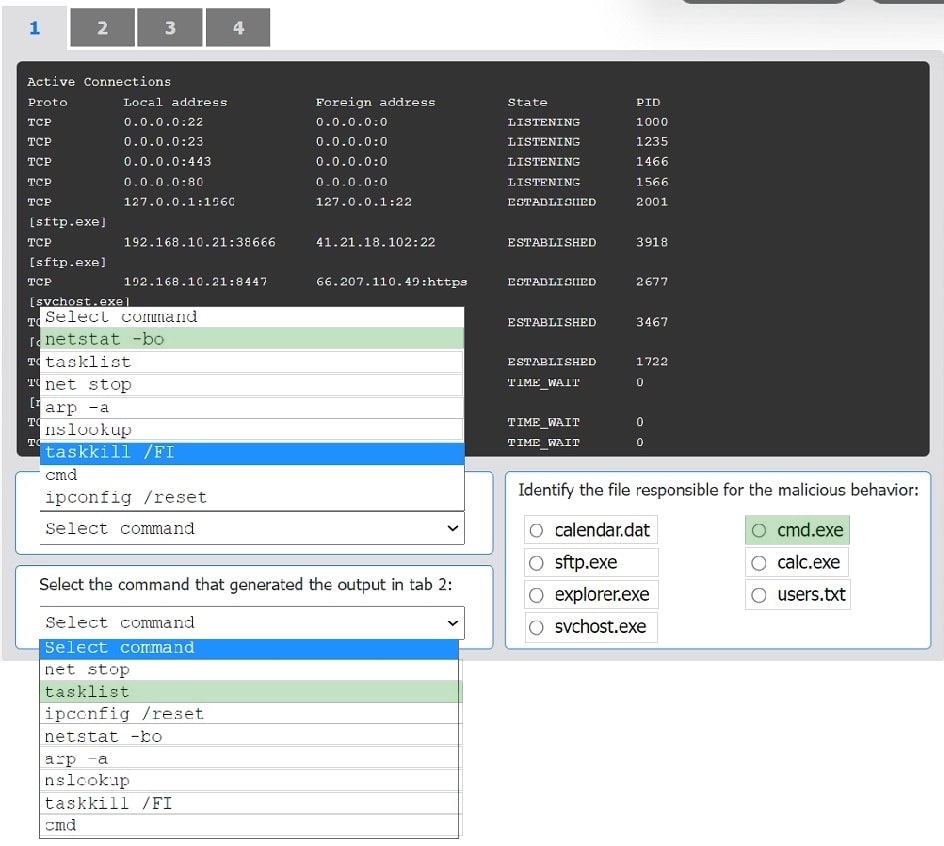
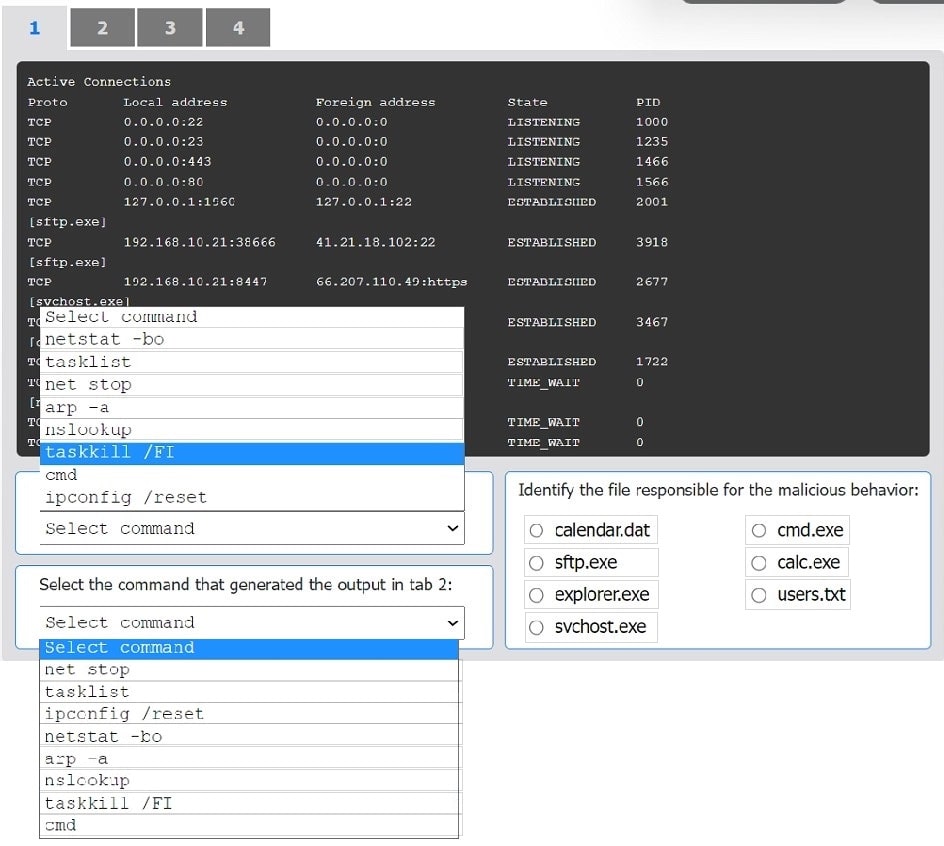
Question 134:
HOTSPOT
An organization has noticed large amounts of data are being sent out of its network. An analyst is identifying the cause of the data exfiltration.
