Exam Details
Exam Code
:CS0-003Exam Name
:CompTIA Cybersecurity Analyst (CySA+)Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:509 Q&AsLast Updated
:Mar 23, 2025
CompTIA CompTIA Certifications CS0-003 Questions & Answers
-
Question 391:
A digital forensics investigator works from duplicate images to preserve the integrity of the original evidence. Which of the following types of media are most volatile and should be preserved? (Select two).
A. Memory cache
B. Registry file
C. SSD storage
D. Temporary filesystems
E. Packet decoding
F. Swap volume
-
Question 392:
A development team recently released a new version of a public-facing website for testing prior to production. The development team is soliciting the help of various teams to validate the functionality of the website due to its high visibility. Which of the following activities best describes the process the development team is initiating?
A. Static analysis
B. Stress testing
C. Code review
D. User acceptance testing
-
Question 393:
A security analyst is trying to identify possible network addresses from different source networks belonging to the same company and region.
Which of the following shell script functions could help achieve the goal?
A. function w() { a=$(ping -c 1 $1 | awk-F "/" 'END{print $1}') andand echo "$1 | $a" }
B. function x() { b=traceroute -m 40 $1 | awk 'END{print $1}') andand echo "$1 | $b" }
C. function y() { dig $(dig -x $1 | grep PTR | tail -n 1 | awk -F ".in-addr" '{print $1}').origin.asn.cymru.com TXT +short }
D. function z() { c=$(geoiplookup$1) andand echo "$1 | $c" }
-
Question 394:
A security analyst is writing a shell script to identify IP addresses from the same country. Which of the following functions would help the analyst achieve the objective?
A. function w() { info=$(ping -c 1 $1 | awk -F "/" `END{print $1}') andand echo "$1 | $info" }
B. function x() { info=$(geoiplookup $1) andand echo "$1 | $info" }
C. function y() { info=$(dig -x $1 | grep PTR | tail -n 1 ) andand echo "$1 | $info" }
D. function z() { info=$(traceroute -m 40 $1 | awk `END{print $1}') andand echo "$1 | $info" }
-
Question 395:
A security analyst obtained the following table of results from a recent vulnerability assessment that was conducted against a single web server in the environment:
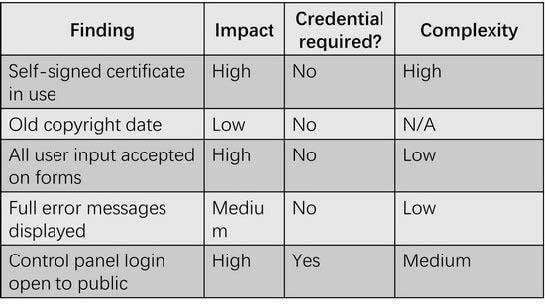
Which of the following should be completed first to remediate the findings?
A. Ask the web development team to update the page contents B. Add the IP address allow listing for control panel access
C. Purchase an appropriate certificate from a trusted root CA
D. Perform proper sanitization on all fields
-
Question 396:
A user reports a malware alert to the help desk. A technician verities the alert, determines the workstation is classified as a low-severity device, and uses network controls to block access. The technician then assigns the ticket to a security analyst who will complete the eradication and recovery processes. Which of the following should the security analyst do next?
A. Document the procedures and walk through the incident training guide.
B. Reverse engineer the malware to determine its purpose and risk to the organization.
C. Sanitize the workstation and verify countermeasures are restored.
D. Isolate the workstation and issue a new computer to the user.
-
Question 397:
An organization has activated the CSIRT. A security analyst believes a single virtual server was compromised and immediately isolated from the network. Which of the following should the CSIRT conduct next?
A. Take a snapshot of the compromised server and verify its integrity
B. Restore the affected server to remove any malware
C. Contact the appropriate government agency to investigate
D. Research the malware strain to perform attribution
-
Question 398:
During an incident, an analyst needs to acquire evidence for later investigation. Which of the following must be collected first in a computer system, related to its volatility level?
A. Disk contents
B. Backup data
C. Temporary files
D. Running processes
-
Question 399:
A user downloads software that contains malware onto a computer that eventually infects numerous other systems. Which of the following has the user become?
A. Hacklivist
B. Advanced persistent threat
C. Insider threat
D. Script kiddie
-
Question 400:
A vulnerability management team is unable to patch all vulnerabilities found during their weekly scans. Using the third-party scoring system described below, the team patches the most urgent vulnerabilities:
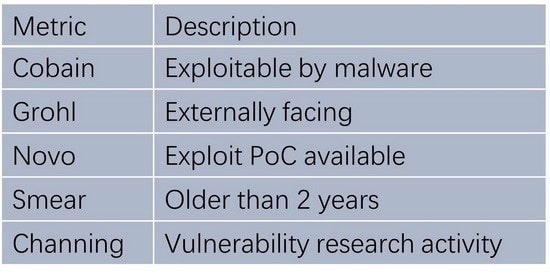
Additionally, the vulnerability management team feels that the metrics Smear and Channing are less important than the others, so these will be lower in priority. Which of the following vulnerabilities should be patched first, given the above third-party scoring system?
A. InLoud: Cobain: Yes Grohl: No Novo: Yes Smear: Yes
Channing: No
B. TSpirit: Cobain: Yes Grohl: Yes Novo: Yes Smear: No Channing: No
C. ENameless: Cobain: Yes Grohl: No Novo: Yes Smear: No Channing: No
D. PBleach: Cobain: Yes Grohl: No Novo: No Smear: No Channing: Yes
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CS0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.