INSTRUCTIONS
Select the command that generated the output in tabs 1 and 2.
Review the output text in all tabs and identify the file responsible for the malicious behavior.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
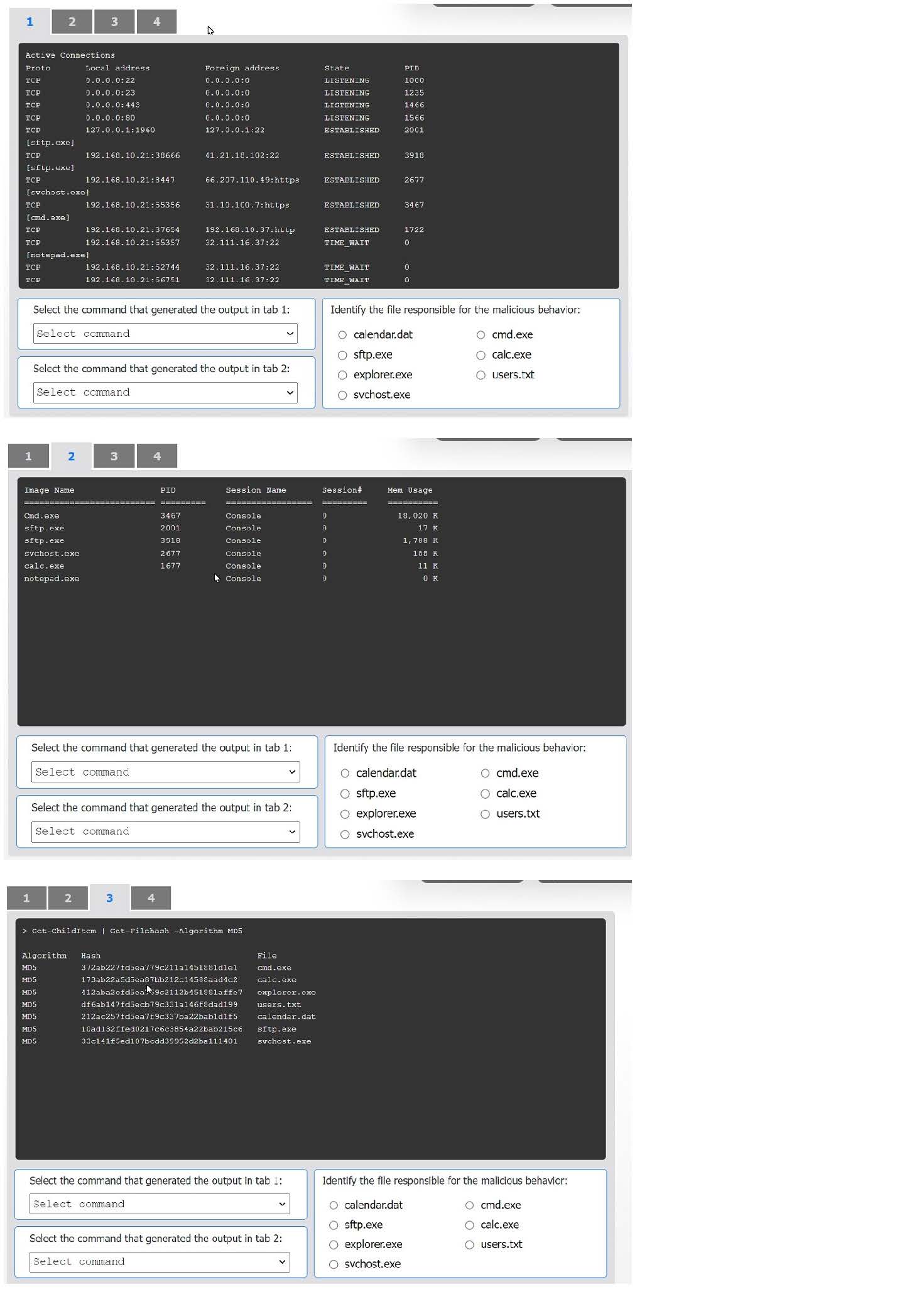
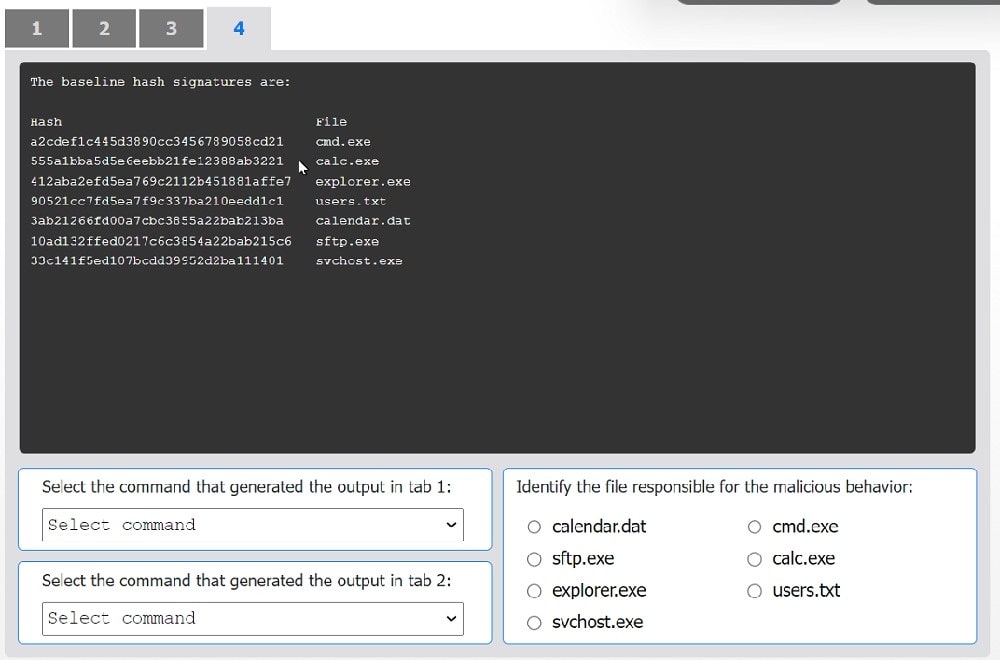
Hot Area:
-
Question 135:
A small company does no! have enough staff to effectively segregate duties to prevent error and fraud in payroll management. The Chief Information Security Officer (CISO) decides to maintain and review logs and audit trails to mitigate risk. Which of the following did the CISO implement?
A. Corrective controls
B. Compensating controls
C. Operational controls
D. Administrative controls
-
Question 136:
Which of the following is the most important reason for an incident response team to develop a formal incident declaration?
A. To require that an incident be reported through the proper channels
B. To identify and document staff who have the authority to declare an incident
C. To allow for public disclosure of a security event impacting the organization
D. To establish the department that is responsible for responding to an incident
-
Question 137:
After updating the email client to the latest patch, only about 15% of the workforce is able to use email. Windows 10 users do not experience issues, but Windows 11 users have constant issues. Which of the following did the change management team fail to do?
A. Implementation
B. Testing
C. Rollback
D. Validation
-
Question 138:
When undertaking a cloud migration of multiple SaaS application, an organizations system administrator struggled ... identity and access management to cloud-based assets. Which of the following service models would have reduced the complexity of this project?
A. CASB
B. SASE
C. ZTNA
D. SWG
-
Question 139:
Two employees in the finance department installed a freeware application that contained embedded malware. The network is robustly segmented based on areas of responsibility. These computers had critical sensitive information stored locally that needs to be recovered. The department manager advised all department employees to turn off their computers until the security team could be contacted about the issue. Which of the following is the first step the incident response staff members should take when they arrive?
A. Turn on all systems, scan for infection, and back up data to a USB storage device.
B. Identify and remove the software installed on the impacted systems in the department.
C. Explain that malware cannot truly be removed and then reimage the devices.
D. Log on to the impacted systems with an administrator account that has privileges to perform backups.
E. Segment the entire department from the network and review each computer offline.
-
Question 140:
An organization discovered a data breach that resulted in Pll being released to the public. During the lessons learned review, the panel identified discrepancies regarding who was responsible for external reporting, as well as the timing requirements. Which of the following actions would best address the reporting issue?
A. Creating a playbook denoting specific SLAs and containment actions per incident type
B. Researching federal laws, regulatory compliance requirements, and organizational policies to document specific reporting SLAs
C. Defining which security incidents require external notifications and incident reporting in addition to internal stakeholders
D. Designating specific roles and responsibilities within the security team and stakeholders to streamline tasks
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CS0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.